Google Task Zero on Thursday disclosed aspects of a new security mechanism that Apple quietly extra to iOS 14 as a countermeasure to avert attacks that ended up lately observed to leverage zero-times in its messaging application.
Dubbed “BlastDoor,” the enhanced sandbox procedure for iMessage details was disclosed by Samuel Groß, a security researcher with Challenge Zero, a group of security scientists at Google tasked with researching zero-working day vulnerabilities in hardware and application units.
“Just one of the significant changes in iOS 14 is the introduction of a new, tightly sandboxed ‘BlastDoor’ provider which is now responsible for virtually all parsing of untrusted information in iMessages,” Groß said. “Additionally, this services is penned in Swift, a (typically) memory risk-free language which makes it appreciably more challenging to introduce classic memory corruption vulnerabilities into the code base.”

The growth is a consequence of a zero-simply click exploit that leveraged an Apple iMessage flaw in iOS 13.5.1 to get around security protections as element of a cyberespionage campaign focusing on Al Jazeera journalists final year.
“We do not imagine that [the exploit] works towards iOS 14 and higher than, which includes new security protections,” Citizen Lab scientists who disclosed the attack final thirty day period.
BlastDoor types the main of all those new security protections, for each Groß, who analyzed the applied adjustments over the study course of a week-long reverse engineering job utilizing an M1 Mac Mini operating macOS 11.1 and an iPhone XS running iOS 14.3.
When an incoming iMessage comes, the information passes by way of a amount of services, chief between them getting the Apple Push Notification Assistance daemon (apsd) and a history approach named imagent, which is not only liable for decoding the message contents but also for downloading attachments (by way of a independent assistance termed IMTransferAgent) and handling inbound links to internet sites, ahead of alerting the SpringBoard to exhibit the notification.
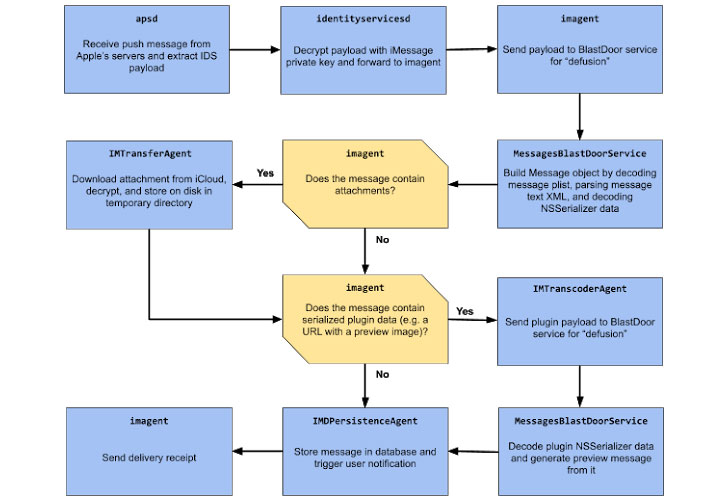
What BlastDoor does is examine all these types of inbound messages in a protected, sandboxed surroundings, which helps prevent any destructive code within of a information from interacting with the rest of the working procedure or accessing consumer info.
Put in different ways, by moving a vast majority of the processing duties — i.e., decoding the information property checklist and generating url previews — from imagent to this new BlastDoor element, a specially-crafted concept sent to a target can no for a longer time interact with the file system or carry out network operations.
“The sandbox profile is fairly tight,” Groß mentioned. “Only a handful of community IPC companies can be achieved, just about all file program conversation is blocked, any conversation with IOKit motorists is forbidden, [and] outbound network access is denied.”
What is a lot more, in a bid to hold off subsequent restarts of a crashing service, Apple has also released a new throttling element in the iOS “launchd” method to limit the variety of attempts an attacker receives when seeking to exploit a flaw by exponentially expanding the time between two successive brute-force tries.
“With this improve, an exploit that relied on continuously crashing the attacked support would now probable involve in the order of multiple hrs to roughly 50 percent a working day to total alternatively of a few minutes,” Groß explained.
“All round, these variations are possibly very close to the most effective that could’ve been carried out presented the need for backwards compatibility, and they must have a considerable influence on the security of iMessage and the platform as a entire.”
Uncovered this posting fascinating? Comply with THN on Facebook, Twitter and LinkedIn to browse a lot more special written content we article.
Some parts of this article are sourced from:
thehackernews.com


 Watch how the new Samsung Galaxy S21 ringtone “Over the Horizon” was made
Watch how the new Samsung Galaxy S21 ringtone “Over the Horizon” was made