Cybersecurity scientists have identified an updated version of an Android banking trojan called Medusa that has been utilised to target buyers in Canada, France, Italy, Spain, Turkey, the U.K., and the U.S.
The new fraud strategies, observed in May 2024 and energetic because July 2023, manifested by way of 5 distinct botnets operated by several affiliates, cybersecurity business Cleafy stated in an investigation revealed last 7 days.
The new Medusa samples characteristic a “lightweight authorization established and new features, these kinds of as the potential to screen a full-display screen overlay and remotely uninstall apps,” security researchers Simone Mattia and Federico Valentini explained.
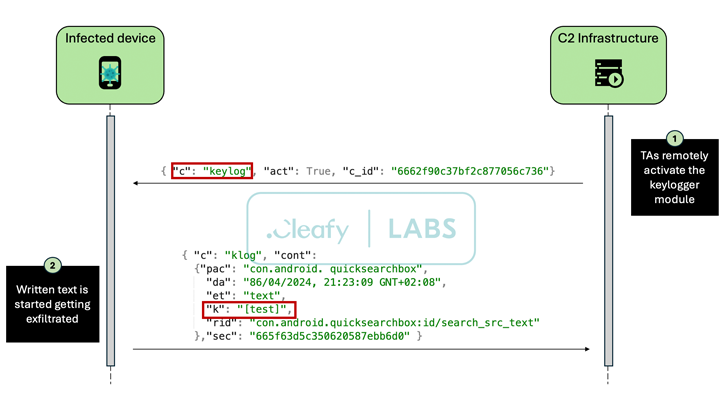
Medusa, also known as TangleBot, is a innovative Android malware to start with uncovered in July 2020 focusing on fiscal entities in Turkey. It arrives with abilities to study SMS messages, log keystrokes, seize screenshots, file calls, share the device display screen in real-time, and execute unauthorized fund transfers employing overlay assaults to steal banking qualifications.
In February 2022, ThreatFabric uncovered Medusa strategies leveraging related delivery mechanisms as that of FluBot (aka Cabassous) by masquerading the malware as seemingly harmless offer supply and utility apps. It is suspected that the threat actors driving the Trojan are from Turkey.
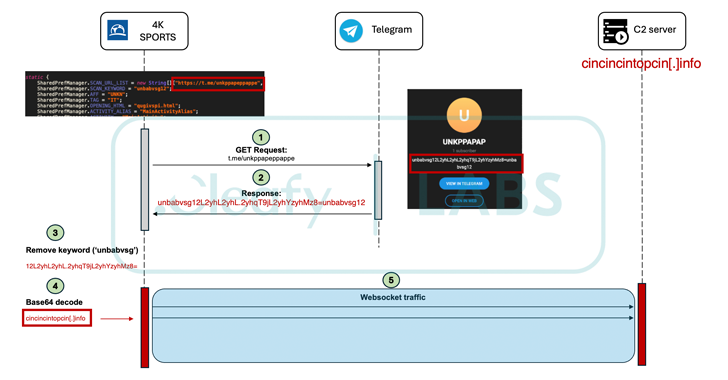
Cleafy’s hottest examination reveals not only advancements to the malware, but also the use of dropper apps to disseminate Medusa beneath the guise of pretend updates. Furthermore, reputable products and services like Telegram and X are made use of as lifeless drop resolvers to retrieve the command-and-management (C2) server utilized for knowledge exfiltration.
A notable modify is the reduction in the quantity of permissions sought in an obvious exertion to decreased the likelihood of detection. That said, it nonetheless necessitates Android’s accessibility expert services API, which will allow it to stealthily enable other permissions as necessary and keep away from increasing consumer suspicion.
A further modification is the ability to set a black display overlay on the victim’s gadget to give the effect that the system is locked or run off and use it as a address to have out malicious things to do.
Medusa botnet clusters commonly rely on tried out-and-examined approaches such as phishing to unfold the malware. Nonetheless, more recent waves have been noticed propagating it by way of dropper apps downloaded from untrusted resources, underscoring continued initiatives on the part of risk actors to evolve their practices.
“Reducing the expected permissions evades detection and seems more benign, enhancing its skill to run undetected for prolonged durations,” the researchers stated. “Geographically, the malware is growing into new regions, these kinds of as Italy and France, indicating a deliberate hard work to diversify its sufferer pool and broaden its attack area.”
The enhancement will come as Symantec exposed that fictitious Chrome browser updates for Android are currently being utilized as a lure to drop the Cerberus banking trojan. Comparable campaigns distributing bogus Telegram applications through phony internet sites (“telegroms[.]icu”) have noticed distributing a different Android malware dubbed SpyMax.
Once installed, the application prompts the person to empower the accessibility products and services, enabling it to obtain keystrokes, specific locations, and even the pace at which the system is shifting. The collected information and facts is then compressed and exported to an encoded C2 server.
“SpyMax is a distant administration tool (RAT) that has the capacity to obtain personalized/non-public data from the contaminated unit without having consent from the consumer and sends the exact to a distant danger actor,” K7 Security Labs claimed. “This enables the danger actors to command victims’ units that impacts the confidentiality and integrity of the victim’s privacy and information.”
Uncovered this article exciting? Comply with us on Twitter and LinkedIn to browse much more distinctive content we write-up.
Some parts of this article are sourced from:
thehackernews.com

 Over 110,000 Websites Affected by Hijacked Polyfill Supply Chain Attack
Over 110,000 Websites Affected by Hijacked Polyfill Supply Chain Attack