The Log4Shell vulnerability critically threatens any individual using the preferred open-supply Apache Struts framework and could direct to a “Mini internet meltdown soonish.”
An excruciating, effortlessly exploited flaw in the ubiquitous Java logging library Apache Log4j that will allow unauthenticated distant code execution (RCE) and full server takeover is staying exploited in the wild.
Early Friday morning, the Cyber Crisis Response Crew (CERT) of the Deutsche Telekom Team tweeted that it was seeing attacks on its honeypots coming from the Tor network as threat actors experimented with to exploit the new zero-day vulnerability, which is tracked as “Log4Shell” by LunaSec and as CVE-2021-44228.
🚨⚠️New #-day vulnerability tracked underneath “Log4Shell” and CVE-2021-44228 found out in Apache Log4j 🌶️‼️ We are observing attacks in our honeypot infrastructure coming from the TOR network. Locate Mitigation guidelines in this article: https://t.co/tUKJSn8RPF pic.twitter.com/WkAn911rZX
— Deutsche Telekom CERT (@DTCERT) December 10, 2021
Ditto for CERT New Zealand and people who’ve piped up on Twitter to warn that they’re also seeing in-the-wild exploits.
This challenge is heading to induce a mini-internet meltdown, authorities mentioned, specified that Log4j is integrated into scads of common frameworks, like Apache Struts2, Apache Solr, Apache Druid and Apache Flink. That exposes an eye-watering selection of third-celebration applications that may perhaps also be susceptible to the similar form of high-severity exploits as that spotted in Minecraft, as well as in cloud solutions such as Steam and Apple iCloud.
Even nevertheless a fix was rushed out, it’s likely to just take time to trickle down, given how thoroughly the logging library is integrated downstream. “Expect a Mini internet meltdown soonish,” reported British security expert Kevin Beaumont, who tweeted that the resolve “needs to stream downstream to Apache Struts2, Solr, Linux distributions, distributors, appliances and so forth.”
Max CVSS Score of 10
The bug discover has been credited to Chen Zhaojun of Alibaba. It is been assigned the optimum CVSS rating of 10, presented how reasonably easy it is to exploit, attackers’ ability to seize control of qualified servers and the ubiquity of Log4j.
The internet’s response: “Umm, yikes.”
“This log4j (CVE-2021-44228) vulnerability is really negative,” tweeted security specialist Marcus Hutchins. “Millions of programs use Log4j for logging, and all the attacker requirements to do is get the app to log a specific string.”
According to LunaSec’s Thursday report, cloud providers which includes Steam, Apple iCloud and apps like Minecraft experienced presently been found to be susceptible, but as of Friday afternoon ET, reports of other afflicted applications were flooding in.
Just a single example of the bug’s enormous get to: On Friday early morning, Rob Joyce, director of cybersecurity at the Countrywide Security Company/ (NSA), tweeted that even the NSA’s Ghidra – a suite of reverse-engineering equipment formulated by NSA’s Analysis Directorate – features the buggy log4j library.
“The log4j vulnerability is a major danger for exploitation because of to the popular inclusion in software program frameworks, even NSA’s GHIDRA. This is a circumstance research in why the software monthly bill of substance (SBOM) ideas are so crucial to comprehend exposure.” —Rob Joyce, NSA Director of Cybersecurity
Initially Noticed on Minecraft Web pages
The flaw to start with turned up on internet sites that cater to customers of the world’s preferred sport, Minecraft, on Thursday. The sites reportedly warned that attackers could unleash destructive code on both servers or clientele managing the Java model of Minecraft by manipulating log messages, together with from text typed into chat messages.
In accordance to CERT Austria, the zero working day security gap can be exploited by simply logging a distinctive string. Scientists advised Ars Technica that Log4Shell is a Java deserialization bug that stems from the library producing network requests by the Java Naming and Directory Interface (JNDI) to an LDAP server and executing any code which is returned. It’s reportedly induced inside of of log messages with use of the $ syntax.
