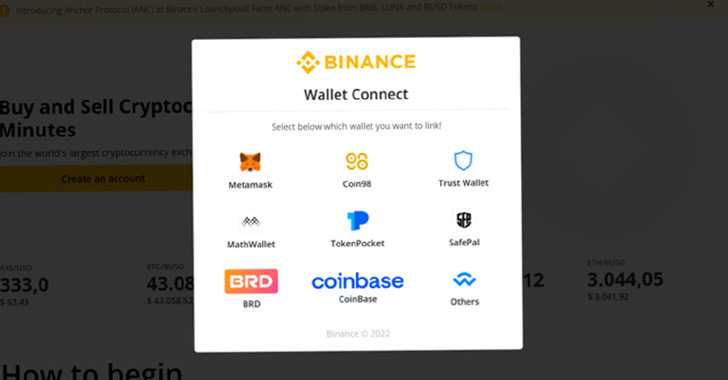
Cybercriminals are impersonating preferred crypto platforms such as Binance, Celo, and Trust Wallet with spoofed emails and faux login web pages in an endeavor to steal login information and deceptively transfer virtual money.
“As cryptocurrency and non-fungible tokens (NFTs) become more mainstream, and seize headlines for their volatility, there is a higher probability of far more folks falling target to fraud trying to exploit folks for electronic currencies,” Proofpoint explained in a new report.
“The rise and proliferation of cryptocurrency has also supplied attackers with a new approach of money extraction.”
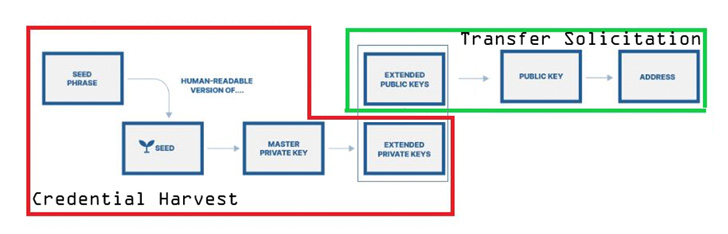
The concentrating on of delicate cryptocurrency info by threat actors was just lately echoed by the Microsoft 365 Defender Research Team, which warned about the rising risk of cryware wherein private keys, seed phrases, and wallet addresses are plundered with the intention of siphoning virtual currencies by indicates of fraudulent transfers.
The swift popularity of Web3 in modern several years has brought on a change in the phishing landscape, paving the way for a range of social engineering and exploitation mechanisms that are aimed at thieving cryptocurrencies in diverse means ranging from credential harvesting to the use of commodity stealer malware.
This incorporates spam email messages that include backlinks to rogue URLs that obtain malware and redirect end users to a credential harvesting landing web page or even fake lookalike variations of NFT investing platforms like OpenSea. Other campaigns prompt opportunity victims to enter their seed phrases.
In a phishing attack detected by the enterprise security firm in February 2022, a Have faith in Wallet-themed entice was noticed nudging email recipients, exclusively college students, to verify their wallets by coming into the restoration phrases.
A essential enabler of these tailored strategies is the relative ease with which counterfeit landing internet pages can be constructed working with phishing kits, permitting a lot less competent threat actors to distribute and control strategies at a massive scale.
Even more incentivizing the cybercriminal scheme are phishing-as-a-support (PHaaS) operators like BulletProofLink that give phishing templates, spamming services, bulletproof hosting providers, and credential assortment solutions, among the many others.
The kits, which are constantly up-to-date and expanded, are created to mimic different makes this kind of as blockchain[.]com as perfectly as other NFT and other cryptocurrency wallet services providers.
Also outstanding are business email compromise (BEC) attempts to facilitate the fraudulent transfer of electronic cash through messages that solicit cryptocurrency under the guise of seller payments and donation requests to help the Ukraine war work.

The results come as losses from crypto-relevant criminal offense jumped 79% 12 months-more than-year in 2021, with the U.S. Federal Trade Fee (FTC) noting that much more than 46,000 individuals have reported shedding about $1 billion in digital currencies to scams.
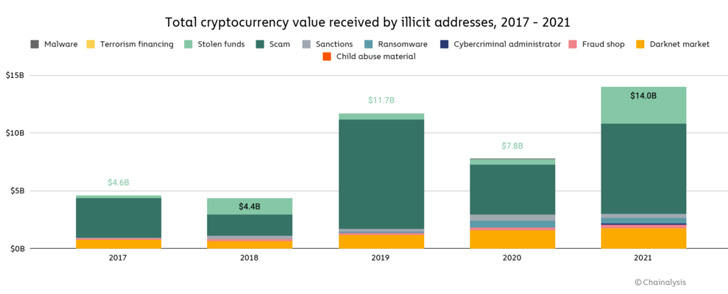
What is additional, Blockchain analytics firm Chainalysis found that cryptocurrency-centered criminal offense hit a new all-time large in 2021, even as illicit addresses obtained $14 billion over the program of the 12 months, up from $7.8 billion in 2020.
“Cybercriminal threats to cryptocurrency are not new, on the other hand as the basic general public encounters increasing adoption of cryptocurrency, men and women could be a lot more most likely to have interaction with social engineering lures employing this kind of themes,” Sherrod DeGrippo, vice president of threat investigation and detection at Proofpoint, mentioned.
“Crypto went mainstream with Superbowl advertisements this yr and threat actors have taken note of the prospect for a fast payday. There is no much easier process of money extraction than the illicit transfer of cryptocurrency.”
Observed this post attention-grabbing? Observe THN on Facebook, Twitter and LinkedIn to go through additional exceptional information we publish.
Some parts of this article are sourced from:
thehackernews.com

 HTC teases a potential 'Viverse' phone launch for June 28th
HTC teases a potential 'Viverse' phone launch for June 28th