Buyers browsing for TeamViewer remote desktop software package on look for engines like Google are becoming redirected to malicious backlinks that fall ZLoader malware onto their methods although simultaneously embracing a stealthier an infection chain that permits it to linger on contaminated units and evade detection by security alternatives.
“The malware is downloaded from a Google advertisement published as a result of Google Adwords,” scientists from SentinelOne explained in a report released on Monday. “In this marketing campaign, the attackers use an indirect way to compromise victims instead of making use of the vintage method of compromising the victims immediately, these types of as by phishing.”
Initial identified in 2016, ZLoader (aka Silent Night time and ZBot) is a absolutely-showcased banking trojan and a fork of another banking malware identified as ZeuS, with more recent versions employing a VNC module that grants adversaries remote entry to target devices. The malware is in lively advancement, with prison actors spawning an array of variants in latest a long time, no much less fuelled by the leak of ZeuS source code in 2011.
The latest wave of attacks is thought to focus on consumers of Australian and German economic establishments with the major objective of intercepting users’ web requests to the banking portals and thieving bank credentials. But the marketing campaign is also noteworthy since of the measures it normally takes to keep less than the radar, which includes managing a sequence of instructions to conceal the destructive exercise by disabling Windows Defender.
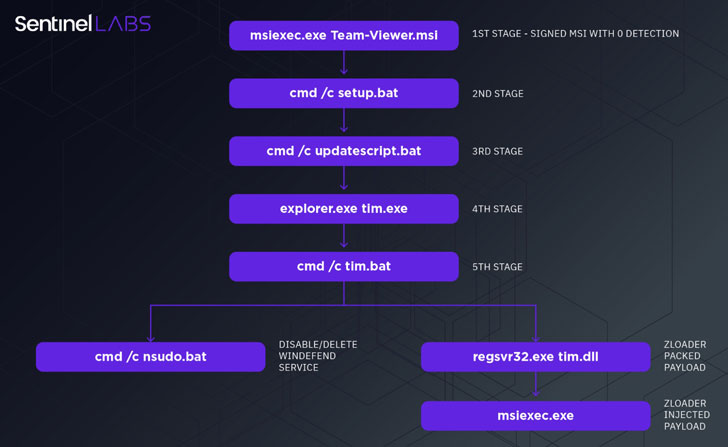
The infection chain commences when a user clicks on an ad shown by Google on the search success webpage and is redirected to the bogus TeamViewer site under the attacker’s regulate, therefore tricking the victim into downloading a rogue but signed variant of the application (“Team-Viewer.msi”). The bogus installer functions as the first phase dropper to set off a collection of actions that require downloading upcoming-stage droppers aimed at impairing the defenses of the equipment and eventually downloading the ZLoader DLL payload (“tim.dll”).
“At very first, it disables all the Windows Defender modules by means of the PowerShell cmdlet Set-MpPreference,” SentinelOne Senior Risk Intelligence Researcher Antonio Pirozzi reported. “It then adds exclusions, these kinds of as regsvr32, *.exe, *.dll, with the cmdlet Insert-MpPreference to conceal all the components of the malware from Windows Defender.”
The cybersecurity agency explained it uncovered supplemental artifacts that mimic well known applications like Discord and Zoom, suggesting that the attackers experienced various campaigns ongoing over and above leveraging TeamViewer.
“The attack chain analyzed in this analysis displays how the complexity of the attack has grown in get to reach a larger level of stealthiness, making use of an option to the traditional method of compromising victims by means of phishing email messages,” Pirozzi discussed. “The technique utilised to install the initial phase dropper has been transformed from socially engineering the sufferer into opening a destructive doc to poisoning the user’s web lookups with inbound links that deliver a stealthy, signed MSI payload.”
Observed this report exciting? Follow THN on Fb, Twitter and LinkedIn to read through extra unique material we write-up.
Some parts of this article are sourced from:
thehackernews.com

 Financial Services Firms Spend Over $2m on Ransomware Recovery
Financial Services Firms Spend Over $2m on Ransomware Recovery