A new malware resource that enables cybercriminal actors to construct malicious Windows shortcut (.LNK) documents has been noticed for sale on cybercrime discussion boards.
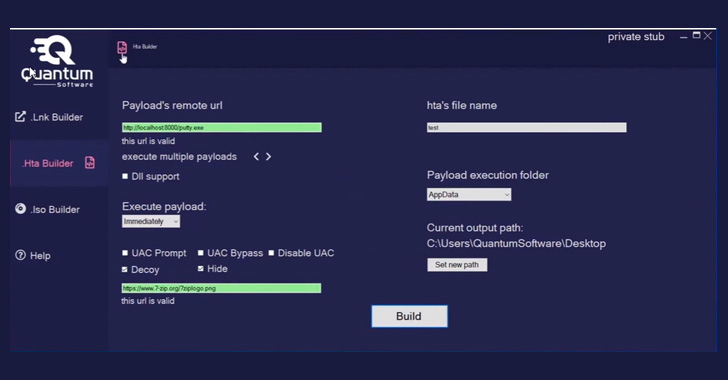
Dubbed Quantum Lnk Builder, the computer software would make it doable to spoof any extension and opt for from over 300 icons, not to mention aid UAC and Windows SmartScreen bypass as nicely as “various payloads per .LNK” file. Also made available are abilities to create .HTA and disk image (.ISO) payloads.
Quantum Builder is out there for lease at distinct rate details: €189 a thirty day period, €355 for two months, €899 for six months, or as a one particular-off lifetime acquire for €1,500.
“.LNK documents are shortcut data files that reference other documents, folders, or purposes to open up them,” Cyble scientists reported in a report. “The [threat actor] leverages the .LNK data files and drops destructive payloads applying LOLBins [living-off-the-land binaries].”
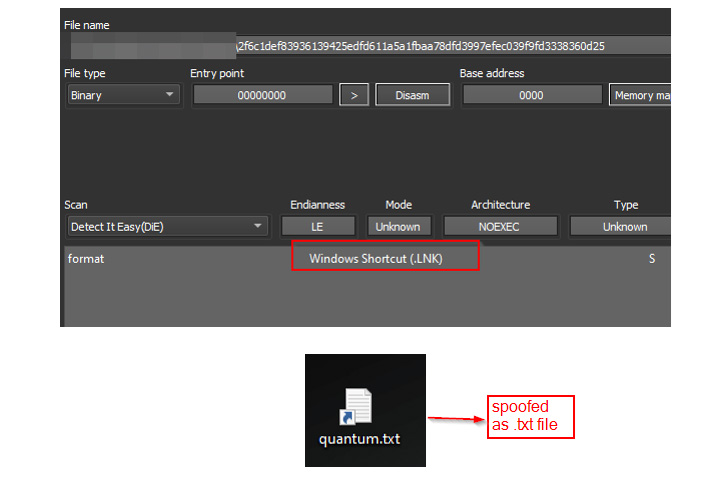
Early evidence of malware samples working with Quantum Builder in the wild is mentioned to day again to May possibly 24, masquerading as harmless-seeking textual content documents (“exam.txt.lnk”).
“By default, Windows hides the .LNK extension, so if a file is named as file_identify.txt.lnk, then only file_identify.txt will be noticeable to the user even if the exhibit file extension choice is enabled,” the scientists reported. “For these types of explanations, this could possibly be an attractive possibility for TAs, utilizing the .LNK data files as a disguise or smokescreen.”
Launching the .LNK file executes PowerShell code that, in convert, operates a HTML application (“bdg.hta”) file hosted on Quantum’s internet site (“quantum-software program[.]on the internet”) utilizing MSHTA, a legit Windows utility that is used to run HTA files.
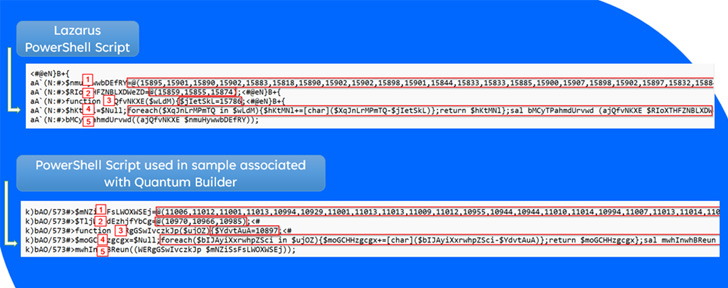
Quantum Builder is reported to share ties with the North Korean-based Lazarus Team based mostly on resource code-stage overlaps in the tool and the latter’s modus operandi of leveraging .LNK files for delivering even more phase payloads, indicating its opportunity use by APT actors in their assaults.

The development comes as operators at the rear of Bumblebee and Emotet are shifting to .LNK files as a conduit to cause the an infection chains next Microsoft’s choice to disable Visual Essential for Applications (VBA) macros by default throughout its goods previously this year.
Bumblebee, a substitution for BazarLoader malware first spotted in March, capabilities as a backdoor created to give the attackers persistent accessibility to compromised programs and a downloader for other malware, including Cobalt Strike and Sliver.
The malware’s capabilities have also designed it a software of choice for threat actors, with 413 incidents of Bumblebee an infection documented in May possibly 2022, up from 41 in April, in accordance to Cyble.
“Bumblebee is a new and hugely sophisticated malware loader that employs intensive evasive maneuvers and anti-evaluation tips, together with intricate anti-virtualization techniques,” the researchers reported. “It is probable to turn out to be a well-liked instrument for ransomware teams to provide their payload.”
Uncovered this post fascinating? Observe THN on Facebook, Twitter and LinkedIn to read much more exclusive information we post.
Some parts of this article are sourced from:
thehackernews.com


 Wearable arm muscles could help overcome upper body injuries
Wearable arm muscles could help overcome upper body injuries