A new malware strain acknowledged as BundleBot has been stealthily running below the radar by having benefit of .NET one-file deployment techniques, enabling risk actors to seize delicate data from compromised hosts.
“BundleBot is abusing the dotnet bundle (single-file), self-contained format that success in extremely small or no static detection at all,” Examine Place explained in a report released this week, adding it is “normally distributed through Facebook Adverts and compromised accounts main to internet sites masquerading as common method utilities, AI instruments, and online games.”
Some of these internet websites intention to mimic Google Bard, the firm’s conversational generative artificial intelligence chatbot, engaging victims into downloading a bogus RAR archive (“Google_AI.rar”) hosted on legitimate cloud storage solutions these types of as Dropbox.
The archive file, when unpacked, consists of an executable file (“GoogleAI.exe”), which is the .NET solitary-file, self-contained software (“GoogleAI.exe”) that, in turn, incorporates a DLL file (“GoogleAI.dll”), whose obligation is to fetch a password-shielded ZIP archive from Google Drive.
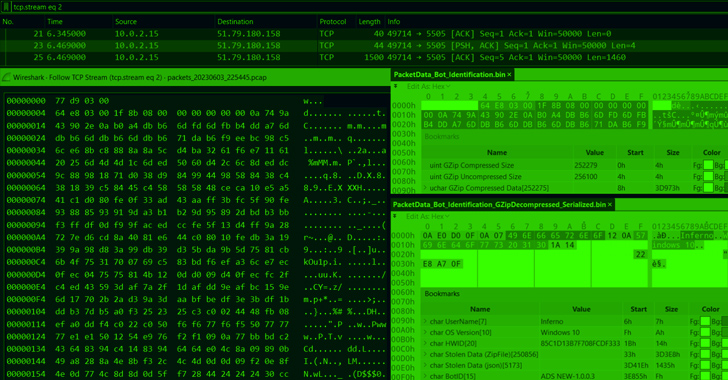
The extracted written content of the ZIP file (“ADSNEW-1…3.zip”) is a different .NET solitary-file, self-contained software (“RiotClientServices.exe”) that incorporates the BundleBot payload (“RiotClientServices.dll”) and a command-and-handle (C2) packet data serializer (“LirarySharing.dll”).
“The assembly RiotClientServices.dll is a personalized, new stealer/bot that makes use of the library LirarySharing.dll to course of action and serialize the packet information that are becoming sent to C2 as a aspect of the bot conversation,” the Israeli cybersecurity company explained.
The binary artifacts employ tailor made-built obfuscation and junk code in a bid to resist examination, and appear with capabilities to siphon information from web browsers, capture screenshots, get Discord tokens, information and facts from Telegram, and Facebook account facts.
Verify Level explained it also detected a 2nd BundleBot sample which is practically equivalent in all elements barring the use of HTTPS to exfiltrate the information to a remote server in the type of a ZIP archive.
“The providing system by means of Facebook Advertisements and compromised accounts is a little something that has been abused by risk actors for a though, nonetheless combining it with a single of the abilities of the unveiled malware (to steal a victim’s Fb account info) could serve as a difficult self-feeding regimen,” the company pointed out.
The advancement comes as Malwarebytes uncovered a new marketing campaign that employs sponsored posts and compromised verified accounts that impersonate Facebook Advertisements Supervisor to entice buyers into downloading rogue Google Chrome extensions that are built to steal Fb login facts.
People who simply click on the embedded url are prompted to download a RAR archive file that contains an MSI installer file that, for its element, launches a batch script to spawn a new Google Chrome window with the destructive extension loaded working with the “–load-extension” flag –
get started chrome.exe –load-extension=”%~dp0/nmmhkkegccagdldgiimedpiccmgmiedagg4″ “https://www.fb.com/enterprise/tools/advertisements-supervisor”
Approaching WEBINARShield Towards Insider Threats: Master SaaS Security Posture Management
Anxious about insider threats? We’ve acquired you included! Be part of this webinar to check out simple methods and the secrets and techniques of proactive security with SaaS Security Posture Administration.
Sign up for Today
“That personalized extension is cleverly disguised as Google Translate and is regarded as ‘Unpacked’ simply because it was loaded from the neighborhood laptop or computer, fairly than the Chrome Web Keep,” Jérôme Segura, director of risk intelligence at Malwarebytes, defined, noting it is “fully focused on Fb and grabbing important pieces of info that could enable an attacker to log into accounts.”
The captured data is subsequently sent using the Google Analytics API to get all-around articles security insurance policies (CSPs) to mitigate cross-web-site scripting (XSS) and details injection assaults.
The danger actors at the rear of the exercise are suspected to be of Vietnamese origin, who have, in recent months, exhibited acute desire in targeting Facebook business and advertising and marketing accounts. Above 800 victims globally have been impacted, with 310 of all those situated in the U.S.
“Fraudsters have a great deal of time on their arms and invest years finding out and knowing how to abuse social media and cloud platforms, the place it is a frequent arm’s race to continue to keep undesirable actors out,” Segura said. “Recall that there is no silver bullet and anything at all that appears as well great to be correct could incredibly nicely be a rip-off in disguise.”
Observed this posting intriguing? Comply with us on Twitter and LinkedIn to read through more distinctive content we article.
Some parts of this article are sourced from:
thehackernews.com

 Local Governments Targeted for Ransomware – How to Prevent Falling Victim
Local Governments Targeted for Ransomware – How to Prevent Falling Victim