Disclaimer: This posting is meant to give insight into cyber threats as observed by the group of people of CrowdSec.
What can tens of 1000’s of machines explain to us about unlawful hacker actions?
Do you bear in mind that scene in Batman – The Dark Knight, exactly where Batman works by using a program that aggregates energetic audio information from many cellular telephones to produce a meta sonar feed of what is likely on at any supplied area?
It is an exciting analogy with what we do at CrowdSec. By aggregating intrusion indicators from our local community, we can present a crystal clear image of what is likely on in terms of unlawful hacking in the globe.
After 2 yrs of exercise and analyzing 1 million intrusion signals daily from tens of thousands of users in 160 international locations, we get started possessing an correct “Batman sonar” world wide feed of cyber threats. And there are some interesting takeaways to outline.
A cyber menace with a lot of faces
To start with of all, the global cyber risk is highly flexible. What do we see when searching at the styles of assaults noted, their origin, and the Autonomous Devices (AS) driving the destructive IP addresses?
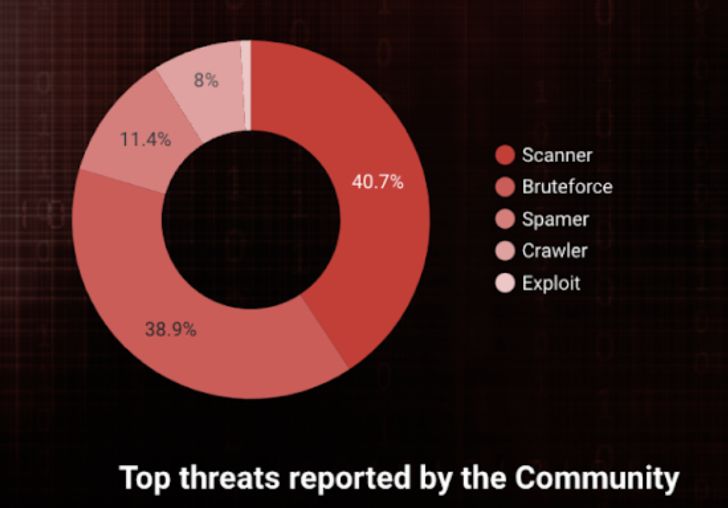
Scanners and Brute force tries are continue to the most common intrusion vectors our local community sees and rank #1. Really logic, as surveillance is the very first action to a far more state-of-the-art intrusion. The scanning things to do observed by our group are generally port scans or HTTP-based mostly probings.
Amongst the various intrusion varieties applied by hackers, brute force makes an attempt on sensitive providers (SSH, email, admin URLs, etc.) is #2. Not breakthrough data, but when studies show that brute force attacks are accounted for 6% of cyber assaults in the entire world, it is not surprising to see it as dominant, especially given that it is however one of the least complicated and lowest priced types to automate and deploy (howdy script kiddies). Due to the fact it is very straightforward to counter, 1 would feel it seldom is effective, but hey, 6%!
Log4J is however not still a finished offer
Among the most popular exploit makes an attempt our community sees, we have Log4j. You certainly relished past year’s storm on how a basic open-resource logging utility for Apache with a vulnerability took around the cybersecurity earth and brought on countless problems to cybersecurity professionals. And, of study course, the felony environment was far more than joyful to exploit it with automated scanning bots hunting for vulnerable solutions.
Well, our local community has witnessed the storm. When the December peak next the disclosure handed, points calmed down a tiny bit, but scanning functions for Log4j started off again, whilst at a lessen but regular degree, fueled by bots.
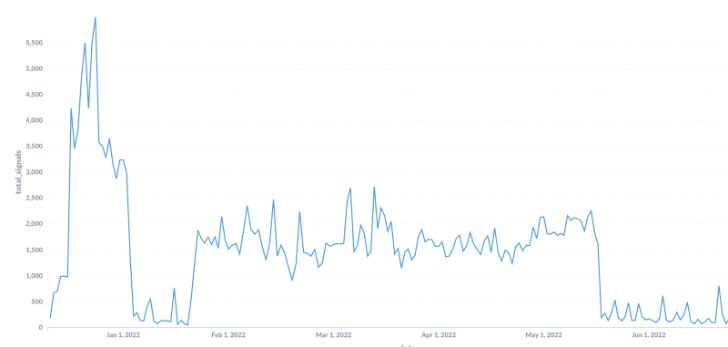
The vital message is that if you think you are guarded due to the fact the “marketing” storm passed, believe 2 times.
There is continue to a very intense activity hunting to use the vulnerability.
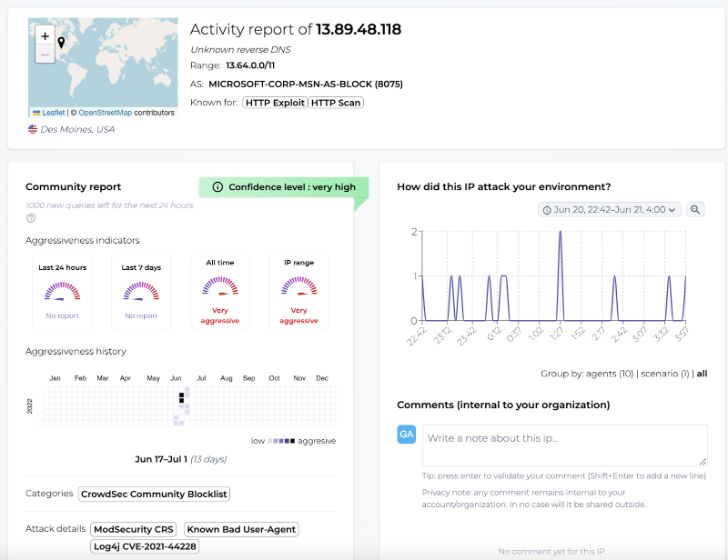
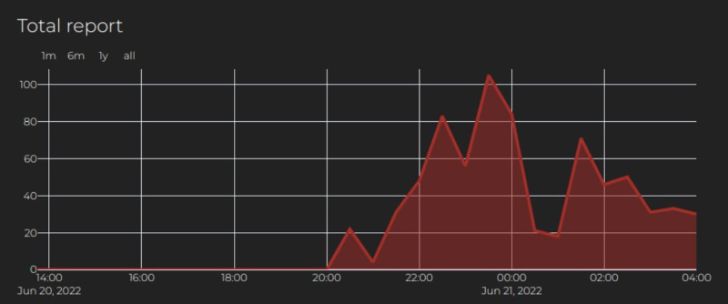
For instance, a few of weeks in the past, a big spectrum of our neighborhood was scanned as the IP address 13.89.48.118 was described by additional than 500 consumers in significantly less than 12 hrs. It joined 20000+ other IP addresses on the neighborhood blocklist for remediation.
