Network Threats: A Step-by-Step Attack Demonstration
Adhere to this genuine-lifestyle network attack simulation, covering 6 steps from Preliminary Access to Facts Exfiltration. See how attackers stay undetected with the simplest tools and why you require various choke points in your protection approach.…
Network Threats: A Step-by-Step Attack DemonstrationRead More

DOJ Arrests Founders of Crypto Mixer Samourai for $2 Billion in Illegal Transactions
The U.S. Department of Justice (DoJ) on Wednesday announced the arrest of two co-founders of a cryptocurrency mixer referred to as Samourai and seized the provider for allegedly facilitating about $2 billion in illegal transactions and…
DOJ Arrests Founders of Crypto Mixer Samourai for $2 Billion in Illegal TransactionsRead More

Google Postpones Third-Party Cookie Deprecation Amid U.K. Regulatory Scrutiny
Google has as soon as once again pushed its plans to deprecate 3rd-occasion tracking cookies in its Chrome web browser as it operates to address exceptional level of competition problems from U.K. regulators above its Privacy…
Google Postpones Third-Party Cookie Deprecation Amid U.K. Regulatory ScrutinyRead More

State-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
A new malware marketing campaign leveraged two zero-working day flaws in Cisco networking equipment to produce custom malware and facilitate covert knowledge collection on focus on environments. Cisco Talos, which dubbed the action ArcaneDoor, attributing it…
State-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for EspionageRead More

U.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
The U.S. Treasury Department’s Business office of Foreign Assets Regulate (OFAC) on Monday sanctioned two companies and 4 persons for their involvement in destructive cyber things to do on behalf of the Iranian Islamic Revolutionary Guard…
U.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber AttacksRead More
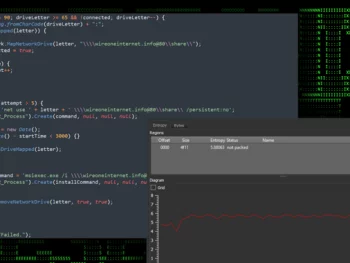
Researchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
Cybersecurity scientists have identified an ongoing attack campaign which is leveraging phishing e-mail to provide malware named SSLoad. The campaign, codenamed FROZEN#SHADOW by Securonix, also requires the deployment of Cobalt Strike and the ConnectWise ScreenConnect distant…
Researchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt StrikeRead More









