It might occur as a shock, but secrets and techniques management has turn out to be the elephant in the AppSec place. While security vulnerabilities like Frequent Vulnerabilities and Exposures (CVEs) generally make headlines in the cybersecurity earth, techniques administration continues to be an missed issue that can have rapid and impactful outcomes for company protection.
A the latest review by GitGuardian uncovered that 75% of IT final decision-makers in the US and the Uk reported at the very least a person top secret leaked from an application, with 60% leading to issues for the corporation or workforce. Shockingly, fewer than half of respondents (48%) had been assured in their means to shield software secrets “to a excellent extent.”
The examine, named Voice of Practitioners: The Point out of Secrets and techniques in AppSec (available for absolutely free download below), gives a refreshing perspective on managing secrets, which is often reduced to clichés that do not mirror the operational reality in engineering departments.
Despite their ubiquity in modern-day cloud and improvement operations, techniques stay a thorny issue even for the most experienced companies. The multiplication of the range of techniques staying simultaneously in use inside the growth cycle helps make it all way too easy to slide off the management of audio security actions and “leak.”
Guarding Software Tricks
When a key has leaked, it is no lengthier a solution and is accessible to unauthorized methods or persons for a selected period. Leaks largely happen internally due to the fact strategies get copied and pasted into configuration files, supply code data files, emails, messaging applications, and far more. Critically, if a developer hardcodes techniques into their code or configuration information and the code is pushed to a GitHub repository, all those secrets are also pushed. Yet another worst-situation situation occurs when a destructive actor manages to place their fingers on internally leaked credentials right after preliminary access, comparable to what took place last calendar year to Uber.
The Voice of Practioners research evidences that the threat of uncovered techniques is acknowledged by a large greater part of the respondents. Seventy-5 percent of the respondents said that a magic formula leak transpired in their firm in the past, and 60% acknowledged it caused critical issues for the corporation, personnel, or the two.
When requested about the critical risk points in just their software provide chains, 58% found “supply code and repositories” as the core risk region, with 53% for “open source dependencies” and 47% for “really hard-coded secrets and techniques.”
Nonetheless, the responses suggest a major gap in maturity. Precisely, fewer than 50 % of the respondents (48%) are self-confident in their capability to shield application techniques to a excellent extent:
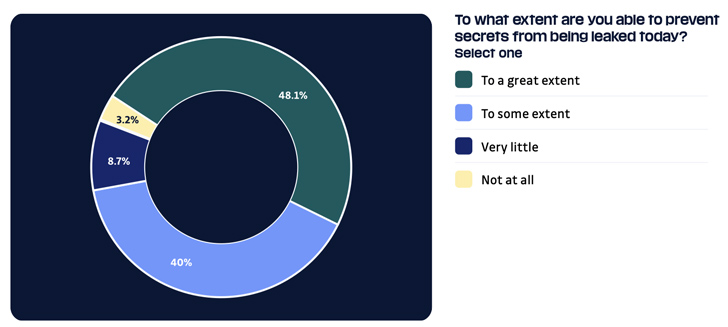 From Voice of Practitioners: The State of Insider secrets in AppSec
From Voice of Practitioners: The State of Insider secrets in AppSec
On top of that, a lot more than a quarter (27%) of the respondents admitted relying on guide code evaluations to reduce secret leaks, which are notably ineffective at detecting tough-coded insider secrets.
Eventually, the analyze also uncovered that 53% of senior administration (these kinds of as CSOs, CISOs, and VPs of cybersecurity) consider that techniques are shared in very clear text through messaging applications.
Irrespective of the difficulties, there is hope for advancement. The research discovered that 94% of respondents plan to enrich their insider secrets methods in the next 12-18 months, which is a favourable phase in direction of greater insider secrets management and corporate basic safety. Nonetheless, it is worthy of noting that secrets and techniques detection and remediation, as properly as techniques management, should be prioritized in conditions of investment when compared to other resources, these types of as runtime security equipment. Though 38% of respondents plan to devote in runtime software defense equipment, only 26% and 25%, respectively, plan to allocate cash for techniques detection and remediation and key management.
A In depth Secrets and techniques Management Application
More and a lot more tricks get leaked every 12 months. GitGuardian screens the annually quantity of leaks on the selection one code-sharing platform, GitHub, and publishes the outcomes in its once-a-year State of Tricks Sprawl report. At the time once more, the figures are bring about for alarm: from 3 million insider secrets detected in 2021, the range jumped 67% to 10 million in 2022. And this is just the suggestion of the iceberg. Most of the leaks transpire within the corporate perimeter, which tends to make it very tough to estimate a worldwide figure.
To tackle this expanding risk, businesses need to have to fortify their secrets and techniques management as a precedence to harden their defenses.
In a the latest interview with GitGuardian, Ubisoft’s former CISO Jason Haddix described how tricks administration importance turned clear immediately after the organization was targeted by the Laspsus$ hacking gang in March 2022. Soon after talking with 40 other affected CISOs, he arrived up with a 4-axis system to produce a thorough tricks management program:
- Detect: remaining able to discover all previous leaks calls for an automated instrument and is a critical phase to getting visibility into a firm’s true security posture.
- Protect against: save time for the foreseeable future by blocking leaks as a lot as possible, with secure guardrails this kind of as pre-commit hooks.
- Respond: tricks get leaked for the reason that they need to have to be shared. Owning equipment to keep, share and rotate these secrets and techniques along with fantastic-grained access controls is also critical.
- Educate: owning continued studying sessions about secrets, not just for builders but for all staff members, assures the risks linked with difficult-coding insider secrets and passwords, as nicely as the most effective tactics, are understood.
Summary
The Voice of Practitioners analyze highlights the importance of a holistic secrets technique in AppSec and gives valuable insights into the ideal procedures for lowering the risks connected with secrets and techniques sprawl. Tricks administration appears like a debt that compounds above time. If waiting for much too lengthy, the elephant in the place will inevitably turn into also huge to overlook, placing your firm at risk of really serious repercussions.
If you might be on the lookout to make improvements to your secrets administration method, a straightforward action you can consider right now is to request a free audit of your firm’s tricks leaks on GitHub from GitGuardian. The computerized report you will obtain will clearly show you the amount of energetic developers on GitHub, the variety of strategies discovered uncovered on GitHub’s repositories about time (classified), and the share of valid insider secrets among the them.
This will support you properly ascertain your developer perimeter on GitHub, evaluate the purchase of magnitude of the risk your business is struggling with, and just take the very first stage in the direction of a thorough techniques administration program.
Located this article intriguing? Adhere to us on Twitter and LinkedIn to read additional distinctive material we publish.
Some parts of this article are sourced from:
thehackernews.com

 Adversary-in-the-Middle Attack Campaign Hits Dozens of Global Organizations
Adversary-in-the-Middle Attack Campaign Hits Dozens of Global Organizations