Action dubbed ‘Raspberry Robin’ employs Microsoft Conventional Installer and other reputable processes to communicate with threat actors and execute nefarious commands. Credit: Crimson …
USB-based Wormable Malware Targets Windows InstallerRead More


Action dubbed ‘Raspberry Robin’ employs Microsoft Conventional Installer and other reputable processes to communicate with threat actors and execute nefarious commands. Credit: Crimson …
USB-based Wormable Malware Targets Windows InstallerRead More
Cybersecurity researchers have discovered a new Windows malware with worm-like abilities and is propagated by indicates of detachable USB equipment. Attributing the malware to a cluster named …
Researchers Warn of ‘Raspberry Robin’ Malware Spreading via External DrivesRead More

A trainee solicitor and specific police constable has been handed a two-year suspended sentence soon after making use of encrypted channels to article messages about boy or girl sexual abuse. Jack …
Special Police Constable Used Encrypted Chat to Post Child Abuse ContentRead More
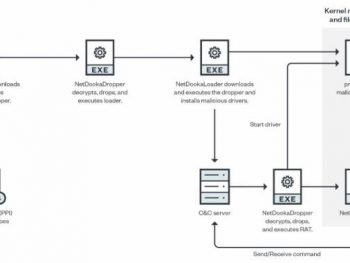
A spend-for every-set up (PPI) malware support recognized as PrivateLoader has been noticed distributing a "rather advanced" framework named NetDooka, granting attackers comprehensive command around …
Hackers Using PrivateLoader PPI Service to Distribute New NetDooka MalwareRead More

Ukrainian hacktivists reportedly disrupted liquor shipments in Russia just after committing distributed denial of assistance (DDoS) attacks towards a critical online portal, in accordance to area …
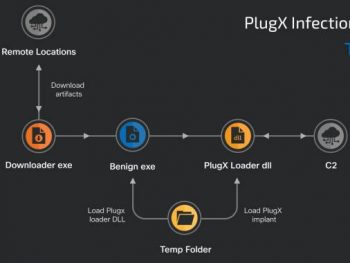
The China-primarily based risk actor identified as Mustang Panda has been noticed refining and retooling its techniques and malware to strike entities positioned in Asia, the European Union, Russia, …
Experts Uncover New Espionage Attacks by Chinese ‘Mustang Panda’ HackersRead More

Google has introduced month-to-month security patches for Android with fixes for 37 flaws throughout diverse parts, just one of which is a resolve for an actively exploited Linux kernel vulnerability …
Google Releases Android Update to Patch Actively Exploited VulnerabilityRead More

A code-hosting system employed by tens of hundreds of thousands of software builders around the globe is employing required two-variable authentication (2FA) for all code contributors. In …

The proprietor of a Delaware laptop fix shop, who alerted the FBI to the contents of a laptop reportedly owned by President Joe Biden’s son, Hunter, is suing a politician and many news media outlets …
Hunter Biden Laptop Repairman Sues Over Hacker AllegationsRead More

A cyber-attack that compromised the individual details of hundreds of 1000's of students in New York has impacted further college students based mostly in Colorado. The security incident occurred at …
Illuminate Data Breach Impacts More School DistrictsRead More
