Multiple security flaws have been disclosed in Apache OpenMeetings, a web conferencing option, that could be probably exploited by malicious actors to seize manage of admin accounts and run destructive code on inclined servers.
“Attackers can bring the application into an unanticipated condition, which makes it possible for them to consider above any consumer account, which include the admin account,” Sonar vulnerability researcher Stefan Schiller explained in a report shared with The Hacker Information.
“The obtained admin privileges can even further be leveraged to exploit another vulnerability making it possible for attackers to execute arbitrary code on the Apache OpenMeetings server.”
Subsequent accountable disclosure on March 20, 2023, the vulnerabilities were addressed with the release of Openmeetings edition 7.1. that was launched on Might 9, 2023. The checklist of 3 flaws is as follows –
- CVE-2023-28936 (CVSS rating: 5.3) – Insufficient check of invitation hash
- CVE-2023-29032 (CVSS score: 8.1) – An authentication bypass that potential customers to unrestricted accessibility through invitation hash
- CVE-2023-29246 (CVSS rating: 7.2) – A NULL byte (%00) injection that permits an attacker with admin privileges to obtain code execution
Assembly invitations established using OpenMeetings occur are not only certain to a particular room and a consumer but also occur with a one of a kind hash that is utilised by the application to retrieve aspects connected with the invitation.
Upcoming WEBINARShield In opposition to Insider Threats: Learn SaaS Security Posture Management
Apprehensive about insider threats? We have bought you coated! Be a part of this webinar to take a look at sensible approaches and the techniques of proactive security with SaaS Security Posture Administration.
Be part of Currently
The very first two flaws, in a nutshell, have to do with a weak hash comparison among the user-provided hash and what is actually existing in the databases and a quirk that allows for the generation of a area invitation without the need of a space assigned to it, leading to a situation the place an invitation exists with no space hooked up to it.
A menace actor could exploit these shortcomings to develop an celebration and be a part of the corresponding area, and comply with it up by deleting the celebration, at which level an invitation is developed for the admin consumer to the non-current place. In the next action, the weak hash comparison bug could be leveraged to enumerate the despatched invitation and redeem it by delivering a wildcard hash enter.
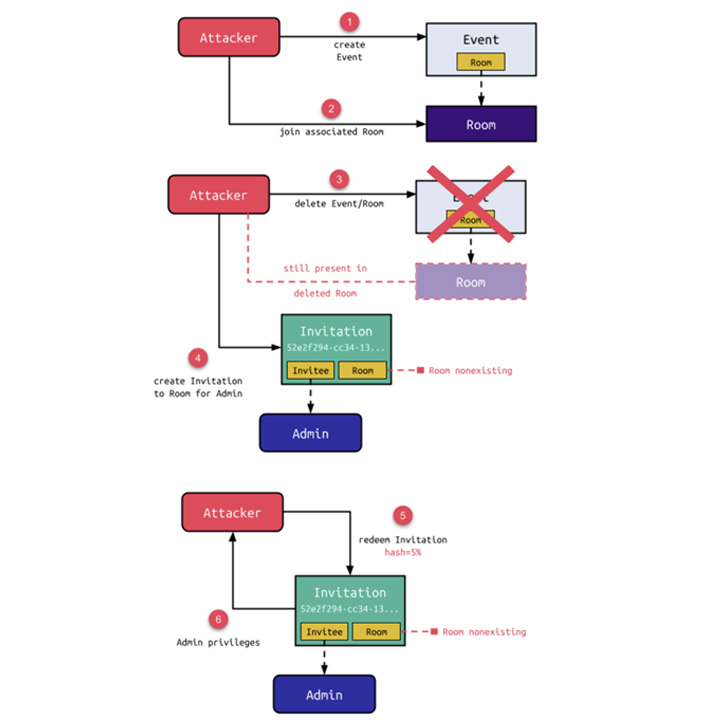
“Though the area is also deleted when its affiliated event is deleted, the existence of the attacker in the space would make this a zombie space,” Schiller spelled out. “Though an error is lifted when redeeming the hash for these kinds of an invitation, a legitimate web session for the invitee with complete permissions of this user is made.”
In other text, the zombie area could allow for the attacker to get admin privileges and make modifications to the OpenMeetings occasion, including incorporating and taking away end users and groups, modifying space configurations, and terminating sessions of connected people.
Sonar said it also determined a third vulnerability which is rooted in a aspect that enables an administrator to configure the path for executables relevant to ImageMagick, an open up-resource software program employed to edit and course of action photos. This enables an attacker with admin privileges to obtain code execution by transforming the ImageMagic route to “/bin/sh%00x” and triggering arbitrary shell instructions.
“When now uploading a pretend picture that contains a valid impression header adopted by arbitrary shell commands, the conversion spawns /bin/sh with the to start with argument staying the pretend impression, proficiently executing just about every command in it,” Schiller claimed.
“In mix with the account takeover, this vulnerability permits a self-registered attacker to attain distant code execution on the underlying server.”
Located this post attention-grabbing? Stick to us on Twitter and LinkedIn to read through more exceptional content material we write-up.
Some parts of this article are sourced from:
thehackernews.com


 North Korean State-Sponsored Hackers Suspected in JumpCloud Supply Chain Attack
North Korean State-Sponsored Hackers Suspected in JumpCloud Supply Chain Attack