The notorious Lazarus Group actor has been concentrating on vulnerable variations of Microsoft Internet Information Products and services (IIS) servers as an initial breach route to deploy malware on targeted systems.
The results come from the AhnLab Security Unexpected emergency reaction Center (ASEC), which specific the sophisticated persistent threat’s (APT) continued abuse of DLL aspect-loading tactics to deploy malware.
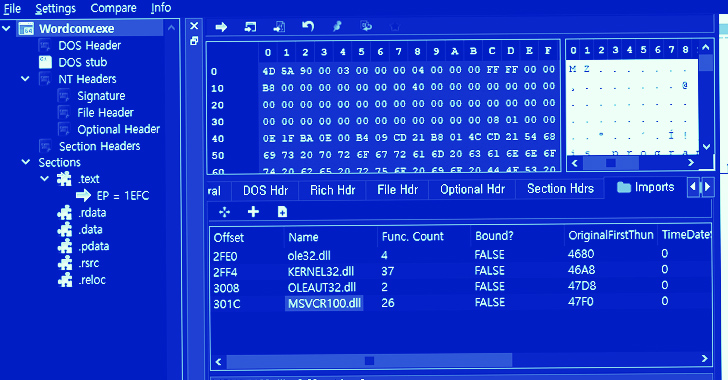
“The risk actor places a malicious DLL (msvcr100.dll) in the exact folder route as a standard application (Wordconv.exe) by using the Windows IIS web server approach, w3wp.exe,” ASEC explained. “They then execute the regular software to initiate the execution of the malicious DLL.”
DLL side-loading, very similar to DLL search-purchase hijacking, refers to the proxy execution of a rogue DLL through a benign binary planted in the exact same listing.
Lazarus, a very-capable and relentless country-condition group linked to North Korea, was most a short while ago spotted leveraging the exact same strategy in relationship with the cascading source chain attack on enterprise communications provider company 3CX.
The destructive msvcr100.dll library, for its component, is built to decrypt an encoded payload that is then executed in memory. The malware is claimed to be a variant of a related artifact that was discovered by ASEC past year and which acted as a backdoor to connect with an actor-managed server.
The attack chain more entailed the exploitation of a discontinued open up resource Notepad++ plugin termed Rapid Coloration Picker to deliver supplemental malware in order to facilitate credential theft and lateral movement.
The most up-to-date advancement demonstrates the range of Lazarus assaults and its means to utilize an comprehensive established of resources from victims to have out very long-term espionage functions.
“In unique, considering that the threat group primarily makes use of the DLL side-loading system in the course of their original infiltrations, companies must proactively monitor abnormal course of action execution relationships and choose preemptive actions to avoid the risk team from carrying out activities these as data exfiltration and lateral motion,” ASEC mentioned.
U.S. Treasury Sanctions North Korean Entities
The conclusions also come as the U.S. Treasury Section sanctioned four entities and 1 unique included in malicious cyber routines and fundraising schemes that purpose to assist North Korea’s strategic priorities.
Upcoming WEBINARZero Believe in + Deception: Master How to Outsmart Attackers!
Find out how Deception can detect superior threats, cease lateral movement, and enhance your Zero Rely on technique. Be a part of our insightful webinar!
Preserve My Seat!
This incorporates the Pyongyang College of Automation, the Specialized Reconnaissance Bureau and its subordinate cyber unit, the 110th Analysis Center, Chinyong Info Technology Cooperation Organization, and a North Korean nationwide named Kim Sang Person.
The Lazarus Group and its numerous clusters are thought to be operated by the Complex Reconnaissance Bureau, which oversees North Korea’s progress of offensive cyber tactics and applications.
The sanctions-hit country, other than participating in crypto currency theft and espionage operations, is acknowledged to create illicit revenue from a workforce of competent IT workers who pose under fictitious identities to obtain careers in the technology and virtual forex sectors throughout the planet.
“The DPRK conducts destructive cyber things to do and deploys information and facts technology (IT) staff who fraudulently receive employment to make revenue, such as in digital currency, to assist the Kim routine and its priorities, these as its illegal weapons of mass destruction and ballistic missile plans,” the section said.
“These personnel deliberately obfuscate their identities, places, and nationalities, generally using phony personas, proxy accounts, stolen identities, and falsified or forged documentation to use for work opportunities at these businesses.”
“They make hundreds of tens of millions of dollars a calendar year by participating in a vast variety of IT enhancement do the job, like freelance get the job done platforms (internet websites/applications) and cryptocurrency progress, immediately after obtaining freelance work contracts from providers close to the earth,” the South Korean government warned in December 2022.
Identified this write-up intriguing? Observe us on Twitter and LinkedIn to study far more special content we submit.
Some parts of this article are sourced from:
thehackernews.com

 Cyber Attacks Strike Ukraine’s State Bodies in Espionage Operation
Cyber Attacks Strike Ukraine’s State Bodies in Espionage Operation