The prolific Iranian country-point out group acknowledged as Charming Kitten qualified numerous victims in the U.S., Europe, the Middle East and India with a novel malware dubbed BellaCiao, adding to its at any time-growing checklist of tailor made instruments.
Found by Bitdefender Labs, BellaCiao is a “customized dropper” which is able of offering other malware payloads on to a sufferer machine based on commands gained from an actor-managed server.
“Each and every sample collected was tied up to a unique victim and provided tough-coded facts these kinds of as enterprise identify, specifically crafted subdomains, or connected general public IP address,” the Romanian cybersecurity organization said in a report shared with The Hacker News.
Charming Kitten, also identified as APT35, Cobalt Illusion, Educated Manticore, ITG18, Mint Sandstorm (née Phosphorus), TA453, and Yellow Garuda, is an Iranian condition-sponsored APT group associated with the Islamic Innovative Guard Corps (IRGC).
Above the yrs, the team has utilized numerous usually means to deploy backdoors in devices belonging to a wide range of field verticals.
The growth will come as the threat actor was attributed by Microsoft to retaliatory attacks aimed at critical infrastructure entities in the U.S. amongst late 2021 to mid-2022 applying bespoke malware such as harmPower, Drokbk, and Soldier.
Then before this week, Test Level disclosed Mint Sandstorm’s use of an updated version of the PowerLess implant to strike organizations situated in Israel employing Iraq-themed phishing lures.
“Custom made-made malware, also acknowledged as ‘tailored’ malware, is commonly more difficult to detect for the reason that it is particularly crafted to evade detection and includes distinctive code,” Bitdefender researcher Martin Zugec observed.
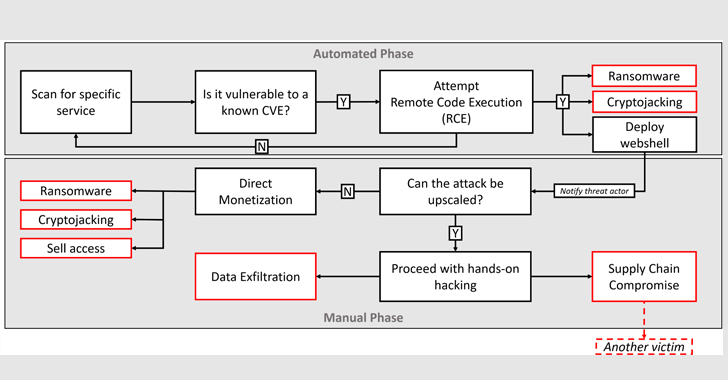
The exact modus operandi used to reach first intrusion is currently undetermined, despite the fact that it can be suspected to entail the exploitation of recognized vulnerabilities in internet-exposed apps like Microsoft Trade Server or Zoho ManageEngine.
A successful breach is followed by the danger actor trying to disable Microsoft Defender applying a PowerShell command and establishing persistence on the host by means of a provider instance.
Bitdefender stated it also noticed Charming Kitten downloading two Internet Information Products and services (IIS) modules able of processing incoming directions and exfiltrating credentials.
Upcoming WEBINARZero Have confidence in + Deception: Learn How to Outsmart Attackers!
Find how Deception can detect advanced threats, stop lateral movement, and increase your Zero Rely on technique. Sign up for our insightful webinar!
Conserve My Seat!
BellaCiao, for its aspect, is also noteworthy for performing a DNS request every 24 several hours to solve a subdomain to an IP handle that’s subsequently parsed to extract the commands to be executed on the compromised method.
“The settled IP deal with is like the actual community IP deal with, but with slight modifications that allow BellaCiao to obtain even further instructions,” Zugec defined.
Based on the solved IP deal with, the attack chain qualified prospects to the deployment of a web shell that supports the ability to upload and download arbitrary documents as perfectly as run instructions.
Also spotted is a next variant of BellaCiao that substitutes the web shell for a Plink software – a command-line utility for PuTTY – which is developed to establish a reverse proxy relationship to a distant server and implements comparable backdoor functions.
“The greatest safety against modern attacks requires implementing a defense-in-depth architecture,” Zugec concluded. “The initial phase in this procedure is to decrease the attack surface area, which consists of restricting the variety of entry details that attackers can use to obtain entry to your methods and prompt patching of newly uncovered vulnerabilities.”
Located this article intriguing? Observe us on Twitter and LinkedIn to go through extra distinctive information we put up.
Some parts of this article are sourced from:
thehackernews.com

 Chinese Hackers Using MgBot Malware to Target International NGOs in Mainland China
Chinese Hackers Using MgBot Malware to Target International NGOs in Mainland China