An unknown sophisticated persistent threat (APT) team has been linked to a series of spear-phishing attacks targeting Russian government entities considering that the onset of the Russo-Ukrainian war in late February 2022.
“The campaigns […] are intended to implant a Distant Entry Trojan (RAT) that can be utilised to surveil the pcs it infects, and operate instructions on them remotely,” Malwarebytes reported in a technical report released Tuesday.
The cybersecurity business attributed the assaults with very low assurance to a Chinese hacking group, citing infrastructure overlaps between the RAT and Sakula Rat malware used by a risk actor identified as Deep Panda.
The attack chains, when leveraging distinct lures more than the class of two months, all used the similar malware barring modest variances in the resource code.

The marketing campaign is claimed to have commenced around February 26, days just after Russia’s military services invasion of Ukraine, with the email messages distributing the RAT under the guise of an interactive map of Ukraine (“interactive_map_UA.exe”).
The development once once more demonstrates danger actors’ abilities to adapt and change their attacks to globe situations, utilizing the most pertinent and up-to-date lures to optimize their likelihood of good results.
A 2nd early March attack wave mostly specific the point out-controlled RT Television set and involved the use of a rogue computer software repair for the Log4Shell vulnerability that produced headlines in late 2021.
Other than together with the patch in the variety of a compressed TAR file, the email concept also came with a PDF document with guidelines to put in the patch and stated the very best security practices to abide by, which include enabling two-factor authentication, applying Kaspersky antivirus, and refraining from opening or replying to suspicious email messages.
In a more attempt to increase the authenticity of the email, the document also contained a VirusTotal URL pointing to an unrelated file to give the effect that the Log4j patch file is not malicious.
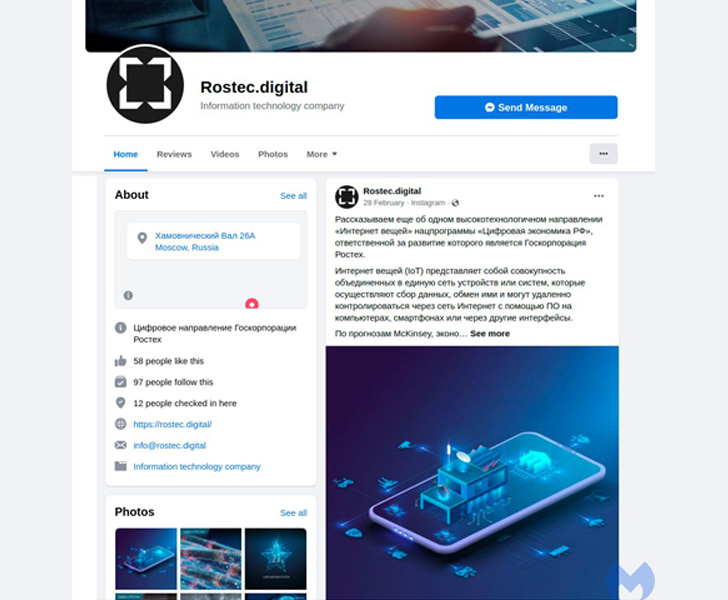
What is more, the email featured inbound links to an attacker-controlled area “rostec[.]digital” along with fraudulent profiles designed on Fb and Instagram alluding to the Russian defense conglomerate.

“Apparently, the risk actor developed the Fb website page in June 2021, 9 months in advance of it was utilised in this marketing campaign,” the scientists explained. “This was probably an try to attract followers, to make the webpage appear much more legitimate, and it suggests the APT group ended up setting up this marketing campaign prolonged before the invasion of Ukraine.”
The 3rd iteration of the attack that adopted made use of yet another destructive executable file — this time “create_rosteh4.exe” — in an endeavor to pass off the malware as although it’s from Rostec.
Finally, in mid-April 2022, the attackers pivoted to a occupation-themed phishing bait for Saudi Aramco, a Saudi Arabian petroleum and organic fuel corporation, the weaponized Microsoft Term doc performing as a set off for an infection sequence to deploy the RAT.
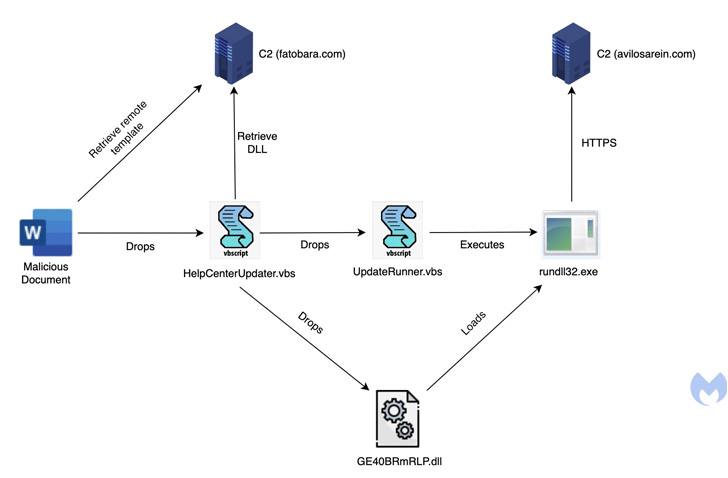
The DLL payload employs a assortment of highly developed methods to thwart examination, which include manage stream flattening and string obfuscation, although also incorporating features that make it possible for it to arbitrary data files sent from a distant server to the contaminated host and execute command-line guidance.
The conclusions carefully comply with findings from Check out Point that a Chinese adversarial collective with connections to Stone Panda and Mustang Panda qualified at least two investigate institutes found in Russia with a previously undocumented backdoor called Spinner.
Discovered this report fascinating? Adhere to THN on Fb, Twitter and LinkedIn to read additional special content we post.
Some parts of this article are sourced from:
thehackernews.com

 [Template] Incident Response for Management Presentation
[Template] Incident Response for Management Presentation