A new fiscally determined procedure is leveraging a malicious Telegram bot to enable menace actors fraud their victims.
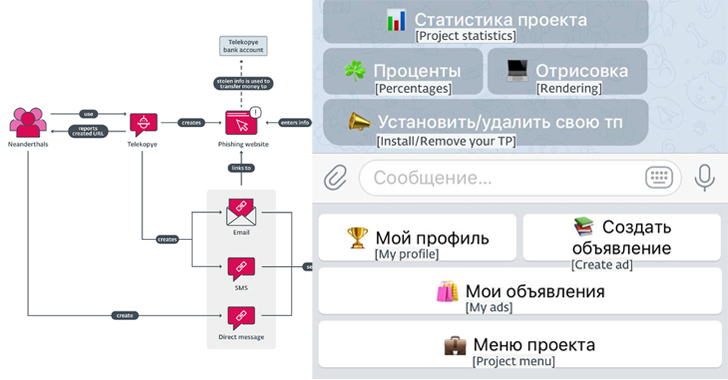
Dubbed Telekopye, a portmanteau of Telegram and kopye (that means “spear” in Russian), the toolkit capabilities as an automated usually means to generate a phishing web site from a premade template and send the URL to potential victims, codenamed Mammoths by the criminals.
“This toolkit is implemented as a Telegram bot that, when activated, provides several quick-to-navigate menus in the kind of clickable buttons that can accommodate many scammers at when,” ESET researcher Radek Jizba mentioned in a report shared with The Hacker News.
The exact origins of the menace actors, dubbed Neanderthals, are unclear, but proof points to Russia as the nation of origin of the toolkit’s authors and customers, owing to the use of Russian SMS templates and the point that a the vast majority of the specific on the web marketplaces are well-liked in the state.
Several variations of Telekopye have been detected to day, the earliest courting all the way back to 2015, suggesting that it can be staying actively taken care of and applied for various many years.
The attack chains move forward hence: Neanderthals discover their Mammoths and attempt to create rapport with them, ahead of sending a bogus website link established using the Telekopye phishing package via email, SMS, or a immediate information.
At the time the payment specifics are entered on the fake credit history/debit card gateway, the information and facts is used to siphon resources from the target, which are then laundered by way of cryptocurrency.
Telekopye is thoroughly-featured, enabling its users to send phishing email messages, produce web internet pages, send out SMS messages, build QR codes, and create convincing images and screenshots of checks and receipts.
The phishing domains applied to host the pages are registered these kinds of that ultimate URL starts with the anticipated brand identify — cdek.id7423[.]ru, olx.id7423[.]ru, and sbazar.id7423[.]ru — in an effort to make them tough to place.
A notable element of the procedure is the centralized nature of the payouts. Relatively than transferring cash stolen from Mammoths to their personal accounts, it can be funneled to a shared account managed by the Telekopye administrator, giving the core workforce an oversight into the operations of each individual Neanderthal.
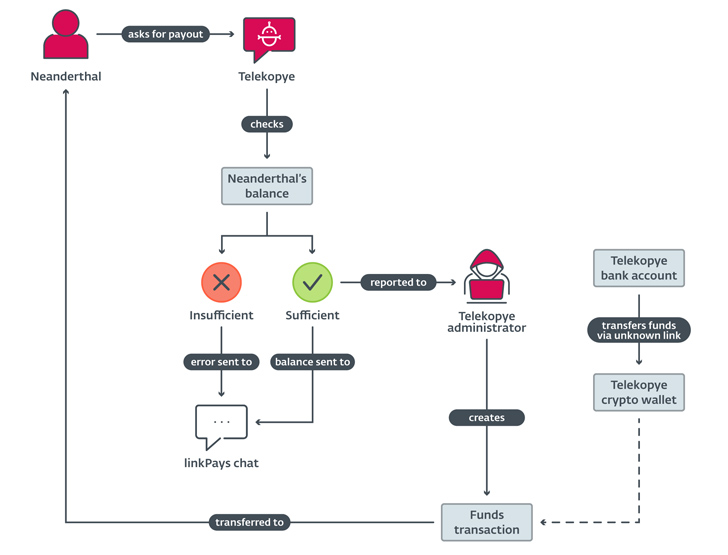
In other words, Neanderthals get compensated by the Telekopye administrator immediately after requesting for a payout as a result of the toolkit alone, but not ahead of a chunk of it is taken as commission service fees to the system operator and the recommender.
“Telekopye checks the Neanderthal’s equilibrium, last request is authorized by the Telekopye administrator and, ultimately, money are transferred to the Neanderthal’s cryptocurrency wallet,” Jizba said.
“In some Telekopye implementations, the very first move, asking for a payout, is automated and the negotiation is initiated each time a Neanderthal reaches a selected threshold of stolen cash from successfully pulled off cons.”

In what is a further more indication of the professionalization of the criminal organization, buyers and operators of Telekopye are organized in a apparent hierarchy spanning roles such as directors, moderators, very good personnel (or support bots), personnel, and blocked.
- Blocked: Users who are prohibited from applying Telekopye for likely breaking the project policies.
- Personnel: A widespread part assigned to all new Neanderthals.
- Excellent workers: An upgrade of the Employee part with a bigger payout and a lower fee service fees.
- Moderators: Consumers who can boost and demote other associates and approve new customers, but can not modify toolkit options.
- Directors: Users with the maximum privileges who can incorporate phishing web webpage templates and change payout fees.
“The simplest way to inform no matter if you are getting targeted by a Neanderthal trying to steal your income is by looking at the language utilized,” Jizba reported. “Insist on in-person cash and items trade every time achievable when dealing with secondhand items on online marketplaces. Keep away from sending funds unless you are sure exactly where it will go.”
Identified this short article fascinating? Stick to us on Twitter and LinkedIn to read more distinctive written content we article.
Some parts of this article are sourced from:
thehackernews.com

 The Hidden Dangers of Public Wi-Fi
The Hidden Dangers of Public Wi-Fi