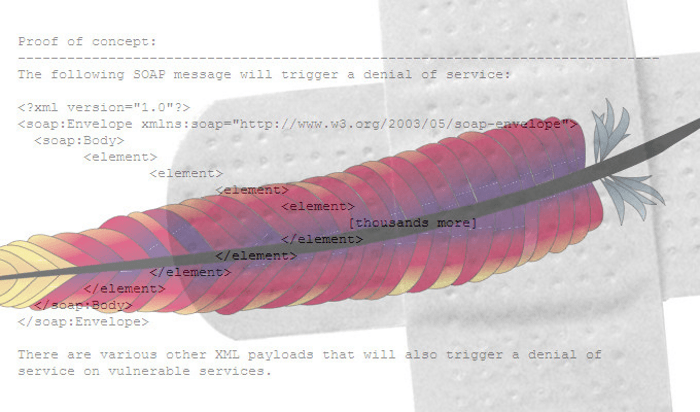
“JNDI triggers a search-up on a server managed by the attacker and executes the returned code,” according to CERT Austria’s advisory, posted Friday, which observed that code for an exploit evidence-of-concept (PoC) was published on GitHub.
Afflicted Versions
On Thursday, LunaSec explained that any person who’s utilizing Apache Struts – the popular open up-supply framework for developing web programs in the Java programming language – is likely vulnerable. The security business stated that we have observed related vulnerabilities exploited before in breaches such as the massive 2017 Equifax breach.
The security company explained that affected versions are 2. <= Apache log4j <= 2.14.1.
It added that JDK versions greater than 6u211, 7u201, 8u191, and 11.0.1 aren’t affected by the LDAP attack vector, specified that in individuals variations, “com.sun.jndi.ldap.object.trustURLCodebase is set to bogus that means JNDI simply cannot load a remote codebase making use of LDAP.”
But there are “other attack vectors concentrating on this vulnerability which can consequence in RCE,” LunaSec continued. “Depending on what code is current on the server, an attacker could leverage this existing code to execute a payload,” pointing to a Veracode post on an attack targeting the class org.apache.naming.factory.BeanFactory which is present on Apache Tomcat servers.
As of Friday, Edition 2.15. experienced been released. log4j-main.jar is obtainable on Maven Central in this article, with launch notes are available in this article and Apache’s log4j security announcements offered here.
LunaSec mentioned that, “given how ubiquitous this library is, the effect of the exploit (total server handle), and how quick it is to exploit, the effects of this vulnerability is fairly intense.”
Businesses can tell if they are afflicted by analyzing log files for companies applying impacted Log4j versions. If they contain user-managed strings – CERT-NZ utilizes the instance of “Jndi:ldap” – they could be afflicted.
In order to mitigate vulnerabilities, consumers should really switch log4j2.formatMsgNoLookups to true by adding:”‐Dlog4j2.formatMsgNoLookups=True” to the JVM command for beginning the application.
To retain the library from getting exploited, it’s urgently advisable that Log4j versions are upgraded to log4j-2.15.-rc1.
“If you believe you may be impacted by CVE-2021-44228, Randori encourages all businesses to undertake an assumed breach mentality and evaluation logs for impacted programs for unusual activity,” cybersecurity researchers at Randori wrote in a site write-up.
Momentary Mitigation
For those who simply cannot update straight off, LunaSec pointed to a discussion on HackerNews concerning a mitigation system out there in version 2.10. and bigger that was posted in the early hrs of Friday morning.
That system is no for a longer time needed with version 2.15., which will make it the default behavior.
For variations more mature than 2.10. that simply cannot be upgraded, these mitigation decisions were recommended:
- Modify just about every logging sample layout to say %mnolookups as a substitute of %m in your logging config data files (below are Apache’s information), or,
- Substitute a non-susceptible or empty implementation of the class org.apache.logging.log4j.main.lookup.JndiLookup, in a way that your classloader utilizes your alternative in its place of the vulnerable variation of the course. Refer to your application’s or stack’s classloading documentation to comprehend this habits.
Some parts of this article are sourced from:
threatpost.com

 The Morning After: 'Alan Wake 2' is coming in 2023
The Morning After: 'Alan Wake 2' is coming in 2023