The operators of TrickBot trojan are collaborating with the Shathak threat group to distribute their wares, in the end leading to the deployment of Conti ransomware on contaminated devices.
“The implementation of TrickBot has progressed in excess of the many years, with new versions of TrickBot implementing malware-loading capabilities,” Cybereason security analysts Aleksandar Milenkoski and Eli Salem explained in a report analysing current malware distribution campaigns undertaken by the team. “TrickBot has performed a big position in lots of attack campaigns conducted by unique threat actors, from common cybercriminals to country-state actors.”

The hottest report builds on a report from IBM X-Power previous month, which revealed TrickBot’s partnerships with other cybercrime gangs, which include Shathak, to produce proprietary malware. Also tracked underneath the moniker TA551, Shathak is a advanced cybercrime actor focusing on stop-end users on a world scale, performing as a malware distributor by leveraging password-secured ZIP archives containing macro-enabled Business office files.
The TrickBot gang, regarded as ITG23 or Wizard Spider, is also responsible for building and keeping the Conti ransomware, in addition to leasing accessibility to the malicious software package to affiliate marketers by way of a ransomware-as-a-company (RaaS) design.
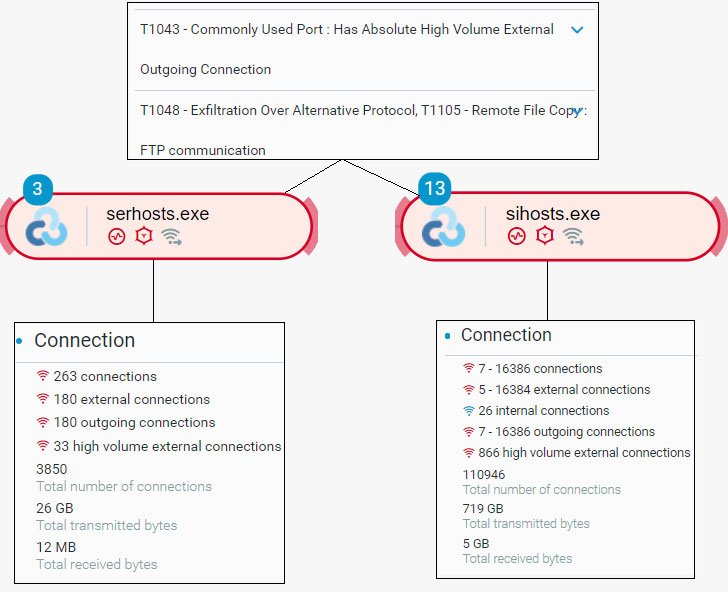
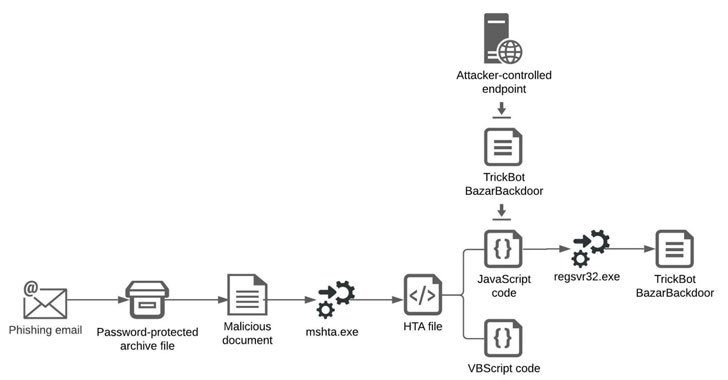
Infection chains involving Shathak commonly involve sending phishing email messages that appear embedded with malware-laced Word files that ultimately direct to the deployment of TrickBot or BazarBackdoor malware, which is then utilized as a conduit to deploy Cobalt Strike beacons as well as the ransomware, but not prior to conducting reconnaissance, lateral motion, credential theft, and facts exfiltration pursuits.

Cybereason researchers claimed they observed an ordinary Time-to-Ransom (TTR) of two days write-up the compromises, denoting the quantity of time from when the risk actor gains first obtain into a network to the time the menace actor actually deploys the ransomware.
The findings also occur as the U.S. Cybersecurity and Infrastructure Security Agency (CISA) and the Federal Bureau of Investigation (FBI) described that no less than 400 Conti ransomware attacks experienced taken position concentrating on U.S. and international organizations as of September 2021.
To protected devices towards Conti ransomware, the companies recommend enforcing a range of mitigation measures, which includes “requiring multi-aspect authentication (MFA), utilizing network segmentation, and holding working methods and application up to date.”
Identified this short article fascinating? Stick to THN on Fb, Twitter and LinkedIn to browse far more special articles we post.
Some parts of this article are sourced from:
thehackernews.com

 DOJ sues Uber for allegedly discriminating against passengers with disabilities
DOJ sues Uber for allegedly discriminating against passengers with disabilities