A team of researchers has identified a new data leakage attack impacting fashionable CPU architectures supporting speculative execution.
Dubbed GhostRace (CVE-2024-2193), it is a variation of the transient execution CPU vulnerability recognized as Spectre v1 (CVE-2017-5753). The approach brings together speculative execution and race disorders.
“All the common synchronization primitives applied working with conditional branches can be microarchitecturally bypassed on speculative paths applying a department misprediction attack, turning all architecturally race-absolutely free critical areas into Speculative Race Problems (SRCs), permitting attackers to leak facts from the goal,” the scientists mentioned.
The conclusions from the Units Security Investigation Group at IBM Investigation Europe and VUSec, the latter of which disclosed a further side-channel attack called SLAM concentrating on modern-day processors in December 2023.

Spectre refers to a class of side-channel attacks that exploit department prediction and speculative execution on modern CPUs to study privileged information in the memory, bypassing isolation protections concerning purposes.
Even though speculative execution is a performance optimization strategy applied by most CPUs, Spectre assaults choose benefit of the actuality that erroneous predictions leave at the rear of traces of memory accesses or computations in the processor’s caches.
“Spectre attacks induce a target to speculatively execute operations that would not occur through strictly serialized in-purchase processing of the program’s directions, and which leak victim’s confidential details through a covert channel to the adversary,” the researchers at the rear of the Spectre attack pointed out in January 2018.
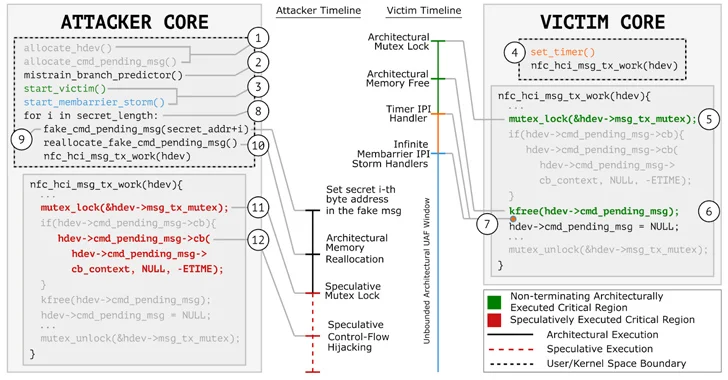
What will make GhostRace noteworthy is that it permits an unauthenticated attacker to extract arbitrary facts from the processor employing race disorders to access the speculative executable code paths by leveraging what’s called a Speculative Concurrent Use-Soon after-Cost-free (SCUAF) attack.
A race condition is an undesirable predicament that takes place when two or a lot more procedures attempt to obtain the exact, shared source without correct synchronization, thereby leading to inconsistent success and opening a window of chance for an attacker to carry out malicious steps.
“In properties and exploitation technique, an SRC vulnerability is identical to a common race situation,” the CERT Coordination Middle (CERT/CC) described in an advisory.
“On the other hand, it is distinctive in that the attacker exploits claimed race situation on a transiently executed path originating from a mis-speculated branch (similar to Spectre v1), concentrating on a racy code snippet or gadget that ultimately discloses info to the attacker.”
The net end result is that it permits an attacker with accessibility to CPU sources to accessibility arbitrary sensitive knowledge from host memory.

“Any software program, e.g., functioning process, hypervisor, etc., implementing synchronization primitives by conditional branches without any serializing instruction on that path and running on any microarchitecture (e.g., x86, ARM, RISC-V, and so forth.), which enables conditional branches to be speculatively executed, is vulnerable to SRCs,” VUSec said.
Subsequent responsible disclosure, AMD stated its present direction for Spectre “remains relevant to mitigate this vulnerability.” The maintainers of the Xen open-resource hypervisor acknowledged that all variations are impacted, whilst they mentioned it can be not likely to pose a critical security menace.
“Out of caution, the Xen Security Staff have supplied hardening patches such as the addition of a new LOCK_HARDEN mechanism on x86 equivalent to the current Branch_HARDEN,” Xen mentioned.
“LOCK_HARDEN is off by default, owing to the uncertainty of there becoming a vulnerability under Xen, and uncertainty more than the general performance affect. Nevertheless, we be expecting extra research to take place in this place, and really feel it is prudent to have a mitigation in place.”
Uncovered this posting interesting? Abide by us on Twitter and LinkedIn to read a lot more special content material we put up.
Some parts of this article are sourced from:
thehackernews.com

 Third-Party ChatGPT Plugins Could Lead to Account Takeovers
Third-Party ChatGPT Plugins Could Lead to Account Takeovers