It’s very similar to Lazarus’s Manuscrypt malware, but the new spy ware is splattering alone onto govt corporations and ICS in a non-Lazarus-like, untargeted wave of attacks.
Researchers have tracked new spyware – dubbed “PseudoManuscrypt” due to the fact it’s identical to “Manuscrypt” malware from the Lazarus innovative persistent risk (APT) team – which is attempted to scribble by itself across much more than 35,000 targeted computers in 195 nations.
Kaspersky scientists said in a Thursday report that from Jan. 20 to Nov. 10, the actors guiding the vast campaign ended up targeting government corporations and industrial control devices (ICS) throughout a vary of industries, such as engineering, making automation, power, manufacturing, development, utilities and water administration. At the very least 7.2 p.c of all attacked computer systems are component of ICS, scientists mentioned.
Manuscrypt, aka NukeSped, is a family of malware equipment that have been applied in espionage campaigns in the previous. Just one these kinds of was a February spear-phishing campaign joined to Lazarus – a prolific North Korean APT – that used the Manuscrypt malware family’s ‘ThreatNeedle’ instrument cluster to attack defense firms.
Bogus Pirated Installers
The operators driving PseudoManuscrypt are utilizing fake pirated software program installer archives to originally down load the spyware on to targets’ systems.
The phony installers are for for “ICS-specific program, these kinds of as an application built to develop a MODBUS Learn System to acquire data from a PLC [programmable logic controller], as effectively as a lot more normal-goal computer software, which is nevertheless utilised on OT networks, this sort of as a essential generator for a SolarWinds software for network engineers and systems directors,” researchers reported.
They suspect that the threat actors are receiving the phony installers off a malware-as-a-company (MaaS) system that is providing them up to operators of several malicious campaigns, not just this commonly dispersed PseudoManuscrypt campaign.
On the other hand, Kaspersky also shared a display screen seize – shown beneath –of the listings for pretend installers they observed via a Google research.
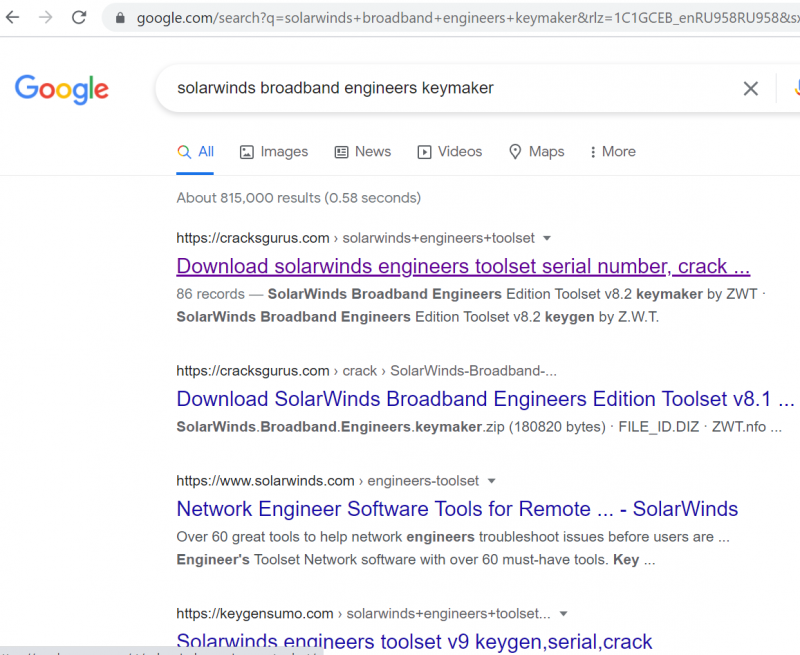
Fake installers located by using a Google lookup. Resource: Kaspersky.
Kaspersky outlined two variants of the module, each of which are outfitted with superior spyware abilities. One particular variation rode in through the notorious Glupteba botnet: a tough-to-scrub-off, 1 million-strong botnet of compromised Windows and internet of points (IoT) devices that Google’s Threat Evaluation Team (TAG) disrupted before this thirty day period.
The tie-in with Glupteba is a clue that PseudoManuscrypt’s could have originated on a MaaS system, researchers stated, presented that the botnet’s most important installer “is also dispersed by means of the pirated software package installer distribution system.”
