The well-liked mastering-administration procedure for instructor-pupil interaction is rife with SQL-injection vulnerabilities.
Security vulnerabilities in Tutor LMS, a WordPress plugin set up on a lot more than 20,000 sites, open up the door to info theft and privilege escalation, according to researchers.
Tutor LMS is a finding out-administration program for educators that enables them to digitally reach their students. It supports class-setting up, pupil community forums, multimedia lessons and extra. In accordance to an investigation from Wordfence, there are five critical SQL-injection flaws in the plugin, and at the very least one superior-severity bug stemming from unprotected AJAX endpoints.
The previous “make it achievable for attackers to receive data saved in a site’s database, including person qualifications, website solutions and other delicate facts,” researchers stated, in a posting this 7 days.
The remaining flaws allow for authenticated attackers to elevate person privileges and alter training course information and options, by means of the use of many AJAX steps.
Web site directors ought to update to the patched model, Tutor LMS v.1.8.3.
Medium-Severity SQL-Injection Bugs
The five SQL-injection vulnerabilities all level 6.5 out of 10 on the CVSS vulnerability-rating scale, generating them medium in severity. CVEs are pending for all.
The 1st SQL-injection issue exists in a critique attribute in Tutor LMS that allows learners to amount their programs.
Tutor LMS presents a assortment of electronic studying characteristics. Click to enlarge.
To enter a ranking, the plugin takes advantage of an AJAX action to process the ask for, in accordance to Wordfence. If a evaluation presently exists for the present user and class, it will update the rating – if it is new, it will produce a new evaluate and score and include it to the databases.
“By utilizing get_var() without the use of prepare() when examining for the existence of a overview, along with no SQL sanitization on the person-equipped variables, a consumer could inject arbitrary SQL statements even though leaving a evaluation,” researchers described, introducing that a consumer would require to be authenticated to carry out an attack (while generating a scholar profile can be uncomplicated).
The injected arbitrary SQL statements could open up the doorway to snatching data from the site’s database, which include login particulars for users.
“In some conditions, wherever a MySQL server is insecurely configured, this could allow for an attacker to read information and build new files that contains web shells together with modifying data in the database,” researchers extra.
Another SQL-injection issue was identified in the potential for academics to mark solutions as correct the moment they have been submitted by a college student.
In this circumstance, the plugin works by using an AJAX motion to retrieve the original college student remedy recorded in the databases, even though using the user-provided benefit from the Put up parameter remedy_id as the answer ID.
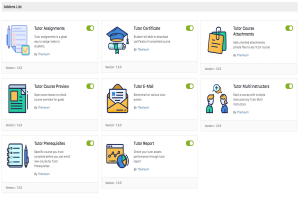
Gradebooks in Tutor LMS. Click to enlarge.
“Unfortunately, there was no SQL sanitization on the person-equipped price, nor was the purpose applying a ready statement, making it achievable for SQL queries to be injected,” according to Wordfence.
Scientists included, “This operation was intended to be made use of by instructors and directors only, nevertheless, considering that it was an AJAX action with no nonce protection or ability checks in location, this meant that any authenticated user, such as college students, experienced the skill to execute this motion and exploit the SQL injection vulnerability.”
The group also observed 3 UNION-dependent SQL-injection vulnerabilities. This sort of weakness happens when an SQL question can be joined to an presently current query, employing a UNION operator. UNION operators mix success of two different queries together.
“This differs from the past two SQL-injection kinds mentioned since data can easily be extracted by merely incorporating an additional question to the by now present question, through the use of the UNION operator,” researchers defined. “This is a single of the most straightforward, and least difficult, forms of SQL-injection vulnerability that can be exploited.”
UNION-Dependent SQL Bugs
The very first of these vulnerabilities exists in the Tutor LMS function that makes it possible for teachers to retrieve a established of answers for a provided issue, though analyzing the reaction of students.
In buy to deliver this operation, the plugin employs “get_results()” to receive the responses from the databases.
“Again, there was no SQL sanitization on the person-supplied input, nor was there any use of prepared statements,” researchers said. “This designed it attainable for an attacker to offer a UNION query in the ‘question_id’ parameter that would execute and offer the immediate results of the query in the reaction to the ask for.”
