Specifics have emerged about a large-severity security vulnerability impacting Service Site Protocol (SLP) that could be weaponized to launch volumetric denial-of-services assaults against targets.
“Attackers exploiting this vulnerability could leverage susceptible instances to launch huge Denial-of-Provider (DoS) amplification attacks with a aspect as significant as 2200 times, likely building it just one of the most significant amplification assaults ever claimed,” Bitsight and Curesec scientists Pedro Umbelino and Marco Lux claimed in a report shared with The Hacker Information.
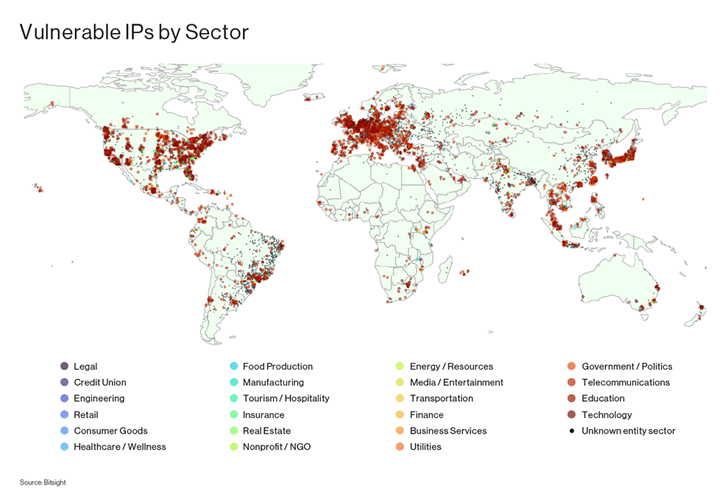
The vulnerability, which has been assigned the identifier CVE-2023-29552 (CVSS rating: 8.6), is stated to impression far more than 2,000 worldwide businesses and more than 54,000 SLP cases that are accessible about the internet.
This features VMWare ESXi Hypervisor, Konica Minolta printers, Planex Routers, IBM Built-in Administration Module (IMM), SMC IPMI, and 665 other products styles.
The best 10 countries with the most organizations acquiring vulnerable SLP occasions are the U.S., the U.K., Japan, Germany, Canada, France, Italy, Brazil, the Netherlands, and Spain.
SLP is a assistance discovery protocol that can make it doable for pcs and other products to uncover companies in a local region network these types of as printers, file servers, and other network means.
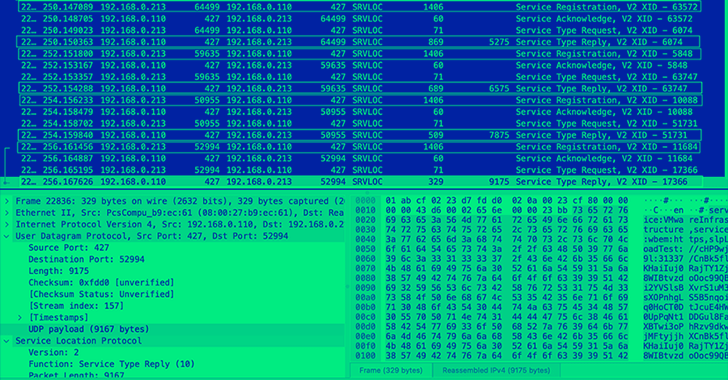
Thriving exploitation of CVE-2023-29552 could allow for permit an attacker to consider gain of susceptible SLP scenarios to start a reflection amplification attack and overwhelm a target server with bogus site visitors.
To do so, all an attacker desires to do is come across an SLP server on UDP port 427 and sign-up “products and services right up until SLP denies far more entries,” adopted by frequently spoofing a ask for to that service with a victim’s IP as the source address.
Future WEBINARZero Belief + Deception: Master How to Outsmart Attackers!
Learn how Deception can detect superior threats, cease lateral motion, and increase your Zero Believe in strategy. Join our insightful webinar!
Save My Seat!
An attack of this variety can generate an amplification element of up to 2,200, ensuing in huge-scale DoS attacks. To mitigate towards the risk, end users are proposed to disable SLP on methods instantly related to the internet, or alternatively filter traffic on UDP and TCP port 427.
“It is similarly essential to enforce solid authentication and entry controls, allowing for only licensed customers to obtain the correct network methods, with accessibility being intently monitored and audited,” the scientists said.
Web security company Cloudflare, in an advisory, explained it “expects the prevalence of SLP-centered DDoS assaults to increase appreciably in the coming weeks” as menace actors experiment with the new DDoS amplification vector.
The conclusions appear as a now-patched two-yr-aged flaw in VMware’s SLP implementation was exploited by actors associated with the ESXiArgs ransomware in popular assaults earlier this yr.
Located this write-up appealing? Stick to us on Twitter and LinkedIn to study much more exclusive written content we submit.
Some parts of this article are sourced from:
thehackernews.com

 Iranian Hackers Launch Sophisticated Attacks Targeting Israel with PowerLess Backdoor
Iranian Hackers Launch Sophisticated Attacks Targeting Israel with PowerLess Backdoor