Malicious email attachments with macros are just one of the most widespread strategies hackers get in through the doorway. Huntress security researcher John Hammond discusses how danger hunters can combat back again.
Any cybersecurity attack — no matter if it be a breach, an incident or any type of compromise — starts off with hackers acquiring in by way of the doorway. Menace actors and adversaries rely on attaining code execution on a concentrate on process which they can then leverage to do additional damage—a phase frequently referred to as initial accessibility.
A lot more frequently than not, the best way for an attacker to get preliminary accessibility is by exploiting the human vulnerability. This involves tricking an stop consumer into having some motion that in the long run provides the danger actor a lot more power than they had in advance of. They lay a trap and suggest a cleverly disguised lie to as lots of prospective victims as probable. Even nevertheless a menace actor may endeavor to idiot a thousand users at a person time, they only require one to drop for the charade.
Danger actors layout and deliver this plan ordinarily via email—the simplest way to put electronic articles in front of any unique. In today’s world, this is common language: “Be cautious not to fall for phishing email messages.”
For many years, the security sector has tried to coach people to keep vigilant towards phishing emails with the boilerplate fundamental principles you have listened to time and time once again: “Look for undesirable grammar or spelling mistakes,” “double-check the sending handle,” “hover above the backlink,” and so on. Even though these saturated lessons may well enable ward off the reduced-hanging fruit, nicely-crafted phishing e-mail from refined actors might be truly really hard to location.
Bait on the Entice
Phishing e-mails or any type of digital deception carry similar qualities, but could possibly have different wished-for results. The most effective phishing campaigns do three matters:
- Established the phase with a pretense
- Strike panic with a danger
- Demand action through urgency
Pretense ordinarily tugs at a person’s heartstrings or capitalizes on actual-earth threats or existing functions, this sort of as the COVID-19 pandemic, taxes or elections, cryptocurrencies, or even blackmail and extortion (“I have your password/I have you on webcam” threats).
The over-all purpose of a phish, even so, varies.
Credential Harvesting
The adversary might set up a “lookalike” web site, masquerading as a web page that the consumer expected and supposed to go to, but which as a substitute provides username and password combos to the risk actor when victims attempt to log in.
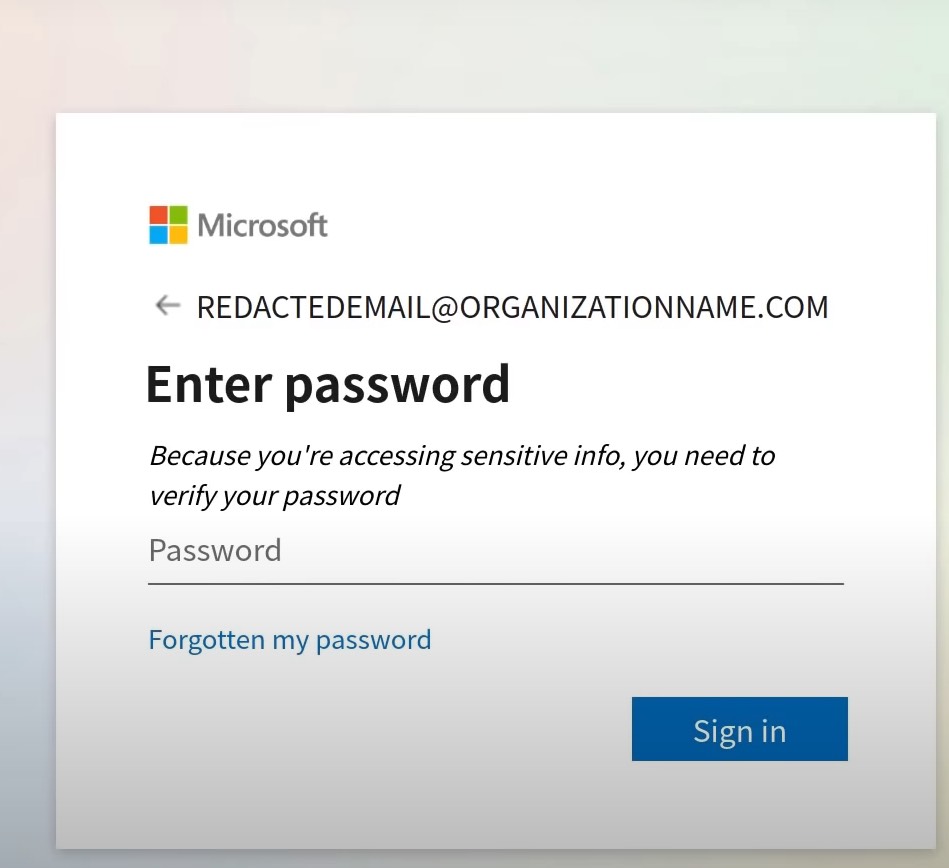
Source: Huntress.