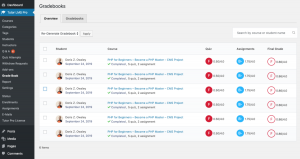
The Tutor LMS quiz-builder. Click on to enlarge.
The 2nd UNION-based bug lies in the ability to develop quizzes as a trainer on a web page. The perform works by using several AJAX steps to make the quiz-creating process straightforward and call for fewer web site reloads.
“When the ‘question_id’ parameter is provided, the operate utilizes ‘get_row()’ to get hold of the reply data from the database,” according to Wordfence. Below once more, there was no SQL sanitization on the consumer-provided input.
“This functionality, along with the tutor_quiz_builder_get_answers_by_concern() purpose, ended up supposed to be for teacher and administrator use only,” explained the scientists. “Unfortunately, on the other hand, due to the fact they had been AJAX steps with no nonce defense or functionality checks in location, any authenticated person, like learners, experienced the capability to execute this action and exploit the SQL-injection vulnerability.”
The final SQL injection vulnerability also stems from the quiz-creation attribute. Every time a scholar will take a quiz, the plugin documents the effects, but also permits pupils to go back later on and alter their answers.
“While retrieving those outcomes, the functionality used ‘get_success()’ to retrieve the success from the databases,” in accordance to the evaluation. “Due to the simple fact that there was no SQL-escaping on the quiz solutions as they were recorded, SQL statements could be provided as a quiz reaction. After the information was retrieved from the database on accessing the try specifics page, the saved SQL statements would execute and supply the requested information and facts from the databases.”
Unprotected AJAX Endpoints
And at last, Wordfence uncovered a raft of unprotected AJAX endpoints.
These “could allow lower-level consumers like learners to execute a myriad of actions that authorized them to produce new quizzes, modify system information, improve grades, escalate privileges and additional,” according to researchers.
The most serious of these is the aforementioned higher-severity privilege-escalation bug, which has a CVSS rating of 8.1.
Tutor LMS makes it possible for two roles: Scholar or instructor. Pupils can ask for to become a trainer, and directors can directly build new instructors on a presented web-site.
“Unfortunately, the two of these features have been insecurely implemented,” in accordance to the business. “Unfortunately, the approval method was vulnerable owing to a deficiency of a capacity examine, and authenticated college students could approve on their own as instructors.”
Moreover, directors have the choice to incorporate new instructors outside of the regular WordPress new user performance.
“Unfortunately, there was no ability test on this AJAX motion so any authenticated person could increase a new teacher account and then use that to create possibly destructive information on a web-site,” researchers spelled out.
The Perils of Plugins for WordPress
This calendar year is shaping up to be a banner 12 months for WordPress plugin difficulties, with several coming to light-weight in the very first quarter of 2021 alone.
Previous 7 days, the Additionally Addons for Elementor plugin was identified to have a critical security vulnerability that attackers can exploit to promptly, effortlessly and remotely just take in excess of a internet site. Very first claimed as a zero-working day bug, researchers reported it’s being actively attacked in the wild.
In February, an unpatched, saved cross-web site scripting (XSS) security bug was found to potentially have an effect on 50,000 Make contact with Sort 7 Fashion plugin end users.
And in January, researchers warned of two vulnerabilities (just one critical) in a WordPress plugin identified as Orbit Fox that could allow for attackers to inject malicious code into vulnerable internet sites and/or consider command of a website.
Also that thirty day period, a plugin called PopUp Builder, utilized by WordPress web sites for building pop-up advertisements for publication subscriptions, was located to have a vulnerability could be exploited by attackers to send out out newsletters with custom made information, or to delete or import newsletter subscribers.
Sign-up for this Are living Event: -Working day Disclosures: Superior, Lousy & Unattractive: On Mar. 24 at 2 p.m. ET, Threatpost tackles how vulnerability disclosures pose a risk to companies like Microsoft – at this time reeling more than -days identified in Trade Servers. Be part of -working day hunters from Intel Corp. and veteran bug bounty scientists who will untangle the -working day economic climate and unpack why comprehension it matters to all companies. Register NOW for this LIVE webinar on Wed., Mar. 24.
Some parts of this article are sourced from:
threatpost.com


 FBI Alert: Pysa Ransomware Targeting Education Sector
FBI Alert: Pysa Ransomware Targeting Education Sector