Let us face it: we all use email, and we all use passwords. Passwords generate inherent vulnerability in the program. The accomplishment charge of phishing attacks is skyrocketing, and alternatives for the attack have drastically multiplied as life moved on the internet. All it usually takes is just one password to be compromised for all other end users to turn into victims of a facts breach.
To provide additional security, consequently, electronic identities rely on verification plasters. MFA (multi-factor authentication) typically falls back again to expertise variables these types of as password resets and OTP codes, but these are nevertheless vulnerable. As prolonged as credentials can be shared or intercepted, they can be misused.
What is necessary is a paradigm shift – from knowledge-based mostly credentials to strong possession-component security that are unable to be compromised, together with other verification security such as biometrics.
A new possession-component API now aims to do specifically that, changing know-how-based mostly credentials, by using the SIM card for possession issue system binding and user authentication, consequently minimizing the chance of phishing.
Phishing: a human challenge
Phishing and other styles of social engineering rely on the human variable to be the weakest hyperlink in a breach. They make use of the practical, credential-dependent entry afforded to the normal consumer of a platform, by tricking people normal customers into sharing credentials. And it works: 83% of organizations surveyed claimed they professional a prosperous email-based phishing attack in 2021.
Even 2FA codes are now targets
It really is prevalent information that passwords can be shared and, for that reason, simply phished. But a lesser-acknowledged truth is that many kinds of 2FA – this sort of as the OTP or PIN code added in an effort to boost the regarded weaknesses in passwords – are also phishable.
Even even worse, criminals are now targeting these solutions specifically: researchers lately located that more than 1,200 phishing kits intended to steal 2FA codes are out in operation.
The respond to to identity and obtain management, hence, is not to apply extra patches that kill the consumer experience, as these don’t genuinely keep attackers out. Instead, MFA wants a more robust, easier possession variable – with practically nothing to type, meaning very little to phish.
Reason-developed MFA possession aspects involve security dongles or tokens. But they’re costly, and not a little something the regular person will acquire. More robust security for everybody can only function with products that are broadly available, effortless to use, quick to integrate, and price-effective.
Enter the SIM card. It’s inside everyone’s cellular phone, and is crafted on cryptographic security when connecting to cell network authentication.
Now, for the to start with time, an API from tru.ID opens up SIM-dependent cell network authentication to every enterprise and application developer, which means you can leverage the security of the SIM card as a protected possession factor for MFA.
SIM-primarily based authentication: the new phishing-resistant possession aspect
The SIM card has a ton going for it. SIM playing cards use the exact really protected, cryptographic microchip technology that is developed into each individual credit card. It’s tough to clone or tamper with, and there is a SIM card in each mobile phone – so each and every a person of your consumers by now has this hardware in their pocket.
The combination of the cellular phone amount with its associated SIM card id (the IMSI) is a blend that is tricky to phish as it’s a silent authentication examine.
The user working experience is superior too. Mobile networks routinely execute silent checks that a user’s SIM card matches their phone number in order to enable them send messages, make phone calls, and use info – making certain authentic-time authentication without requiring a login.
Until finally lately, it was not feasible for businesses to software the authentication infrastructure of a mobile network into an app as conveniently as any other code. tru.ID would make network authentication accessible to anyone.
Incorporating the tru.ID SDK into current account journeys that use the cellular phone variety immediately enables possession-issue security for each and every user. Additionally, with no extra enter from the user, there’s no attack vector for malicious actors: SIM-based mostly authentication is invisible, so there is certainly no qualifications or codes to steal, intercept or misuse.
tru.ID does not entry the user’s SIM card. As an alternative, it verifies SIM card status instantly with the cell operator in actual-time. It checks that a phone number has not been assigned to a different SIM and for new SIM changes, assisting to avoid SIM swap fraud.
An instance situation to enable SIM-dependent verification
Even even though there are a quantity of procedures described in the state of affairs down below, the finish user of the technique has to do only just one thing – supply their cell phone number.
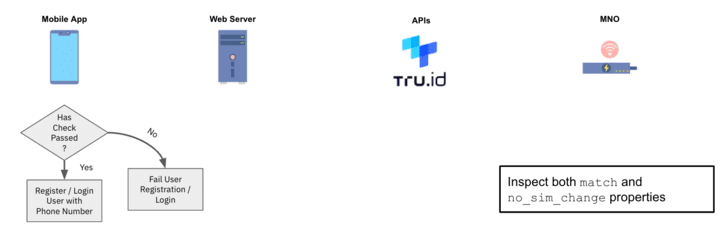
1 — After the consumer delivers their mobile selection, the tru.ID API performs a lookup for the phone variety to decide which cellular network operator (MNO) it is assigned to.