Shanghaing Units with Full Spyware Abilities
Both equally of the module variants have brawny spy ware abilities, researchers mentioned. PseudoManuscrypt’s key module has a complete instrument package for spying every single which way, including, amongst many other things, the means to:
- Steal VPN relationship details
- Log keystrokes
- Get screenshots and consider screen video clips
- Use a system’s microphone to eavesdrop and history sound
- Filch clipboard knowledge
- Steal OS celebration log info – which also makes it achievable to steal Remote Desktop Protocol (RDP) authentication info.
In other words, it can entirely choose above infected systems, researchers mentioned: “Essentially, the performance of PseudoManuscrypt offers the attackers with pretty much entire manage of the infected process.”
Is This an APT On a Bender?
For an APT, this one’s weirdly promiscuous, what with those 35,000 attacks on devices across the world: a spread that does not point out that it’s specific. “Such a big quantity of attacked units is not attribute of the Lazarus team or APT attacks as a complete,” scientists mentioned.
The PseudoManuscrypt campaign assaults what they termed “a important variety of industrial and government companies, such as enterprises in the army-industrial elaborate and investigation laboratories.”
Similarities to Manuscrypt
Kasperskiy’s ICS-CERT crew initially detected the PseudoManuscrypt series of assaults in June, when the malware triggered antivirus detection developed to location Lazarus activity. The whole picture did not issue to Lazarus, having said that, specified the atypical, untargeted splatter of tens of countless numbers of assaults.
On the other hand, Kaspersky subsequently observed similarities between the new PseudoManuscrypt and Lazarus’s Manuscrypt malware
The PseudoManuscrypt malware hundreds its payload from the method registry and decrypts it, researchers defined, with the payload employing a registry site that’s special to just about every infected procedure.
“Both malicious courses load a payload from the program registry and decrypt it in the two conditions, a exclusive worth in the CLSID structure is applied to determine the payload’s place in the registry,” they reported. “The executable documents of each destructive systems have nearly similar export tables.”
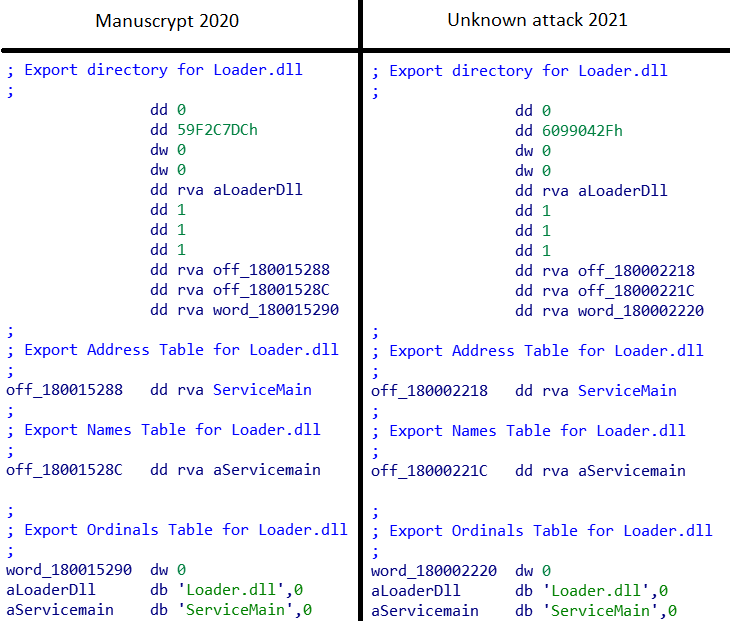
Comparison of PseudoManuscrypt and Manuscrypt export tables. Source: Kaspersky.
The two malwares also use identical executable file naming formats.
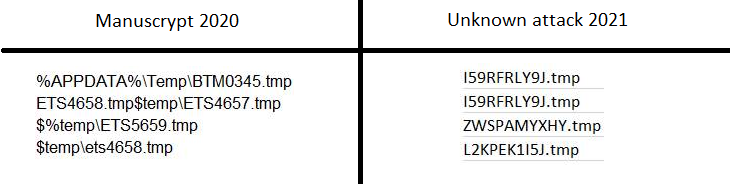
Executable file names. Source: Kaspersky.
Another commonality among the two malwares is that some of the organizations attacked by PseudoManuscrypt have business and manufacturing ties with victims of the Lazarus ThreatNeedle marketing campaign, Kaspersky mentioned.
