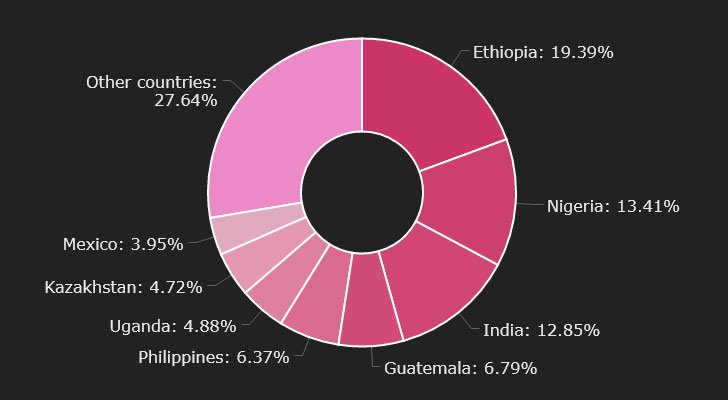
Cryptocurrency end users in Ethiopia, Nigeria, India, Guatemala, and the Philippines are currently being qualified by a new variant of the Phorpiex botnet named Twizt that has resulted in the theft of virtual cash amounting to $500,000 over the previous a single year.
Israeli security agency Look at Level Research, which thorough the assaults, reported the hottest evolutionary model “allows the botnet to work successfully with no energetic [command-and-control] servers,” introducing it supports no less than 35 wallets affiliated with unique blockchains, which includes Bitcoin, Ethereum, Sprint, Dogecoin, Litecoin, Monero, Ripple, and Zilliqa, to aid crypto theft.
Phorpiex, if not acknowledged as Trik, is known for its sextortion spam and ransomware strategies as properly as cryptojacking, a scheme that leverages the targets’ equipment this kind of as pcs, smartphones, and servers to secretly mine cryptocurrency without having their consent or awareness.
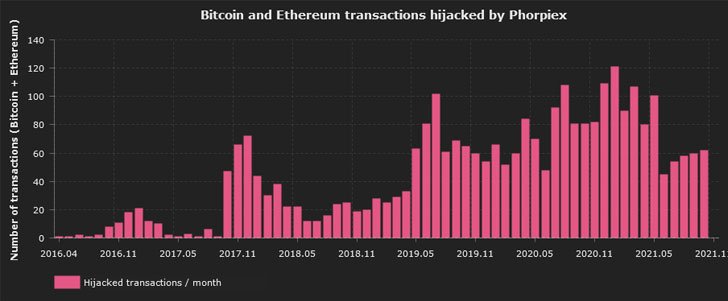
It’s also notorious for its use of a strategy identified as cryptocurrency clipping, which includes stealing cryptocurrency in the course of action of a transaction by deploying malware that automatically substitutes the meant wallet handle with the threat actor’s wallet address. Examine Position mentioned it identified 60 distinctive Bitcoin wallets and 37 Ethereum wallets applied by Phorpiex.
Even though the botnet operators shut down and set its source code for sale on a dark web cybercrime forum in August 2021, the command-and-command (C&C) servers resurfaced a mere two months later to distribute Twizt, a beforehand undiscovered payload that can deploy extra malware and operate in peer-to-peer manner, hence eliminating the have to have for a centralized C&C server.
The clipping feature also arrives with an extra advantage in that, as soon as deployed, it can function even in the absence of any C&C servers and siphon money from victims’ wallets. “This indicates that each of the infected computer systems can act as a server and deliver instructions to other bots in a chain,” Examine Point’s Alexey Bukhteyev said in a report. “The emergence of this sort of options indicates that the botnet might turn out to be even additional secure and hence, additional risky.”
Phorpiex-contaminated bots have been spotted in 96 nations around the world, topped by Ethiopia, Nigeria, and India. The botnet is also believed to have hijacked around 3,000 transactions with a full value of roughly 38 Bitcoin and 133 Ether. It is really, nonetheless, value noting that the botnet is developed to halt its execution ought to the contaminated system’s locale be defaulted to Ukraine, suggesting that the botnet operators are from the East European country.
“Malware with the features of a worm or a virus can continue to spread autonomously for a very long time without the need of any further involvement by its creators,” Bukhteyev said. “In the past yr, Phorpiex received a significant update that reworked it into a peer-to-peer botnet, allowing it to be managed without the need of having a centralized infrastructure. The C&C servers can now alter their IP addresses and issue instructions, hiding among the botnet victims.”
Observed this write-up appealing? Adhere to THN on Fb, Twitter and LinkedIn to go through much more exclusive information we write-up.
Some parts of this article are sourced from:
thehackernews.com


 Comcast won't enforce Northeast data caps until 2023 at the earliest
Comcast won't enforce Northeast data caps until 2023 at the earliest