Researchers on Tuesday disclosed a novel malware that employs a variety of tips to keep less than the radar and evade detection, when stealthily able of executing arbitrary commands on contaminated methods.
Known as ‘Pingback,’ the Windows malware leverages Internet Manage Concept Protocol (ICMP) tunneling for covert bot communications, making it possible for the adversary to benefit from ICMP packets to piggyback attack code, in accordance to an assessment printed right now by Trustwave.

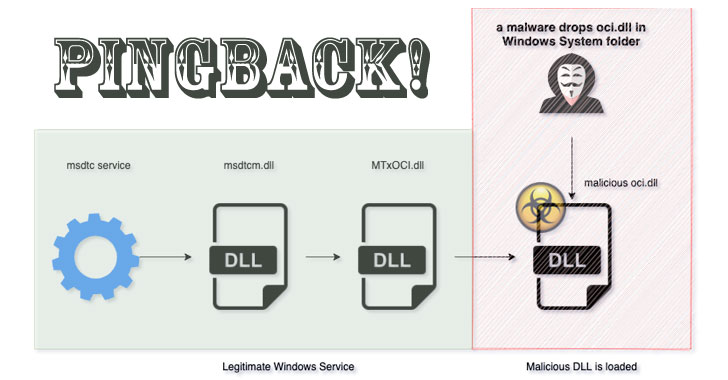
Pingback (“oci.dll”) achieves this by finding loaded as a result of a respectable support known as MSDTC (Microsoft Dispersed Transaction Coordinator) — a element accountable for handling databases functions that are dispersed about various equipment — by getting edge of a process known as DLL search purchase hijacking, which requires working with a authentic software to preload a destructive DLL file.
Naming the malware as one particular of the plugins expected for supporting Oracle ODBC interface in MSDTC is critical to the attack, the scientists mentioned. Even though MSDTC is not configured to operate immediately on startup, a VirusTotal sample submitted in July 2020 was observed to set up the DLL file into the Windows System listing and get started the MSDTC company to attain persistence, elevating the chance that a individual executable is essential to setting up the malware.
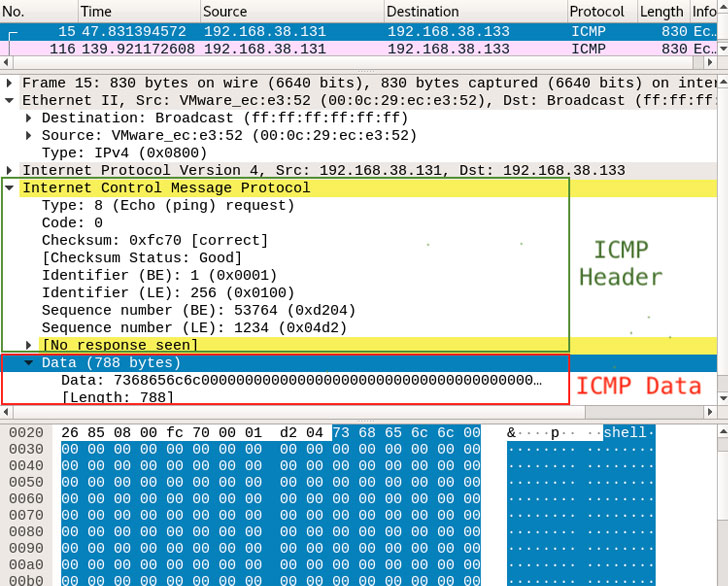
On productive execution, Pingback resorts to applying the ICMP protocol for its primary conversation. ICMP is a network layer protocol mainly used for sending error messages and operational information and facts, say, a failure alert when a further host results in being unreachable.
Particularly, Pingback takes gain of an Echo ask for (ICMP message type 8), with the concept sequence figures 1234, 1235, and 1236 denoting the sort of info contained in the packet — 1234 remaining a command or details, and 1235 and 1236 staying the acknowledgment for receipt of information on the other close. Some of the instructions supported by the malware contain the capability to run arbitrary shell instructions, down load and upload files from and to the attacker’s host, and execute malicious commands on the infected device.
An investigation into the malware’s initial intrusion route is ongoing.
“ICMP tunneling is not new, but this certain sample piqued our interest as a genuine-world illustration of malware applying this system to evade detection,” the scientists reported. “ICMP is practical for diagnostics and effectiveness of IP connections, [but] it can also be misused by destructive actors to scan and map a target’s network natural environment. While we are not suggesting that ICMP must be disabled, we do recommend putting in spot checking to enable detect this kind of covert communications in excess of ICMP.”
Observed this article fascinating? Follow THN on Fb, Twitter and LinkedIn to read a lot more exceptional material we publish.
Some parts of this article are sourced from:
thehackernews.com

 How Should the Service Desk Reset Passwords?
How Should the Service Desk Reset Passwords?