Entities in Armenia have come beneath a cyber attack employing an up-to-date variation of a backdoor known as OxtaRAT that permits distant accessibility and desktop surveillance.
“The software capabilities include looking for and exfiltrating information from the contaminated device, recording the online video from the web camera and desktop, remotely controlling the compromised device with TightVNC, installing a web shell, undertaking port scanning, and more,” Test Issue Exploration claimed in a report.
The hottest marketing campaign is mentioned to have commenced in November 2022 and marks the initial time the menace actors behind the action have expanded their target past Azerbaijan.
“The menace actors powering these attacks have been concentrating on human legal rights organizations, dissidents, and independent media in Azerbaijan for several a long time,” the cybersecurity business famous, calling the campaign Operation Silent Watch.
The late 2022 intrusions are important, not minimum due to the fact of the variations in the an infection chain, the techniques taken to enhance operational security, and equip the backdoor with more ammunition.
The starting stage of the attack sequence is a self-extracting archive that mimics a PDF file and bears a PDF icon. Launching the purported “document” opens a decoy file when also stealthily executing destructive code hidden inside an image.
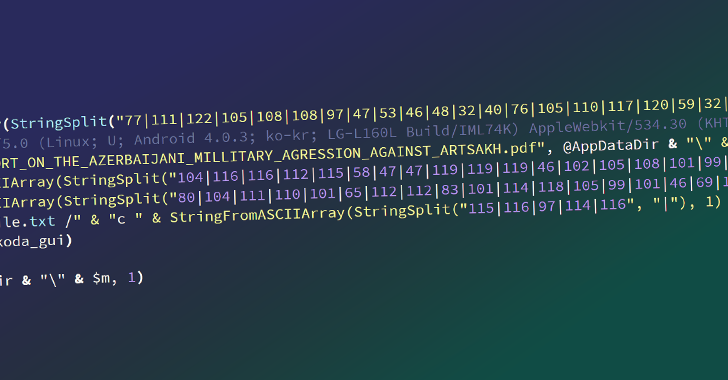
A polyglot file that combines compiled AutoIT script and an picture, OxtaRAT functions commands that permit the risk actor to operate additional commands and data files, harvest sensitive details, execute reconnaissance and surveillance through a web digicam, and even pivot to other.
OxtaRAT has been set to use by the adversary as much back as June 2021, albeit with substantially reduced functionality, indicating an attempt to regularly update its toolset and vogue it into a Swiss Army knife malware.
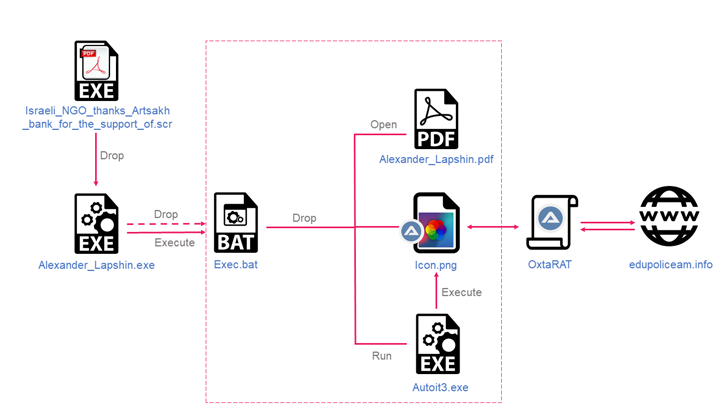
The November 2022 attack also stands out for a variety of reasons. The 1st is that the .SCR documents that activate the destroy chain currently include the OxtaRAT implant as opposed to acting as a downloader to fetch the malware.
“This will save the actors from needing to make additional requests for binaries to the C&C server and attracting unneeded attention, as effectively as hides the major malware from being quickly identified on the contaminated device, as it appears to be like like a standard impression and bypasses variety-unique protections,” Check out Place explained.
The second putting element is the geofencing of command-and-handle (C2) domains that host the auxiliary tools to Armenian IP addresses.
Also of note is the potential of OxtaRAT to run commands for port scanning and to exam the velocity of an internet relationship, that latter of which is probably used as a way to cover the “extensive” information exfiltration.
“OxtaRAT, which earlier experienced typically area recon and surveillance capabilities, can now be utilized as a pivot for active reconnaissance of other devices,” Check out Stage reported.
“This may perhaps point out that the danger actors are preparing to prolong their most important attack vector, which is presently social engineering, to infrastructure-dependent attacks. It also might be a indication that the actors are moving from focusing on men and women to concentrating on a lot more sophisticated or company environments.”
“The underlying danger actors have been maintaining the improvement of Vehicle-IT based mostly malware for the past seven many years, and are using it in surveillance campaigns whose targets are reliable with Azerbaijani interests.”
Observed this posting exciting? Abide by us on Twitter and LinkedIn to read a lot more exceptional content material we article.
Some parts of this article are sourced from:
thehackernews.com

 New Mirai Botnet Variant ‘V3G4’ Exploiting 13 Flaws to Target Linux and IoT Devices
New Mirai Botnet Variant ‘V3G4’ Exploiting 13 Flaws to Target Linux and IoT Devices