SonicWall has printed an advisory warning of a trio of security flaws in its Safe Mobile Access (SMA) 1000 appliances, including a superior-severity authentication bypass vulnerability.
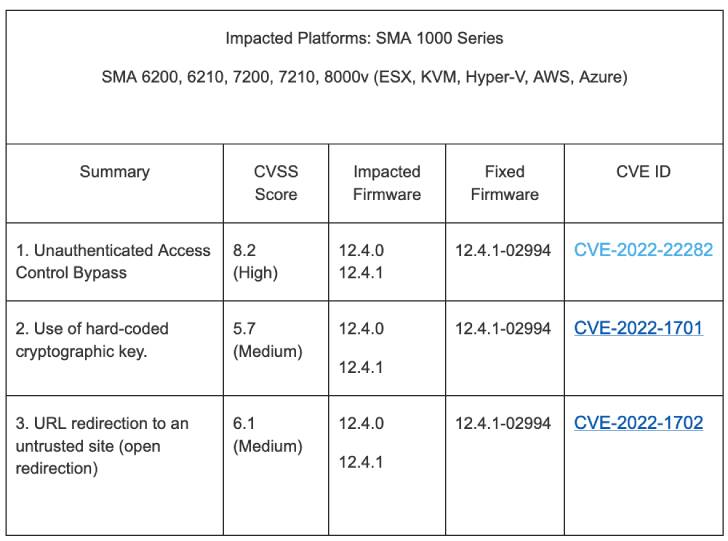
The weaknesses in issue influence SMA 6200, 6210, 7200, 7210, 8000v operating firmware versions 12.4. and 12.4.1. The listing of vulnerabilities is beneath –
- CVE-2022-22282 (CVSS rating: 8.2) – Unauthenticated Obtain Handle Bypass
- CVE-2022-1702 (CVSS score: 6.1) – URL redirection to an untrusted website (open up redirection)
- CVE-2022-1701 (CVSS rating: 5.7) – Use of a shared and difficult-coded cryptographic critical
Productive exploitation of the aforementioned bugs could make it possible for an attacker to unauthorized obtain to inside methods and even redirect opportunity victims to malicious web sites.

Tom Wyatt of the Mimecast Offensive Security Group has been credited with discovering and reporting the vulnerabilities.
SonicWall pointed out that the flaws do not have an impact on SMA 1000 collection jogging variations before than 12.4., SMA 100 collection, Central Management Servers (CMS), and distant accessibility shoppers.
Despite the fact that there is no evidence that these vulnerabilities are remaining exploited in the wild, it’s advised that consumers use the fixes in the mild of the actuality that SonicWall appliances have introduced an interesting bullseye in the past for ransomware attacks.
“There are no non permanent mitigations,” the network security company mentioned. “SonicWall urges impacted customers to employ applicable patches as shortly as possible.”
Found this short article appealing? Follow THN on Fb, Twitter and LinkedIn to read much more unique content we put up.
Some parts of this article are sourced from:
thehackernews.com

 DOJ warns AI hiring and productivity tools can violate anti-discrimination law
DOJ warns AI hiring and productivity tools can violate anti-discrimination law