The maintainers of the PHP programming language have issued an update relating to the security incident that came to gentle late final thirty day period, stating that the actors could have gotten keep of a consumer database that contains their passwords to make unauthorized adjustments to the repository.
“We no for a longer time feel the git.php.net server has been compromised. Having said that, it is attainable that the grasp.php.net user databases leaked,” Nikita Popov stated in a message posted on its mailing listing on April 6.
On March 28, unidentified actors used the names of Rasmus Lerdorf and Popov to push malicious commits to the “php-src” repository hosted on the git.php.net server that included introducing a backdoor to the PHP supply code in an instance of a software source chain attack.
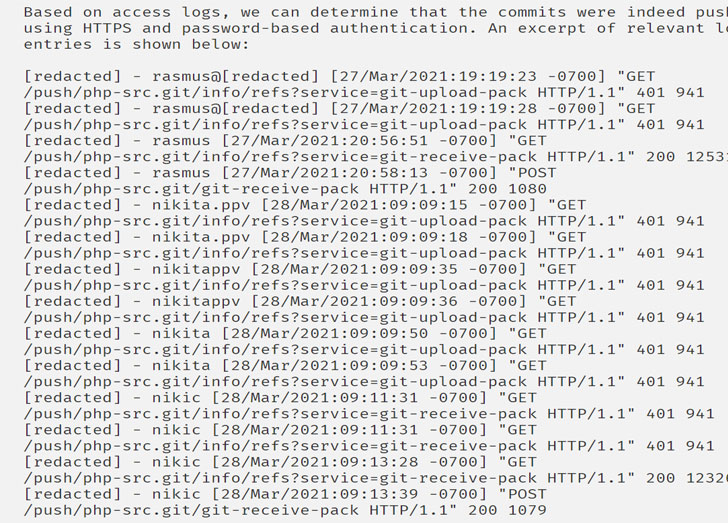
Though this was at first dealt with as a compromise of the git.php.net server, additional investigation into the incident has disclosed that the commits ended up a outcome of pushing them making use of HTTPS and password-primarily based authentication, primary them to suspect a feasible leak of the learn.php.net person database.
The “git.php.net (intentionally) assistance[s] pushing adjustments not only through SSH (employing the Gitolite infrastructure and public key cryptography), but also through HTTPS,” Popov claimed. “The latter did not use Gitolite, and rather utilized git-http-backend guiding Apache 2 Digest authentication from the learn.php.net consumer database.”
“It is notable that the attacker only would make a couple guesses at usernames, and correctly authenticates when the proper username has been located. Even though we you should not have any particular proof for this, a probable explanation is that the user database of grasp.php.net has been leaked, even though it is unclear why the attacker would will need to guess usernames in that circumstance.”
Furthermore, the grasp.php.net authentication method is claimed to be on a incredibly previous running process and a version of PHP, elevating the risk that the attackers may possibly have also exploited a vulnerability in the computer software to phase the attack.
As a consequence, the maintainers have migrated learn.php.net to a new primary.php.net program with help for TLS 1.2, in addition to resetting all existing passwords and storing passwords making use of bcrypt as an alternative of a simple MD5 hash.
Found this short article appealing? Comply with THN on Fb, Twitter and LinkedIn to read additional special information we submit.
Some parts of this article are sourced from:
thehackernews.com


 The National Archives won't be able to host Donald Trump's tweets on Twitter
The National Archives won't be able to host Donald Trump's tweets on Twitter