Cyber attacks applying infected USB an infection drives as an preliminary accessibility vector have witnessed a a few-fold boost in the 1st fifty percent of 2023,
Which is in accordance to new findings from Mandiant, which comprehensive two these kinds of strategies – SOGU and SNOWYDRIVE – focusing on both equally community and personal sector entities across the planet.
SOGU is the “most widespread USB-dependent cyber espionage attack working with USB flash drives and just one of the most aggressive cyber espionage strategies concentrating on each community and non-public sector organizations globally across business verticals,” the Google-owned menace intelligence company mentioned.
The exercise has been attributed to a China-primarily based cluster known as TEMP.Hex, which is also tracked underneath the names Camaro Dragon, Earth Preta, and Mustang Panda. Targets include building and engineering, business providers, federal government, overall health, transportation, and retail in Europe, Asia, and the U.S.
The an infection chain comprehensive by Mandiant exhibits tactical commonalities with a different campaign comprehensive by Test Position, which took the wraps off a strain of self-propagating malware named WispRider that spreads via compromised USB drives and possibly breach air-gapped devices.
It all starts off with a destructive USB flash travel plugged into a computer, major to the execution of PlugX (aka Korplug), which then decrypts and launches a C-based backdoor termed SOGU that exfiltrates documents of desire, keystrokes, and screenshots.
SNOWYDRIVE Targets Oil and Gas Corporations in Asia
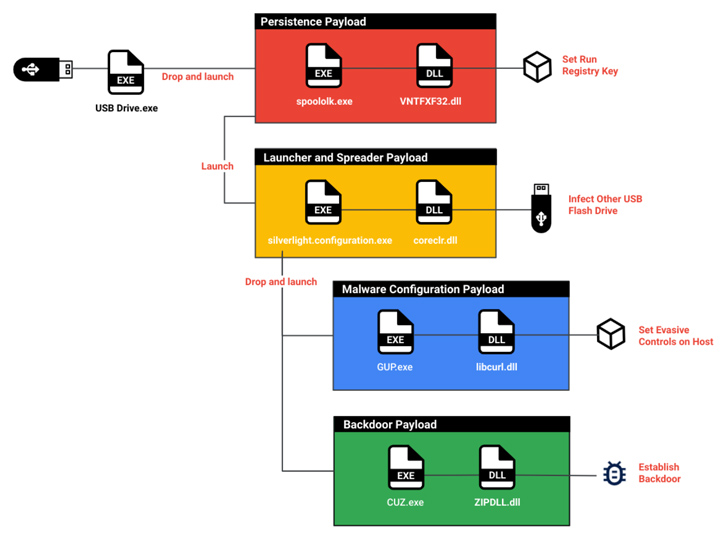
The second cluster to leverage the USB infiltration mechanism is UNC4698, which has singled out oil and gas corporations in Asia to provide the SNOWYDRIVE malware to execute arbitrary payloads on the hacked techniques.
Approaching WEBINARShield Against Insider Threats: Master SaaS Security Posture Management
Nervous about insider threats? We’ve got you lined! Be a part of this webinar to examine simple methods and the strategies of proactive security with SaaS Security Posture Management.
Join Nowadays
“When SNOWYDRIVE is loaded, it produces a backdoor on the host technique, supplying attackers the ability to remotely issue technique instructions,” Mandiant researchers Rommel Joven and Ng Choon Kiat explained. “It also spreads to other USB flash drives and propagates in the course of the network.”
In these assaults, the target is lured into clicking on a booby-trapped file that masquerades as a legit executable, thereby activating a chain of malicious actions, beginning with a dropper that establishes a foothold, followed by executing the SNOWYDRIVE implant.
Some of the functionalities of the backdoor consist of carrying out file and directory searches, uploading and downloading information, and launching a reverse shell.
“Companies should really prioritize implementing restrictions on accessibility to external units this sort of as USB drives,” the researchers reported. “If this is not achievable, they should at the very least scan these equipment for destructive information or code in advance of connecting them to their inner networks.”
Identified this write-up fascinating? Comply with us on Twitter and LinkedIn to read through additional unique content we put up.
Some parts of this article are sourced from:
thehackernews.com


 Cybercriminals Exploit Microsoft Word Vulnerabilities to Deploy LokiBot Malware
Cybercriminals Exploit Microsoft Word Vulnerabilities to Deploy LokiBot Malware