Session Hijacking
The adversary also may possibly implant code on a staged internet site or HTML file, forcing the user’s browser to download a file or depart guiding cookies that can be made use of for later on steps performed by the threat actor:
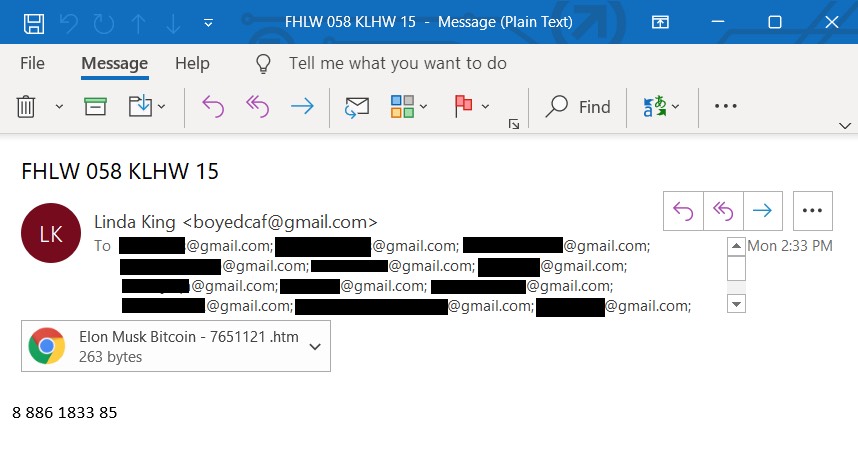
Resource: Huntress.
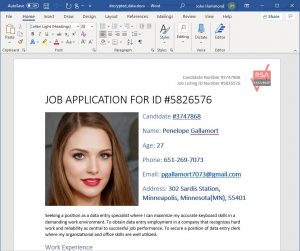
Malicious File Attachments
The adversary most typically having said that attaches a specific file to an email, suggesting that the consumer download it and open it on their very own volition. This file usually masquerades as a legitimate doc, but will as an alternative execute code on being opened.

Resource: Huntress.
Let us transform our focus to this file-attachment attack vector—specifically, malicious Microsoft Office environment files, which can run code with a macro.
Macro Malware
One exceptionally common file attachment variety involved in phishing e-mail are Microsoft Business office documents (like Phrase, PowerPoint or Excel)—masquerading as harmless data files that any consumer or employee may possibly open up on a day by day foundation.
Contemplate an HR representative or a employing supervisor at any organization. Their legit job function is to receive and tackle apps from interested applicants, quite often opening incoming e-mail and downloading their attachments, most likely to perspective an incoming prospect’s resume.
Malicious Business paperwork, or maldocs, can execute code by using macros if they are offered express user permission. As soon as opened, the adversary should go on the charade and trick the consumer to click on “Enable Editing” or “Enable Content” for a macro to run.
Resource: Huntress.
