Vulnerability assessment success in Orange Cyberdefenses’ Security Navigator exhibit that some vulnerabilities first uncovered in 1999 are nonetheless identified in networks right now. This is regarding.
Age of VOC results
Our Vulnerability Scans are carried out on a recurring foundation, which presents us the prospect to examine the variation amongst when a scan was executed on an Asset, and when a offered acquiring on that Asset was described. We can contact that the obtaining ‘Age’. If the results initial noted are not dealt with, they will occur in a lot more scans in excess of time with escalating Age, and so we can track how the Age of described conclusions modifications about time.
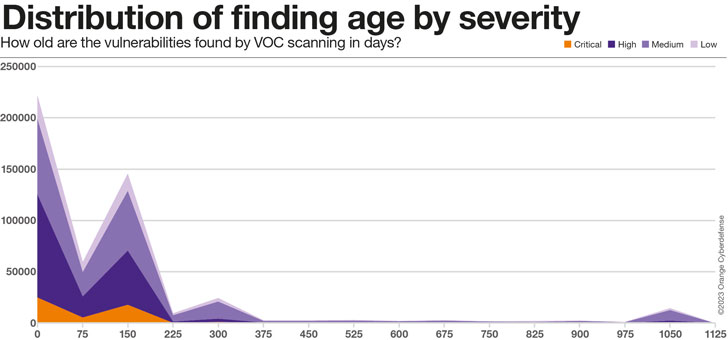
As the chart down below clearly illustrates, the bulk of actual conclusions in our dataset, across all Severity amounts, are amongst 75 and 225 times outdated. There is a second ‘peak’ at all-around 300 times, which we suspect has extra to do with the age of the facts in the dataset and can as a result be disregarded. Ultimately, there is a intriguing ‘bump’ at close to 1,000 days, which we feel represents the ‘long tail’ of conclusions in the dataset that will simply by no means be resolved.
75% of the conclusions in the 1000-days ‘bump’ are Medium Severity, but 16% are categorized as Large or Critical Severity.
The Average Age of conclusions in our dataset is impacted as a lot by changes in our Purchaser and Assets established as any exterior aspect, as can be viewed in the higher degree of variation. Nonetheless, there is a distinct maximize in the Common Age of conclusions of 241% from 63 to 215 days above the 24 months because we have been onboarding purchasers onto this system.
Approximately grouping confirmed findings from our Vulnerability Scan details by ‘Age Group’ reveals the following:
- Only 20% of all findings are dealt with in beneath 30 days
- 80% all conclusions choose 30 times or extra to patch
- 57% of all conclusions consider 90 days or more to patch.
- 215 times Ordinary
Ordinary/max age of results by severity
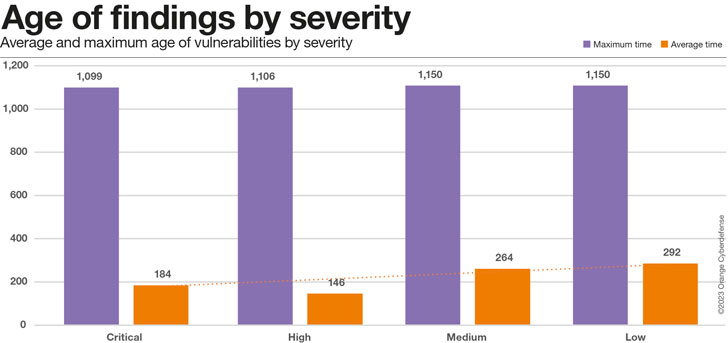
The chart below implies that even Critical Vulnerabilities are getting close to 6 months on regular to take care of, but that is encouragingly at least 36% a lot quicker than the time for reduced-severity issues.
Using a nearer glance at the readings of ordinary vs. optimum time for distinctive scores of criticality we conclude up with the chart underneath.
When our summary of critical issues currently being settled a lot quicker stands for the ordinary mitigation time, the optimum time is continuously significant irrespective of criticality.
We will have to watch this metric extra as the dataset grows in the future.
