A .NET-based evasive crypter named DarkTortilla has been made use of by risk actors to distribute a broad array of commodity malware as very well as targeted payloads like Cobalt Strike and Metasploit, possible given that 2015.
“It can also supply ‘add-on packages’ this sort of as more malicious payloads, benign decoy files, and executables,” cybersecurity firm Secureworks said in a Wednesday report. “It features sturdy anti-evaluation and anti-tamper controls that can make detection, assessment, and eradication tough.”
Malware delivered by the crypter features information and facts steakers and distant accessibility trojans (RATs) such as Agent Tesla, AsyncRat, NanoCore, and RedLine Stealer. “DarkTortilla has versatility that related malware does not,” the scientists observed.

Crypters are program tools that use a combination of encryption, obfuscation, and code manipulation of malware so as to bypass detection by security remedies.
The supply of DarkTortilla takes place by means of malicious spam e-mail which comprise archives with an executable for an original loader which is utilised to decode and launch a main processor module either embedded in just alone or fetched from text storage web pages this kind of as Pastebin.
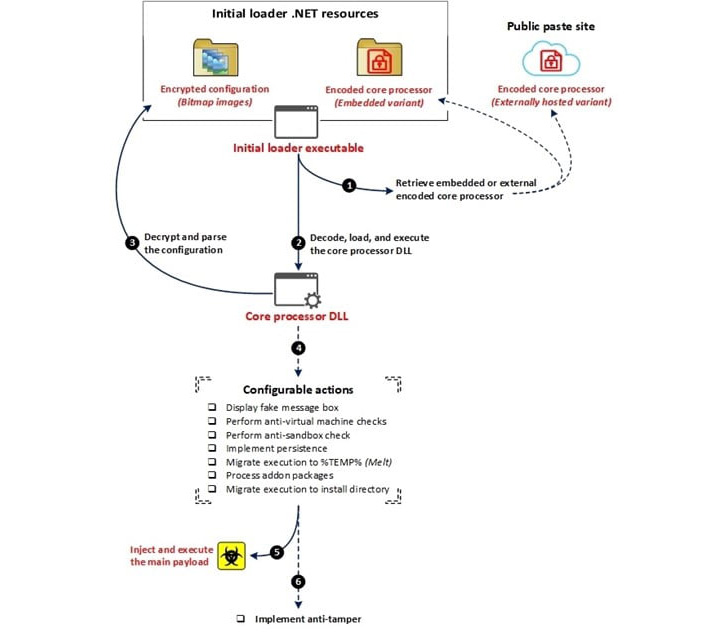
The main processor is then responsible for establishing persistence and injecting the key RAT payload into memory with out leaving a trail on the file method by means of an elaborate configuration file that also permits it to fall include-on deals, including keyloggers, clipboard stealers, and cryptocurrency miners.
DarkTortilla is even further noteworthy for its use of anti-tamper controls that make certain equally the processes used to execute the parts in memory are instantly rerun on termination.
Particularly, the persistence of the first loader is attained by implies of a next executable referred to as a WatchDog that is created to hold tabs on the specified course of action and rerun it should really it be killed.
This system is reminiscent of a similar system adopted by a risk actor referred to as Moses Personnel, which, previously this calendar year, was found relying on a watchdog-primarily based tactic to protect against any interruption to its payloads. Also employed are two other controls to assurance the continued execution of the dropped WatchDog executable itself and the persistence for the initial loader.
Secureworks mentioned it recognized an average of 93 one of a kind DarkTortilla samples being uploaded to the VirusTotal malware databases per 7 days in excess of a 17-month period from January 2021 to May possibly 2022.
“DarkTortilla is able of evading detection, is very configurable, and provides a vast variety of well-known and efficient malware,” the researchers concluded. “Its abilities and prevalence make it a formidable menace.”
Found this post exciting? Stick to THN on Facebook, Twitter and LinkedIn to read far more distinctive articles we submit.
Some parts of this article are sourced from:
thehackernews.com


 Motorola Edge hands-on: A return to (mid-range) form?
Motorola Edge hands-on: A return to (mid-range) form?