A new exploration has yielded nonetheless an additional implies to pilfer sensitive information by exploiting what is the initial “on-chip, cross-core” side-channel in Intel Espresso Lake and Skylake processors.
Released by a team of lecturers from the University of Illinois at Urbana-Champaign, the results are predicted to be presented at the USENIX Security Symposium coming this August.
Though info leakage attacks focusing on the CPU microarchitecture have been formerly shown to break the isolation concerning consumer applications and the running method, permitting a malicious system to access memory utilized by other programs (e.g., Meltdown and Spectre), the new attack leverages a competition on the ring interconnect.
SoC Ring interconnect is an on-die bus organized in a ring topology which allows intra-process communication amongst different factors (aka agents) these types of as the cores, the very last amount cache (LLC), the graphics unit, and the method agent that are housed inside of the CPU. Each individual ring agent communicates with the ring through what’s called a ring halt.
To achieve this, the researchers reverse-engineered the ring interconnect’s protocols to uncover the circumstances for two or extra procedures to induce a ring contention, in turn using them to create a covert channel with a capability of 4.18 Mbps, which the scientists say is the major to day for cross-main channels not relying on shared memory, unlike Flush+Flush or Flush+Reload.
“Importantly, as opposed to prior attacks, our assaults do not rely on sharing memory, cache sets, core-private resources or any unique uncore constructions,” Riccardo Paccagnella, a single of the authors of the research, said. “As a consequence, they are really hard to mitigate working with current ‘domain isolation’ approaches.”
Observing that a ring end generally prioritizes targeted visitors that is previously on the ring above new targeted traffic moving into from its brokers, the scientists reported a competition occurs when existing on-ring traffic delays the injection of new ring targeted traffic.
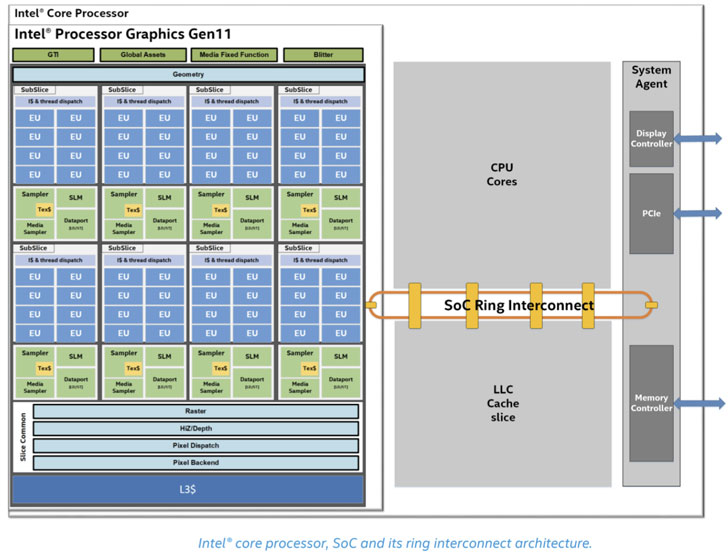
Armed with this information, an adversary can measure the delay in memory obtain connected with a destructive course of action because of to a saturation of bandwidth capability brought on by a target process’ memory accesses. This, nevertheless, necessitates that the spy course of action continually has a skip in its private caches (L1-L2) and performs loads from a concentrate on LLC slice.
In doing so, the repeated latency in memory hundreds from LLC owing to ring competition can permit an attacker to use the measurements as a aspect-channel to leak critical bits from susceptible EdDSA, and RSA implementations as properly as reconstruct passwords by extracting the exact timing of keystrokes typed by a victim user.
Particularly, “an attacker with expertise of our reverse engineering initiatives can set alone up in such a way that its loads are guaranteed to contend with the to start with process’ loads, […] abuses mitigations to preemptive scheduling cache attacks to induce the victim’s loads to miss out on in the cache, displays ring rivalry although the sufferer is computing, and employs a normal device learning classifier to de-sound traces and leak bits.”
The research also marks the initially time a rivalry-centered microarchitectural channel has been exploited for keystroke timing attacks to infer delicate info typed by the target.
In reaction to the disclosures, Intel categorized the attacks as a “traditional facet channel,” which refers to a course of oracle assaults that ordinarily consider edge of the variations in execution timing to infer strategies.
The chipmaker’s recommendations for countering timing attacks versus cryptographic implementations endorse adhering to continuous time programming principles by ensuring that —
- Runtime is unbiased of top secret values
- The get in which the guidance are executed (aka code access styles) are impartial of solution values, and
- The buy in which memory operands are loaded and stored (data access designs) are unbiased of key values
Supplemental steerage on harmless advancement practices to mitigate common side-channel assaults can be uncovered right here. The supply code to reproduce the experimental setup specific in the paper can be accessed right here.
Identified this article interesting? Stick to THN on Facebook, Twitter and LinkedIn to read additional distinctive content we post.
Some parts of this article are sourced from:
thehackernews.com

 Porsche's luxury electric bikes are coming out this spring
Porsche's luxury electric bikes are coming out this spring