An Iranian risk actor has unleashed a new cyberespionage campaign towards a possible Lebanese focus on with a backdoor able of exfiltrating delicate information from compromised programs.
Cybersecurity agency Examine Issue attributed the procedure to APT34, citing similarities with earlier strategies made use of by the threat actor as perfectly as dependent on its sample of victimology.
APT34 (aka OilRig) is identified for its reconnaissance strategies aligned with the strategic interests of Iran, mostly hitting economical, government, vitality, chemical, and telecommunications industries in the Center East.
The team ordinarily resorts to focusing on men and women through the use of booby-trapped occupation present documents, shipped straight to the victims via LinkedIn messages, and the hottest marketing campaign is no exception, even though the manner of shipping continues to be unclear as yet.
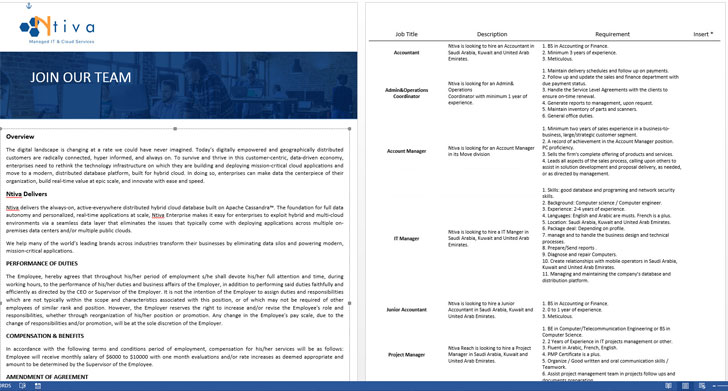
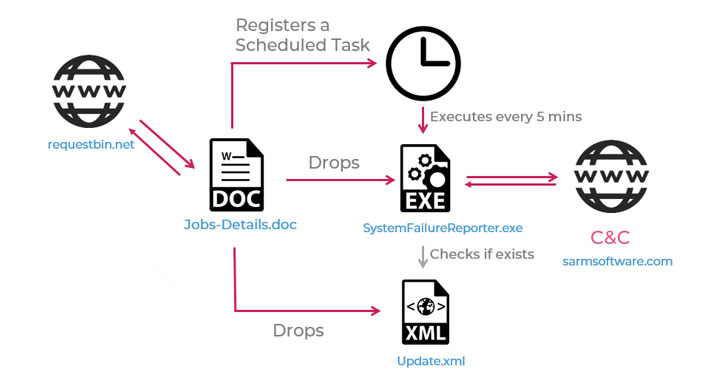
The Word doc analyzed by Test Stage — which was uploaded to VirusTotal from Lebanon on January 10 — statements to offer details about distinct positions at a U.S.-centered consulting business named Ntiva IT, only to trigger the an infection chain upon activating the embedded malicious macros, finally resulting in the deployment of a backdoor named “SideTwist.”
Aside from collecting primary information about the victim’s device, the backdoor establishes connections with a distant server to await extra commands that allow it to download data files from the server, add arbitrary files, and execute shell instructions, the final results of which are posted again to the server.
Verify Level notes that the use of new backdoor points to the group’s ongoing efforts to overhaul and update their payload arsenal in the wake of a 2019 leak of its hacking applications, which also doxxed numerous officers of the Iranian Ministry of Intelligence who have been concerned with APT34 functions.
“Iran backed APT34 exhibits no indication of slowing down, even more pushing its political agenda in the middle-east, with an ongoing concentrate on Lebanon — utilizing offensive cyber functions,” the researchers stated. “Whilst keeping its modus operandi and reusing aged tactics, the group proceeds to generate new and up-to-date applications to lower the achievable detection of their resources by security suppliers.”
Observed this post appealing? Adhere to THN on Fb, Twitter and LinkedIn to examine much more special material we write-up.
Some parts of this article are sourced from:
thehackernews.com

 Hackers Exploit Unpatched VPNs to Install Ransomware on Industrial Targets
Hackers Exploit Unpatched VPNs to Install Ransomware on Industrial Targets