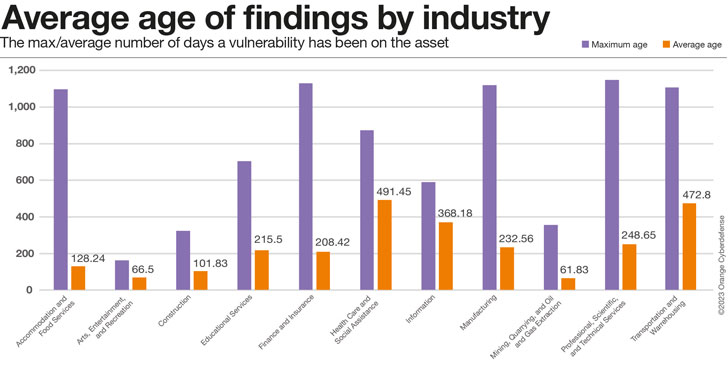
Sector Comparison
The highest age of conclusions in the look at beneath serves as significantly as an sign of how long prospects from that Industry have been current in our dataset as just about anything else, even though the normal age is a far better proxy for how effectively consumers are carrying out at addressing the issues we report. Industries with substantial maximums and minimal averages would therefore be carrying out the finest, high most and significant average… the ‘worst.’ Industries with really minimal optimum ages have likely not been in the dataset for extremely lengthy and must, as a result, most likely not be provided in comparisons on this metric.
On the other hand these Industries are as opposed, the locating Age is a regarding metric.
How old are those vulnerabilities definitely?
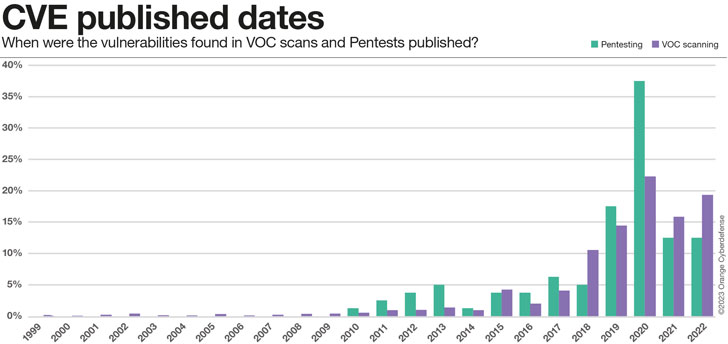
So far we have only looked at the relative time, from when we 1st found a vulnerability in an asset up until now (if still current). Nevertheless, that does not give us any information on how outdated those people vulnerabilities definitely are. Using a closer search at the observed CVEs we can assess their publishing dates. The success are rather baffling, but appear to be to suit the image that emerges: for one reason or another, some vulnerabilities are just not mounted, at any time. They grow to be element of the security credit card debt that corporations accumulate.
- .5% of CVEs reported are 20 a long time aged or much more
- 13% of CVEs stories are 10 several years previous or much more
- 47% of CVEs are 5 yrs previous or more
Conclusion
More than 22 vulnerabilities with assigned CVEs are released just about every day. With an average CVSS rating over 7 (Higher Severity), every single of these disclosed vulnerabilities is a major datapoint that impacts our risk equations and our actual publicity to threats.
Vulnerability Scanning and Penetration Screening are mechanisms we use to make sense of the vulnerabilities that might impression our security posture, have an understanding of their possible effects, prioritize and choose correct action. These two assessment exercises are various in method, but use very similar language and serve a comparable reason.
This year we are including an analysis of datasets from the two solutions in the Navigator. This is the to start with time we are attempting this, and our information is even now far from excellent.
What we can clearly see is the we’re having difficulties to deal with the vulnerabilities we know about. On ordinary, it is getting our clients 215 days to patch a vulnerability we report to them. This is a small reduced for Critical Vulnerabilities – it seems these are patched 36% a lot quicker than ‘Low’ severity issues. But the picture is however grim: 80% of all Findings just take 30 times or much more to patch, 57% just take 90 times or additional.
Our pentesting teams are nevertheless identifying vulnerabilities that ended up to start with identified in 2010, and our scanning teams come upon issues that date back to 1999! Without a doubt 47% of CVEs are 5 a long time old or far more. 13% are as previous as 10 years or additional. This is a regarding end result.
This is just an excerpt of the evaluation. Much more facts, like the criticality of vulnerabilities and the variations in Pentesting and VOC scanning success more than time (as perfectly as a ton of other attention-grabbing research subject areas), can be discovered in the Security Navigator. It is really absolutely free of demand, so have a seem. It truly is worth it!
Be aware: This insightful piece has been expertly crafted and generously shared by Charl van der Walt, Head of Security Investigation at Orange Cyberdefense.
Uncovered this posting interesting? Observe us on Twitter and LinkedIn to browse extra exceptional content we post.
Some parts of this article are sourced from:
thehackernews.com


 Gartner: Zero Trust Will Not Mitigate Over Half of Attacks
Gartner: Zero Trust Will Not Mitigate Over Half of Attacks