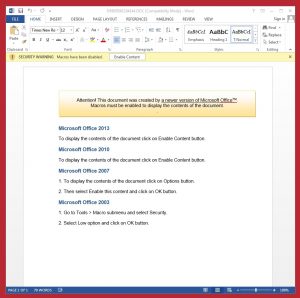
Macro code will execute on clicking the “Enable Content” via a particular operate handler:
Sub Document_Open up()
SubstitutePage
Conclusion Sub
Sub AutoOpen()
SubstitutePage
Finish Sub
Sub SubstitutePage()
ActiveDocument.Content.Select
Assortment.Delete
ActiveDocument.AttachedTemplate.AutoTextEntries(“Candidate”).Insert Wherever:=Range.Variety, RichText=True
Close Sub
The AutoOpen() or Doc_Open up() subroutines define the code that will run promptly after the Place of work doc is opened or the consumer enables material. In the snippet of code higher than, the process to emulate “decrypting” the content is shown—simply switching out the initial doc with written content that is saved in an attached template, having edge of a different element of Microsoft Word to cover points from the user.
Instruments of the Trade: Evaluation Techniques
There are quite a few resources out there to help danger hunters inside providers discover macros and capture them right before they detonate. Here are two.
Olevba
This instrument tends to be run on Linux as it is a Python device. It does a good job of obtaining important indicators that could established off an alarm for a risk hunter. It generates an output that presents danger scientists a chunk of macro code to see if any of that code warrants extra focus.
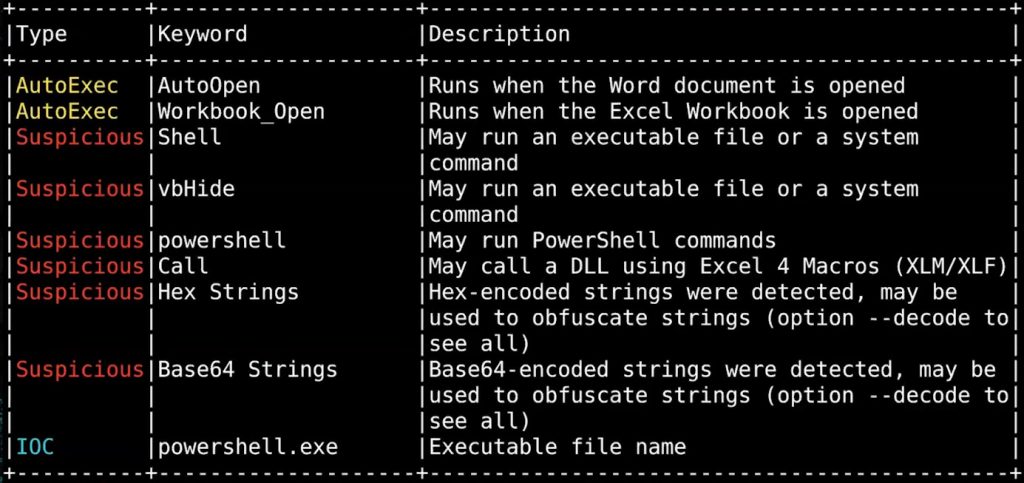
Source: Huntress.
ViperMonkey
This software will take a diverse strategy than Olevba. Whereas Olevba decodes back-end VBAproject.bin documents in .ZIP data files and generates the supply code, ViperMonkey emulates VisualBasic (VB) scripts to a specified extent. It can operate VB shellcode and see what it does—all devoid of posing any genuine hurt to buyers. It can even bypass evasive tactics threat actors take when it comes to malicious Office files, such as splitting up the code through the document to make it more durable to establish. ViperMonkey can uncover those people parts of code and piece them collectively to be analyzed.

Source: Huntress.
The Perpetual Cyber Struggle
Hiding malware inside of Office documents is not a new trick—it’s just a pretty effective one particular. Regardless of realizing the cons and noticing the purple flags, we’re observing a craze of more qualified and methodical phishing campaigns. And this could leave several defenders experience like they’re taking part in a match of whack-a-mole and reacting to the new tips and tactics that attackers are employing. But as attackers have gotten superior at social engineering and acquiring means to dupe consumers and their technology, we like to believe that us defenders are definitely soaring to the challenge and improved organized for battle.
John Hammond is a senior security researcher at Huntress.
Love extra insights from Threatpost’s Infosec Insiders neighborhood by browsing our microsite.
Some parts of this article are sourced from:
threatpost.com


 Volvo Hit by Cyber-thieves
Volvo Hit by Cyber-thieves