IP addresses: cyber criminals’ main source
IP addresses are hardly ever malevolent for good and their reputation can modify from a person working day to a further. With the community continually sharing data on them, any update can be instantaneously transferred to people. In the long operate, it provides invaluable facts on the aggressiveness length of IP addresses.
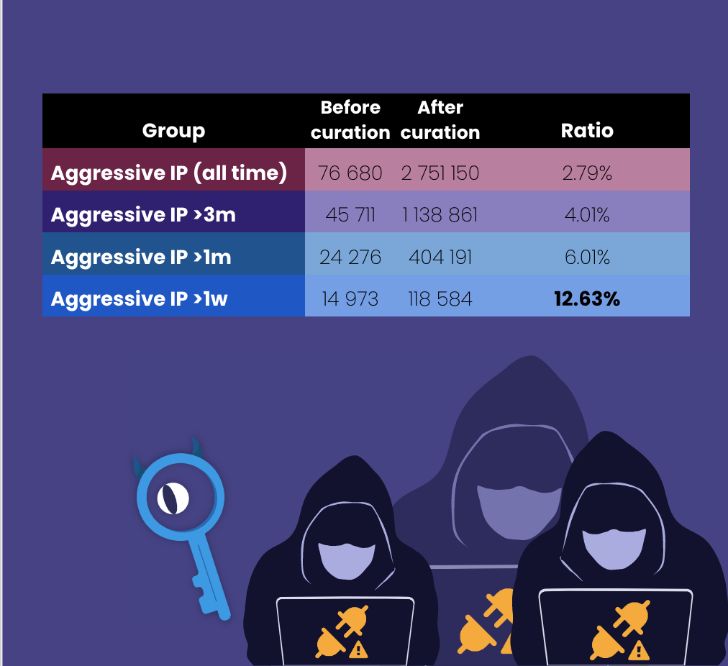
This is a snapshot of the number of IP addresses that landed in the CrowdSec details lakes (flagged as destructive). What is fascinating to be aware is that cybercriminals are in fact transforming the IPs they are employing to commit their attacks:
* only 2,79% of these are long term associates of our databases
* 12,63% of all collected IPs alter every single solitary week
* The day-to-day renewal rate sits at 1.8%
**Autonomous programs have diverse techniques to mitigating compromised IPs**
Each and every IP is aspect of a pool of addresses managed by an AS (Autonomous System). An AS is an substantial network or group of networks that have a unified routing policy. Each individual laptop or computer or product that connects to the Internet is related to an AS. Normally, every AS is operated by a single huge firm, this sort of as an Internet provider company (ISP), a huge business technology enterprise, a college, or a government agency, and is, as this sort of, accountable for the IP addresses.
Every single aggressive IP shared by the CrowdSec neighborhood is enriched by its AS. This, merged with the knowledge on aggressiveness length, can present a crystal clear image of how AS take care of compromised IPs.
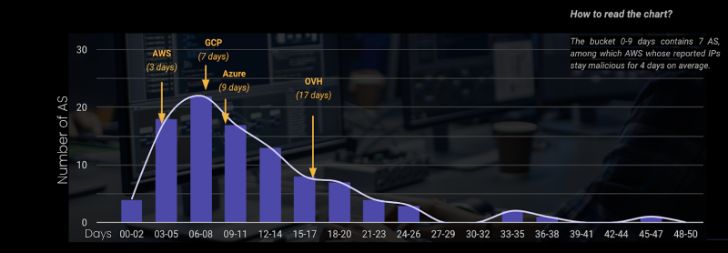
When seeking basically at the amount of compromised belongings could possibly be an angle, it wouldn’t be always good. Not all operators are equal in size, and some are hosting “riskier” providers (hello there outdated PHP CMS) than other folks.
The ordinary malevolent period of all the IPs in the very same AS signifies the operator’s owing diligence in figuring out and working with compromised assets. The distribution of the typical duration is demonstrated with arrows pointing to the situation of the most documented AS for the major cloud vendors. For instance, at AWS, compromised addresses continue being compromised for an regular of 3 days. Azure 9 days. At the finish of the chart, AS from China or Russia (surprise…) “are considerably less quick” to act upon compromised IPs.
This posting is meant to give an overview of the danger action and intelligence CrowdSec buyers see everyday. You should seek advice from the comprehensive model of the report listed here if you want more information.
Discovered this posting intriguing? Adhere to THN on Fb, Twitter and LinkedIn to study extra distinctive content we article.
Some parts of this article are sourced from:
thehackernews.com


 North Korean hackers are using ransomware to attack healthcare providers, feds warn
North Korean hackers are using ransomware to attack healthcare providers, feds warn