An Android malware that was noticed abusing accessibility services in the unit to hijack consumer qualifications from European banking purposes has morphed into an entirely new botnet as component of a renewed marketing campaign that commenced in May possibly 2021.
Italy’s CERT-AGID, in late January, disclosed specifics about Oscorp, a mobile malware designed to attack numerous monetary targets with the goal of stealing cash from unsuspecting victims. Its capabilities include things like the means to intercept SMS messages and make phone calls and carry out Overlay Attacks for additional than 150 cell purposes by building use of lookalike login screens to siphon beneficial data.

The malware was dispersed as a result of malicious SMS messages, with the attacks typically done in true-time by posing as financial institution operators to dupe targets around the phone and surreptitiously achieve entry to the infected system by means of WebRTC protocol and finally conduct unauthorized lender transfers. When no new actions were described given that then, it appears that Oscorp could have staged a return soon after a short-term hiatus in the sort of an Android botnet recognized as UBEL.
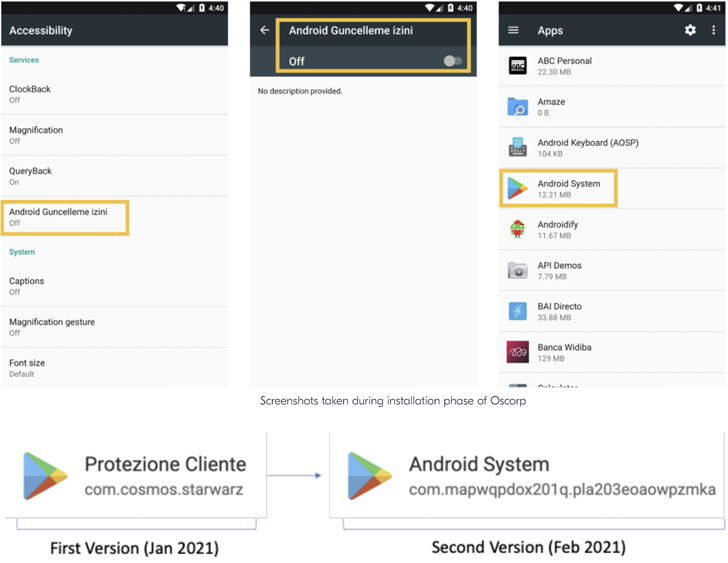
“By examining some connected samples, we discovered various indicators linking Oscorp and UBEL to the identical destructive codebase, suggesting a fork of the similar original project or just a rebrand by other affiliates, as its supply-code seems to be shared involving several [threat actors],” Italian cybersecurity business Cliffy mentioned Tuesday, charting the malware’s evolution.

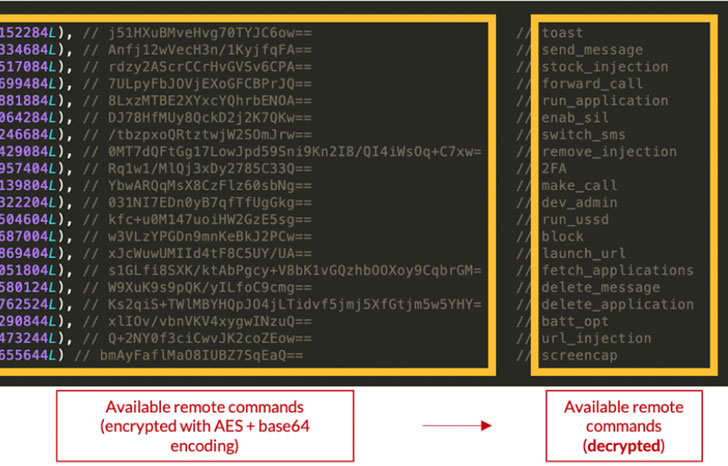
Marketed on underground forums for $980, UBEL, like its predecessor, requests for intrusive permissions that enables it to browse and deliver SMS messages, record audio, put in and delete programs, start by itself quickly after method boot, and abuse accessibility services on Android to amass delicate data from the unit this sort of as login qualifications and two-issue authentication codes, the effects of which are exfiltrated back again to a distant server.
As soon as downloaded on the device, the malware tries to put in by itself as a services and cover its existence from the goal, therefore achieving persistence for extended durations of time.
Apparently, the use of WebRTC to interact with the compromised Android phone in real-time circumvents the need to enroll a new gadget and choose around an account to conduct fraudulent pursuits.
“The most important target for this [threat actor] by utilizing this element, is to stay away from a ‘new system enrollment’, thus considerably reducing the risk of getting flagged ‘as suspicious’ considering that device’s fingerprinting indicators are well-recognised from the bank’s standpoint,” the researchers mentioned.
The geographical distribution of financial institutions and other applications targeted by Oscorp is composed of Spain, Poland, Germany, Turkey, the U.S., Italy, Japan, Australia, France, and India, among the some others.
Uncovered this short article intriguing? Abide by THN on Facebook, Twitter and LinkedIn to examine more exclusive articles we publish.
Some parts of this article are sourced from:
thehackernews.com

 Microsoft's profits skyrocketed by 47 percent in Q4
Microsoft's profits skyrocketed by 47 percent in Q4