A new unpatched security vulnerability has been disclosed in the open-resource Horde Webmail shopper that could be exploited to attain distant code execution on the email server merely by sending a specifically crafted email to a sufferer.
“The moment the email is viewed, the attacker can silently get more than the finish mail server with out any even further person interaction,” SonarSource reported in a report shared with The Hacker Information. “The vulnerability exists in the default configuration and can be exploited with no awareness of a qualified Horde occasion.”
The issue, which has been assigned the CVE identifier CVE-2022-30287, was documented to the vendor on February 2, 2022. The maintainers of the Horde Task did not straight away answer to a ask for for remark pertaining to the unresolved vulnerability.

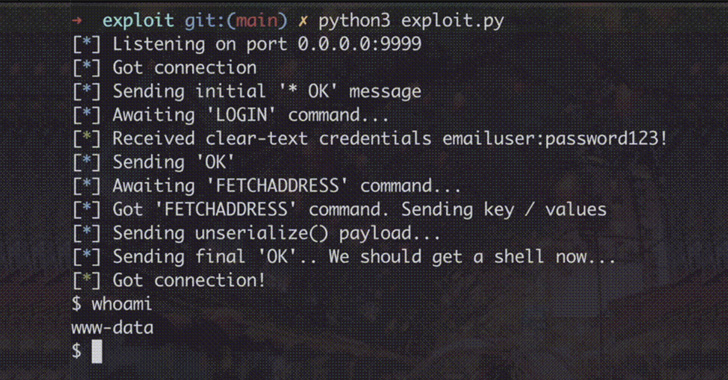
At its core, the issue tends to make it possible for an authenticated user of a Horde occasion to run malicious code on the fundamental server by getting advantage of a quirk in how the shopper handles get in touch with lists.
This can then be weaponized in connection with a cross-internet site ask for forgery (CSRF) attack to set off the code execution remotely.
CSRF, also referred to as session riding, occurs when a web browser is tricked into executing a malicious motion in an software to which a user is logged in. It exploits the believe in a web software has in an authenticated user.
“As a end result, an attacker can craft a destructive email and include an exterior graphic that when rendered exploits the CSRF vulnerability devoid of more interaction of a target: the only prerequisite is to have a sufferer open the destructive email.”
The disclosure will come a tiny in excess of 3 months right after a different nine-12 months-aged bug in the software program came to light-weight, which could permit an adversary to attain full accessibility to email accounts by previewing an attachment. This issue has considering the fact that been fixed as of March 2, 2022.

In light-weight of the reality that Horde Webmail is no extended actively preserved since 2017 and dozens of security flaws have been documented in the productiveness suite, people are proposed to switch to an choice support.
“With so a great deal have faith in staying put into webmail servers, they naturally grow to be a highly
interesting focus on for attackers,” the researchers mentioned.
“If a complex adversary could compromise a webmail server, they can intercept each individual despatched and gained email, entry password-reset back links, sensitive files, impersonate personnel and steal all credentials of buyers logging into the webmail
services.”
Uncovered this article intriguing? Adhere to THN on Facebook, Twitter and LinkedIn to examine much more special content we write-up.
Some parts of this article are sourced from:
thehackernews.com

 Loupedeck’s Live S gives creators an alternative to the Stream Deck
Loupedeck’s Live S gives creators an alternative to the Stream Deck