Researchers claimed the FoundCore malware represents a significant stage ahead when it will come to evasion.
An advanced cyberespionage marketing campaign targeting federal government and armed forces entities in Vietnam has been uncovered that shipped a remote-obtain resource (RAT) for carrying out espionage operations, researchers stated.
Additional investigation prompt that this marketing campaign was executed by a team related to a Chinese-talking advanced persistent risk (APT) recognised as Cycldek (a.k.a. Goblin Panda, APT 27 and Conimes), according to Kaspersky scientists, who additional that the team has been energetic considering that at minimum 2013.
The malware utilised in the campaign, dubbed FoundCore, allows attackers to perform filesystem manipulation, system manipulation, screenshot captures and arbitrary command execution.
It signifies a significant progression in sophistication for the team, according to an assessment produced Monday by Kaspersky. For instance, the process used to safeguard the malicious code from investigation is distinctive for Chinese-speaking teams, researchers said.
“The headers (the destination and source for the code) for the last payload have been wholly stripped away, and the number of that remained contained incoherent values,” they stated. “In doing this, the attackers make it appreciably a lot more tough for scientists to reverse engineer the malware for assessment. What’s a lot more, the elements of the an infection chain are tightly coupled, that means solitary parts are difficult—sometimes impossible—to review in isolation, blocking a comprehensive picture of malicious action.”
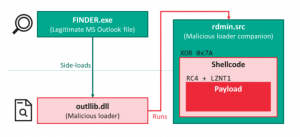
The FoundCore an infection routine (simply click to enlarge). Resource: Kaspersky.
The campaign also uses sideloading of dynamic-hyperlink libraries (DLLs), which comes about when a legitimately signed file is tricked into loading a destructive DLL, allowing for the attackers to bypass security goods.
“In this not too long ago uncovered marketing campaign, the DLL aspect-loading infection chain executes a shellcode that decrypts the remaining payload: [FoundCore], that provides the attackers total handle in excess of the infected system,” in accordance to the investigation.
FoundCore: 4 Malware Threads
The last payload in the infection chain is a distant administration instrument that offers whole handle in excess of the victim equipment to its operators. On execution, this malware commences 4 threads, according to researchers:
- The initially one particular establishes persistence by generating a company.
- The second 1 sets inconspicuous information and facts for the assistance by transforming its Description, ImagePath and DisplayName fields (among the others).
- The 3rd sets an vacant Discretionary Access Control Listing (DACL) to the graphic linked to the recent course of action in get to prevent entry to the underlying malicious file. DACL is an interior list hooked up to an object in Energetic Directory that specifies which customers and groups can access the item and what forms of operations they can accomplish on the item.
- Finally, a worker thread bootstraps execution and establishes connection with the C2 server. Depending on its configuration, it may also inject a duplicate of alone to yet another system.
Communications with the server can just take position either about uncooked TCP sockets encrypted with RC4, or via HTTPS.
In the infection chain, FoundCore was also observed downloading two further pieces of spyware. The first, DropPhone, collects environmental information and facts from the target device and sends it to DropBox. The 2nd, CoreLoader, runs code that assists the malware evade detection by security merchandise.
“In typical, over the earlier yr, we’ve found that a lot of of these Chinese-speaking groups are investing a lot more means into their strategies and honing their specialized capabilities,” said Mark Lechtik, senior security researcher with Kaspersky, in the analysis. “Here, they’ve additional lots of a lot more levels of obfuscation and noticeably challenging reverse engineering. And this alerts that these teams might be seeking to increase their functions.”
Vietnam in APT Sights
Kaspersky’s evaluation confirmed that dozens of computer systems were targeted in the campaign with the vast greater part (80 per cent) situated in Vietnam. The other targets were being found in Central Asia and in Thailand.
The company also uncovered that most of the victims belonged to the federal government or army sector. That said, there have been other focused sectors, including diplomacy, instruction or health care.
“Right now, it may seem to be as if this marketing campaign is additional of a nearby risk, but it’s highly probable the FoundCore backdoor will be located in a lot more countries in distinct regions in the potential,” Lechtik stated.
Pierre Delcher, senior security researcher with Kaspersky, included, “What’s additional, offered that these Chinese-talking groups are inclined to share their ways with a person a further, we wouldn’t be surprised to obtain these very same obfuscation practices in other campaigns. We’ll be checking the danger landscape for related suspicious exercise carefully. For firms, the greatest issue they can do is continue to keep their enterprise up-to-day with the latest risk intelligence, so they know what to be on the lookout for.”
Check out our free upcoming live webinar events – exceptional, dynamic discussions with cybersecurity authorities and the Threatpost community:
- April 21: Underground Marketplaces: A Tour of the Dark Overall economy (Find out more and register!)
Some parts of this article are sourced from:
threatpost.com


 LinkedIn Spear-Phishing Campaign Targets Job Hunters
LinkedIn Spear-Phishing Campaign Targets Job Hunters