Google has taken out a display recording application named “iRecorder – Screen Recorder” from the Engage in Retail outlet immediately after it was located to sneak in details stealing abilities virtually a year following the app was printed as an innocuous app.
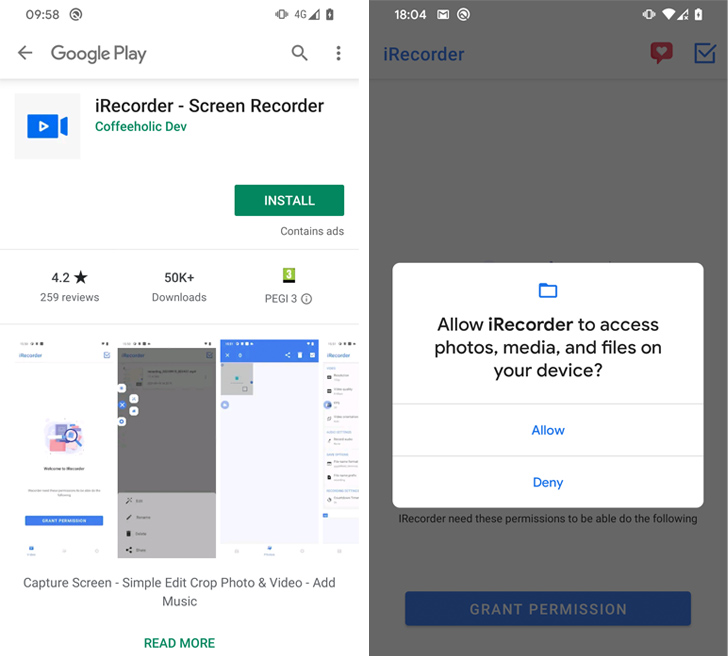
The application (APK package title “com.tsoft.application.iscreenrecorder”), which accrued over 50,000 installations, was to start with uploaded on September 19, 2021. The destructive operation is believed to have been released in version 1.3.8, which was introduced on August 24, 2022.
“It is unusual for a developer to add a legitimate application, hold out nearly a 12 months, and then update it with malicious code,” ESET security researcher Lukáš Štefanko reported in a complex report.
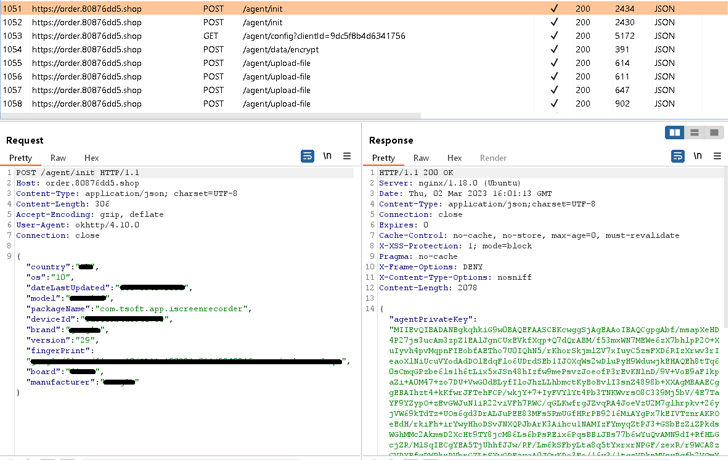
“The destructive code that was added to the clear edition of iRecorder is centered on the open up supply AhMyth Android RAT (remote accessibility trojan) and has been personalized into what we named AhRat.”
iRecorder was 1st flagged as harboring the AhMyth trojan on Oct 28, 2022, by Kaspersky security analyst Igor Golovin, indicating that the app managed to stay accessible all this time and even gained a new update as not too long ago as February 26, 2023.
The application’s malicious habits specially requires extracting microphone recordings and harvesting data files with particular extensions, with ESET describing AhRat as a light-weight version of AhMyth.
The facts gathering characteristic details to a attainable espionage motive, although there is no proof to website link the activity to any identified danger actor. Nonetheless, AhMyth has been beforehand utilized by Transparent Tribe in attacks targeting South Asia.
iRecorder is the do the job of a developer named Coffeeholic Dev, who has also released a number of other apps over the years. None of them are available as of producing –
- iBlock (com.tsoft.app.iblock.advert)
- iCleaner (com.isolar.icleaner)
- iEmail (com.tsoft.app.email)
- iLock (com.tsoft.application.ilock)
- iVideoDownload (com.tsoft.app.ivideodownload)
- iVPN (com.ivpn.pace)
- File speaker (com.teasoft.filespeaker)
- QR Saver (com.teasoft.qrsaver)
- Tin nóng tin lạnh (browse: Very hot news and chilly information in Vietnamese) (com.teasoft.information)
This enhancement is just the newest illustration of malware adopting a technique named versioning, which refers to uploading a cleanse edition of the app to the Enjoy Retail store to build believe in amongst users and then including malicious code at a later stage by using application updates, in a bid to slip by the app critique method.
“The AhRat analysis circumstance serves as a fantastic case in point of how an in the beginning genuine application can renovate into a malicious just one, even soon after several months, spying on its consumers and compromising their privacy,” Štefanko claimed.
Found this write-up appealing? Comply with us on Twitter and LinkedIn to browse extra exceptional content material we article.
Some parts of this article are sourced from:
thehackernews.com


 Legion Malware Upgraded to Target SSH Servers and AWS Credentials
Legion Malware Upgraded to Target SSH Servers and AWS Credentials