With regards to the geographic reach of the PseudoManuscrypt marketing campaign, almost a 3rd – 29.4 p.c – of the targeted, non-ICS computers are situated in Russia (10.1 %), India (10 percent) and Brazil (9.3 p.c), Kaspersky uncovered, which is a distribution which is related to that for ICS desktops.
“The quantity of attacked methods is large and we see no apparent target on unique industrial corporations,” they concluded. “However, the point that a large amount of ICS desktops throughout the world (a lot of hundreds according to our telemetry by itself – and in reality really very likely to be substantially extra) have been attacked in this campaign unquestionably helps make it a threat that deserves the incredibly closest consideration of experts dependable for the security and safety of shop-floor units and their steady procedure.”
Who’s Powering PseudoManuscrypt?
Researchers stated these clues as to the adversary’s origin or its ties:
Execution Move
In a specific drilldown on its ICS-CERT website, Kaspersky scientists mentioned that the execution flow for PseudoManuscrypt set up has many doable variants, with malware installers downloading and executing hundreds of other malicious systems, such as spy ware, backdoors, cryptocurrency miners and adware.
As nicely, at just about every stage, they noticed a slew of diverse droppers mounted and modules downloaded, with diverse modules developed to steal facts and every single module possessing its personal command-and-regulate (C2) server.
Down below is the execution circulation for a single of the two variants noticed by Kaspersky: the a single that utilizes the Glupteba botnet’s infrastructure and malware installers.
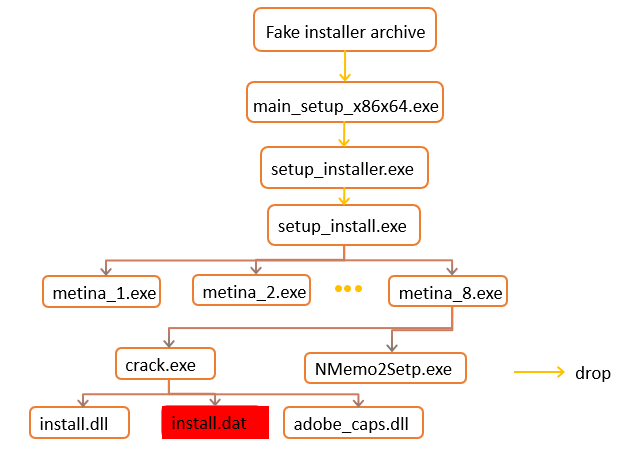
Execution flow for the variant that takes advantage of the Glupteba infrastructure and malware installers. Source: Kaspersky.
Scientists pointed to nevertheless another variant of the PseudoManuscrypt installer which is been described by BitDefender that was downloaded making use of the url hxxps://jom[.]diregame[.]reside/userf/2201/google-recreation.exe on Could 17, 2021.
“It is worthy of noting that at distinct periods the backlink could be made use of to down load malware from unique households,” Kaspersky claimed.
A Bit of a Head-Scratcher
The fact that industrial entities are tempting targets the two for monetarily enthusiastic adversaries and cyberespionage is not news, Kaspersky mentioned in summing up its report. “Industrial companies are some of the most coveted targets for cybercriminals equally for money gain and intelligence collecting,” in accordance to the writeup, which pointed to 2021 having found “significant desire in industrial businesses from nicely-acknowledged APT groups like Lazarus and APT41.”
APT 41 – aka Barium, Winnti, Wicked Panda or Wicked Spider – is a China-linked threat team known for country-state-backed cyber-espionage exercise as very well as fiscal cybercrime.
But Kaspersky stated that it can’t say for certain no matter whether the PseudoManuscrypt marketing campaign is “pursuing prison mercenary objectives or plans correlating with some governments’ interests.” Nonetheless, “the simple fact that attacked methods consist of personal computers of high-profile corporations in various countries makes us assess the danger level as superior,” researchers claimed.
They extra, “The large amount of engineering computers attacked, including programs utilized for 3D and bodily modeling, the progress and use of digital twins raises the issue of industrial espionage as one of the doable objectives of the campaign.”
Verify out our free approaching dwell and on-desire on-line town halls – exceptional, dynamic conversations with cybersecurity experts and the Threatpost local community.
Some parts of this article are sourced from:
threatpost.com


