The U.S. Federal Bureau of Investigation (FBI) and the Cybersecurity and Infrastructure Security Company (CISA) are warning of active exploitation of a newly patched flaw in Zoho’s ManageEngine ServiceDesk Moreover item to deploy web shells and carry out an array of malicious things to do.
Tracked as CVE-2021-44077 (CVSS score: 9.8), the issue relates to an unauthenticated, remote code execution vulnerability impacting ServiceDesk Plus versions up to, and such as, 11305 that if still left unfixed “enables an attacker to upload executable documents and place web shells that help post-exploitation functions, these as compromising administrator qualifications, conducting lateral motion, and exfiltrating registry hives and Energetic Listing files,” CISA said.

“A security misconfiguration in ServiceDesk Additionally led to the vulnerability,” Zoho noted in an independent advisory published on November 22. “This vulnerability can allow for an adversary to execute arbitrary code and carry out any subsequent attacks.” Zoho dealt with the similar flaw in variations 11306 and previously mentioned on September 16, 2021.
CVE-2021-44077 is also the second flaw to be exploited by the same risk actor that was formerly uncovered exploiting a security shortcoming in Zoho’s self-service password administration and one signal-on option identified as ManageEngine ADSelfService Additionally (CVE-2021-40539) to compromise at least 11 corporations, according to a new report published by Palo Alto Networks’ Device 42 threat intelligence crew.
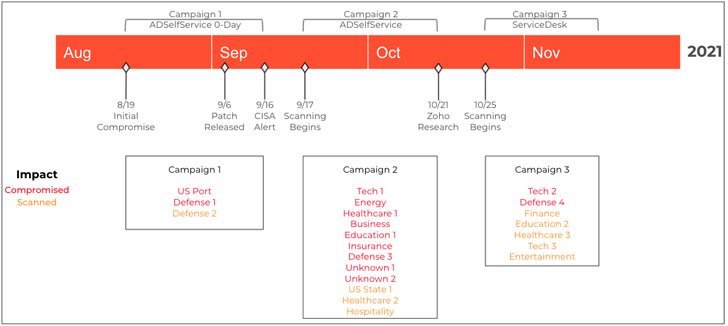
“The threat actor broaden[ed] its target beyond ADSelfService Moreover to other vulnerable software program,” Device 42 researchers Robert Falcone and Peter Renals mentioned. “Most notably, involving Oct 25 and November 8, the actor shifted attention to quite a few companies jogging a diverse Zoho solution regarded as ManageEngine ServiceDesk Plus.”
The assaults are considered to be orchestrated by a “persistent and decided APT actor” tracked by Microsoft less than the moniker “DEV-0322,” an rising danger cluster that the tech giant states is running out of China and has been previously observed exploiting a then zero-day flaw in SolarWinds Serv-U managed file transfer company previously this calendar year. Device 42 is checking the mixed activity as the “TiltedTemple” marketing campaign.

Write-up-exploitation activities following a prosperous compromise require the actor uploading a new dropper (“msiexec.exe”) to sufferer methods, which then deploys the Chinese-language JSP web shell named “Godzilla” for setting up persistence in those people equipment, echoing equivalent techniques made use of versus the ADSelfService software package.
Unit 42 identified that there are now in excess of 4,700 internet-facing situations of ServiceDesk Additionally globally, of which 2,900 (or 62%) spanning across the U.S., India, Russia, Terrific Britain, and Turkey are assessed to be susceptible to exploitation.
Above the earlier three months, at the very least two organizations have been compromised utilizing the ManageEngine ServiceDesk Plus flaw, a selection that’s predicted to climb even more as the APT team ramps up its reconnaissance actions in opposition to technology, electricity, transportation, health care, education, finance, and protection industries.
Zoho, for its portion, has produced out there an exploit detection device to assist buyers establish whether their on-premises installations have been compromised, in addition to recommending that customers “improve to the newest model of ServiceDesk Plus (12001) promptly” to mitigate any potential risk arising of exploitation.
Uncovered this article appealing? Observe THN on Facebook, Twitter and LinkedIn to browse extra exceptional information we put up.
Some parts of this article are sourced from:
thehackernews.com


 New holographic camera sees the unseen with high precision
New holographic camera sees the unseen with high precision