Cybersecurity scientists have shown a new attack procedure that would make it feasible to leverage a device’s Bluetooth ingredient to directly extract network passwords and manipulate site visitors on a Wi-Fi chip.
The novel assaults perform in opposition to the so-identified as “combo chips,” which are specialised chips that are outfitted to take care of various styles of radio wave-dependent wireless communications, these types of as Wi-Fi, Bluetooth, and LTE.
“We give empirical proof that coexistence, i.e., the coordination of cross-technology wireless transmissions, is an unexplored attack surface area,” a group of scientists from the Complex University of Darmstadt’s Safe Cellular Networking Lab and the College of Brescia reported in a new paper.
“In its place of escalating right into the cellular [operating system], wireless chips can escalate their privileges into other wireless chips by exploiting the exact same mechanisms they use to arbitrate their accessibility to the sources they share, i.e., the transmitting antenna and the wireless medium.”

Coexistence refers to a system whereby Bluetooth, Wi-Fi, and LTE share the identical components and sources — e.g., antenna or wi-fi spectrum — necessitating that these communication specifications coordinate the spectrum access to keep away from collisions when working in the identical frequency. Chipset suppliers use this principle to permit Wi-Fi and Bluetooth to function just about concurrently.
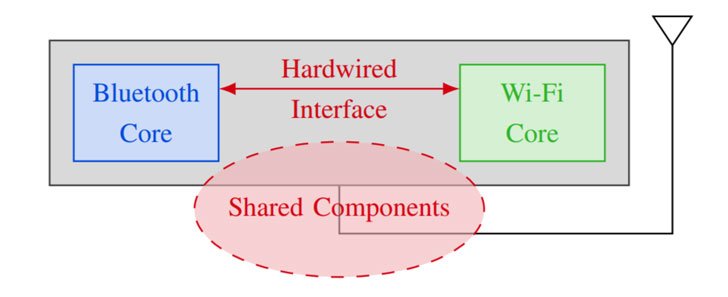
While these combo wi-fi chips are vital to high-overall performance spectrum sharing, coexistence interfaces also pose a aspect-channel risk as shown by the very same set of scientists at the Black Hat security conference past year, correctly allowing a malicious celebration to glean details from other wireless systems supported by the combo chip.
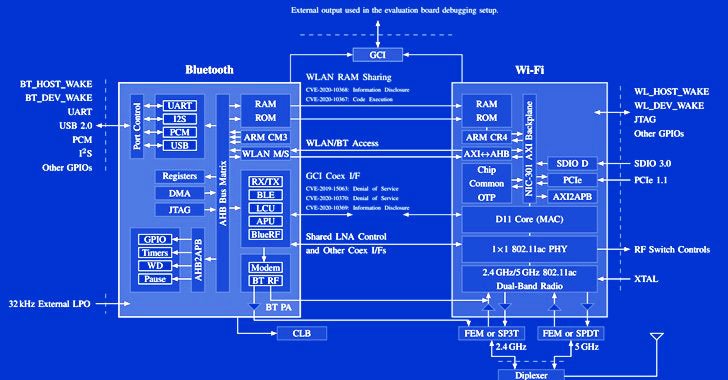
Dubbed “Spectra,” the vulnerability class banking institutions on the truth that transmissions occur in the exact same spectrum and wi-fi chips will need to arbitrate the channel entry. This breaks the separation between Wi-Fi and Bluetooth to result in denial-of-support on spectrum accessibility, information disclosure, and even enable lateral privilege escalations from a Bluetooth chip to code execution on a Wi-Fi chip.
“The Wi-Fi chip encrypts network targeted traffic and holds the existing Wi-Fi credentials, thus offering the attacker with further information,” the scientists said. “Also, an attacker can execute code on a Wi-Fi chip even if it is not related to a wireless network.”
In addition, the scientists found that it can be possible for an adversary with control about the Wi-Fi main to notice Bluetooth packets, which, in switch, makes it possible for figuring out keystroke timings on Bluetooth keyboards, in the long run granting the attacker the means to reconstruct text entered employing the keyboard.
When some of the attack eventualities were to start with documented to the distributors as early as August 2019, the coexistence flaws proceed to keep on being unpatched on Broadcom SoCs to date.
“As of November 2021, extra than two many years immediately after reporting the very first coexistence bug, coexistence attacks, together with code execution, continue to do the job on up-to-date Broadcom chips,” the teachers reported. “This highlights how hard these issues are to take care of in apply.”
To lessen the risk of this kind of wi-fi attacks, it truly is proposed that buyers get rid of unwanted Bluetooth pairings, delete unused Wi-Fi networks, and prohibit to working with mobile as a substitute of Wi-Fi at public spaces.
“Mobile knowledge plans got a lot more affordable for the duration of current yrs and cellular network coverage greater,” the researchers concluded. “Disabling Wi-Fi by default and only enabling it when using reliable networks can be considered a excellent security practice, even if cumbersome.”
Discovered this post appealing? Adhere to THN on Facebook, Twitter and LinkedIn to read through additional distinctive material we put up.
Some parts of this article are sourced from:
thehackernews.com

 The Guide to Automating Security Training for Lean Security Teams
The Guide to Automating Security Training for Lean Security Teams