Cybersecurity scientists have taken the wraps off a new and completely undetected Linux risk dubbed OrBit, signally a growing craze of malware assaults geared toward the well known functioning program.
The malware receives its identify from just one of the filenames that is used to temporarily retail outlet the output of executed commands (“/tmp/.orbit”), according to cybersecurity organization Intezer.
“It can be mounted possibly with persistence capabilities or as a volatile implant,” security researcher Nicole Fishbein said. “The malware implements state-of-the-art evasion techniques and gains persistence on the machine by hooking essential features, presents the risk actors with distant obtain abilities in excess of SSH, harvests credentials, and logs TTY instructions.”
OrBit is the fourth Linux malware to have occur to light-weight in a limited span of a few months soon after BPFDoor, Symbiote, and Syslogk.
The malware also capabilities a large amount like Symbiote in that it is developed to infect all of the operating procedures on the compromised machines. But as opposed to the latter which leverages the LD_PRELOAD atmosphere variable to load the shared item, OrBit employs two distinct strategies.
“The first way is by introducing the shared item to the configuration file that is utilized by the loader,” Fishbein defined. “The second way is by patching the binary of the loader by itself so it will load the destructive shared object.”
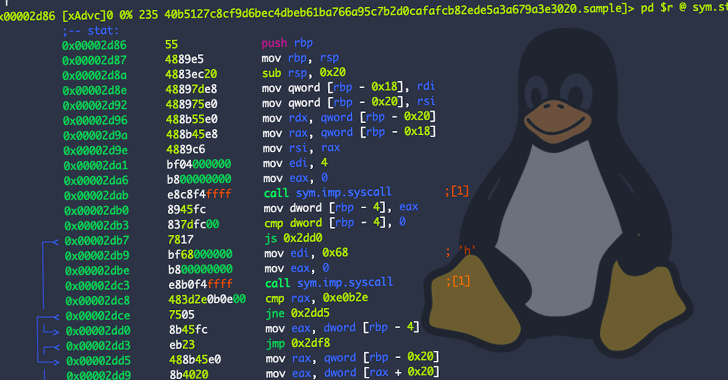
The attack chain commences with an ELF dropper file which is liable for extracting the payload (“libdl.so”) and adding it to the shared libraries that are remaining loaded by the dynamic linker.
The rogue shared library is engineered to hook features from a few libraries — libc, libcap, and Pluggable Authentication Module (PAM) — leading to present and new procedures to use the modified capabilities, fundamentally permitting it to harvest credentials, cover network action, and established up remote access to the host over SSH, all the though keeping beneath the radar.

Moreover, OrBit relies on a barrage of methods that enables it to purpose with out alerting its presence and establish persistence in a method that can make it difficult to take out from the infected equipment.
The moment engaged, the backdoor’s ultimate purpose is to steal information by hooking the browse and produce capabilities to seize facts that is becoming penned by the executed processes on the equipment, such as bash and sh instructions, the effects of which are saved in precise data files.
“What can make this malware particularly exciting is the pretty much hermetic hooking of libraries on the target equipment, that enables the malware to gain persistence and evade detection though thieving facts and environment SSH backdoor,” Fishbein explained.
“Threats that focus on Linux go on to evolve although productively staying under the radar of security applications, now OrBit is a single extra instance of how evasive and persistent new malware can be.”
Uncovered this report interesting? Adhere to THN on Facebook, Twitter and LinkedIn to examine extra distinctive information we publish.
Some parts of this article are sourced from:
thehackernews.com

 Apple’s New “Lockdown Mode” Protects iPhone, iPad, and Mac Against Spyware
Apple’s New “Lockdown Mode” Protects iPhone, iPad, and Mac Against Spyware