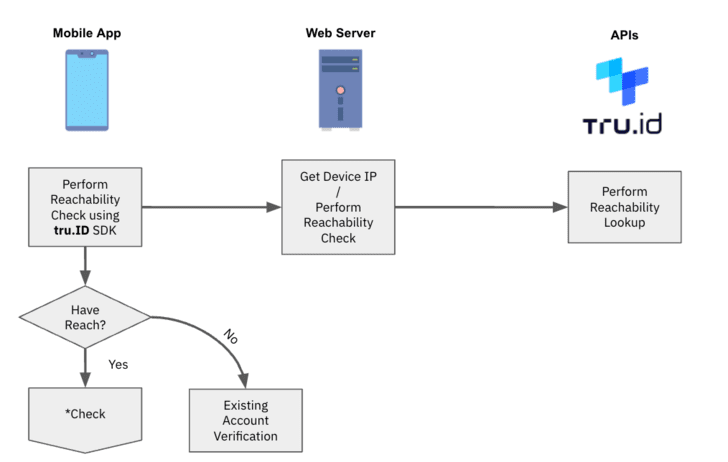
2 — tru.ID requests from the MNO a exceptional Test URL to commence the cell authentication workflow.
3 — tru.ID stores the MNO’s Check out URL, and returns a tru.ID Verify URL to your web server for the cellular unit to open up.
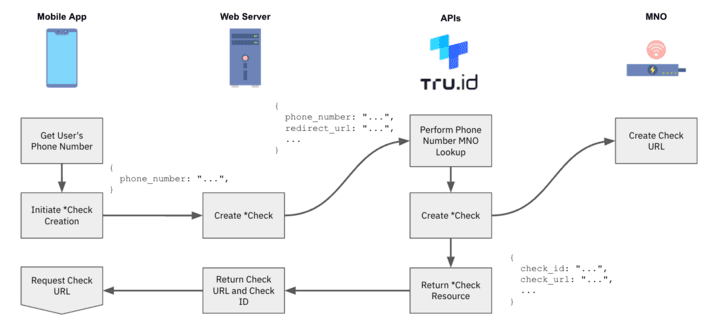
4 — The cellular software opens the tru.ID Test URL. It is most well-liked to use tru.ID SDKs for this for the reason that it forces the web request to be in excess of a cell knowledge session.
5 — The MNO will get the web ask for by way of a redirect from the tru.ID system.
6 — The last redirect can take the machine to the web server’s redirect url endpoint. The overall body of this request will comprise a ‘code’ and the ‘check_id’, and the web server submits this code to tru. ID’s API to finish the SubscriberCheck method.
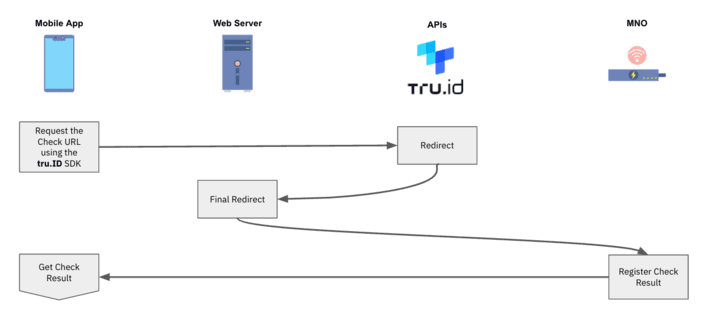
7 — The MNO then establishes if the phone variety related with the authenticated mobile facts session matches the phone range linked with the requested Look at URL. If it does, then the phone variety has been productively verified.
8 — tru.ID performs a SIM card look up and shops the outcome of its position.
9 — On completion of the Check out URL ask for, and when the SIM card standing has been retrieved, the mobile application can ask for the result of the phone verification from the tru.ID API.
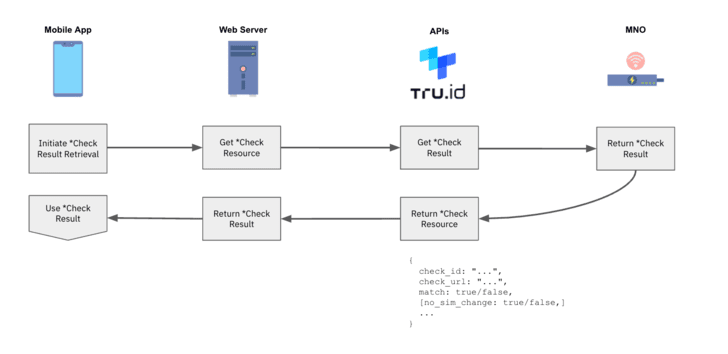
10 — Use the phone verification match and SIM card change `no_sim_change` attributes within just your application logic.
How to get started off
With tru. ID’s developer platform, you can start out screening SIM-centered authentication suitable away, for free of charge, and make your initially API contact inside of minutes.
To come across out how subsequent-gen authentication can produce higher security, low friction authentication ordeals to your people, simply just e-book a free demo or stop by tru.ID.
Uncovered this posting appealing? Comply with THN on Facebook, Twitter and LinkedIn to study far more exceptional content material we article.
Some parts of this article are sourced from:
thehackernews.com


 New Chaos Ransomware Builder Variant “Yashma” Discovered in the Wild
New Chaos Ransomware Builder Variant “Yashma” Discovered in the Wild