Cybersecurity researchers have uncovered a new cloud targeting, peer-to-peer (P2P) worm referred to as P2PInfect that targets vulnerable Redis circumstances for follow-on exploitation.
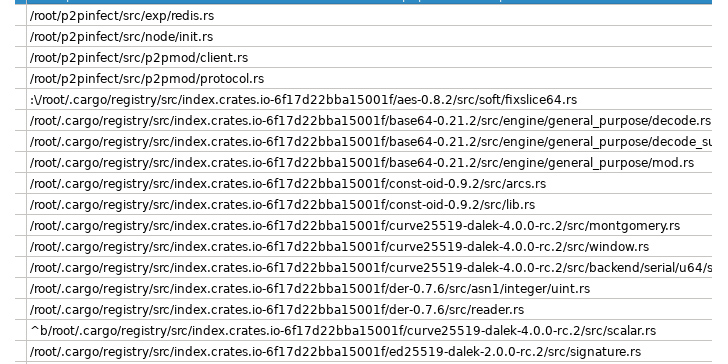
“P2PInfect exploits Redis servers running on both of those Linux and Windows Running Devices building it extra scalable and potent than other worms,” Palo Alto Networks Unit 42 researchers William Gamazo and Nathaniel Quist claimed. “This worm is also published in Rust, a remarkably scalable and cloud-friendly programming language.”
It is really believed that as numerous as 934 special Redis units might be vulnerable to the danger. The to start with regarded occasion of P2PInfect was detected on July 11, 2023.
A noteworthy characteristic of the worm is its means to infects susceptible Redis situations by exploiting a critical Lua sandbox escape vulnerability, CVE-2022-0543 (CVSS score: 10.), which has been beforehand exploited to provide various malware households these types of as Muhstik, Redigo, and HeadCrab about the past 12 months.
The initial entry afforded by a prosperous exploitation is then leveraged to deliver a dropper payload that establishes peer-to-peer (P2P) interaction to a bigger P2P network and fetch added destructive binaries, including scanning computer software for propagating the malware to other exposed Redis and SSH hosts.
“The contaminated occasion then joins the P2P network to supply entry to the other payloads to foreseeable future compromised Redis situations,” the scientists reported.
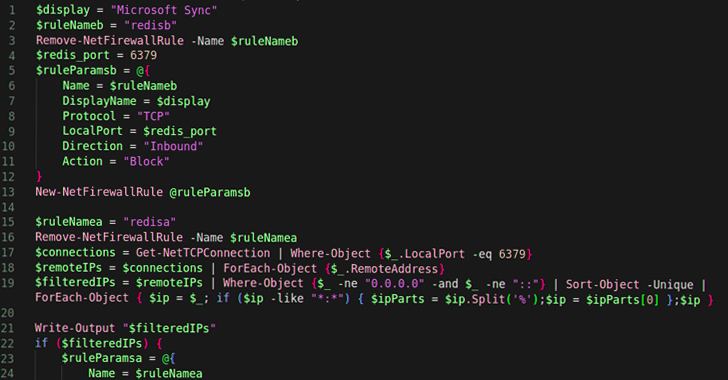
The malware also makes use of a PowerShell script to establish and preserve interaction in between the compromised host and the P2P network, providing menace actors persistent obtain. What’s more, the Windows taste of P2PInfect incorporates a Watch part to self-update and launch the new model.
It is really not straight away recognised what the stop aim of the marketing campaign is, with Device 42 noting that there is no definitive evidence of cryptojacking regardless of the presence of the word “miner” in the toolkit’s source code.
Approaching WEBINARShield From Insider Threats: Learn SaaS Security Posture Administration
Worried about insider threats? We’ve got you covered! Join this webinar to check out sensible tactics and the tricks of proactive security with SaaS Security Posture Administration.
Be a part of These days
The exercise has not been attributed to any recognized menace actor groups notorious for putting cloud environments like Adept Libra (aka TeamTNT), Aged Libra (aka Rocke), Automated Libra (aka PURPLEURCHIN), Money Libra (aka Kinsing), Returned Libra (aka 8220 Gang), or Thief Libra (aka WatchDog).
The progress will come as misconfigured and vulnerable cloud belongings are getting learned within just minutes by bad actors continuously scanning the internet to mount complex attacks.
“The P2PInfect worm appears to be very well intended with many modern day advancement choices,” the researchers reported. “The design and style and setting up of a P2P network to carry out the automobile-propagation of malware is not anything frequently witnessed in the cloud targeting or cryptojacking risk landscape.”
Discovered this short article attention-grabbing? Comply with us on Twitter and LinkedIn to study extra special material we article.
Some parts of this article are sourced from:
thehackernews.com

 Microsoft Expands Cloud Logging to Counter Rising Nation-State Cyber Threats
Microsoft Expands Cloud Logging to Counter Rising Nation-State Cyber Threats