Cybersecurity researchers on Monday disclosed a new wave of ongoing assaults exploiting a number of vulnerabilities to deploy Mirai variants on compromised techniques.
“Upon effective exploitation, the attackers attempt to obtain a malicious shell script, which has even further an infection behaviors these kinds of as downloading and executing Mirai variants and brute-forcers,” Palo Alto Networks’ Unit 42 Menace Intelligence Team mentioned in a produce-up.
The rash of vulnerabilities getting exploited contain:
- VisualDoor — a SonicWall SSL-VPN remote command injection vulnerability that arrived to gentle before this January
- CVE-2020-25506 – a D-Backlink DNS-320 firewall remote code execution (RCE) vulnerability
- CVE-2021-27561 and CVE-2021-27562 – Two vulnerabilities in Yealink Machine Administration that let an unauthenticated attacker to operate arbitrary commands on the server with root privileges
- CVE-2021-22502 – an RCE flaw in Micro Aim Procedure Bridge Reporter (OBR), impacting version 10.40
- CVE-2019-19356 – a Netis WF2419 wi-fi router RCE exploit, and
- CVE-2020-26919 – a Netgear ProSAFE Plus RCE vulnerability
Also provided in the combine are three earlier undisclosed command injection vulnerabilities that had been deployed from not known targets, 1 of which, according to the scientists, has been noticed in conjunction with MooBot.
The attacks are explained to have been detected above a month-prolonged period starting off from February 16 to as latest as March 13.
Regardless of the flaws employed to obtain profitable exploitation, the attack chain will involve the use of wget utility to down load a shell script from the malware infrastructure which is then utilized to fetch Mirai binaries, a infamous malware that turns networked IoT devices jogging Linux into remotely managed bots that can be employed as portion of a botnet in significant-scale network assaults.
Apart from downloading Mirai, added shell scripts have been noticed retrieving executables to facilitate brute-force attacks to split into vulnerable equipment with weak passwords.
“The IoT realm stays an effortlessly obtainable focus on for attackers. A lot of vulnerabilities are pretty uncomplicated to exploit and could, in some scenarios, have catastrophic repercussions,” the researcher said.
New ZHtrap Botnet Traps Victims Working with a Honeypot
In a linked growth, scientists from Chinese security firm Netlab 360 discovered a new Mirai-centered botnet named ZHtrap that tends to make use of a honeypot to harvest additional victims, when borrowing some features from a DDoS botnet known as Matryosh.
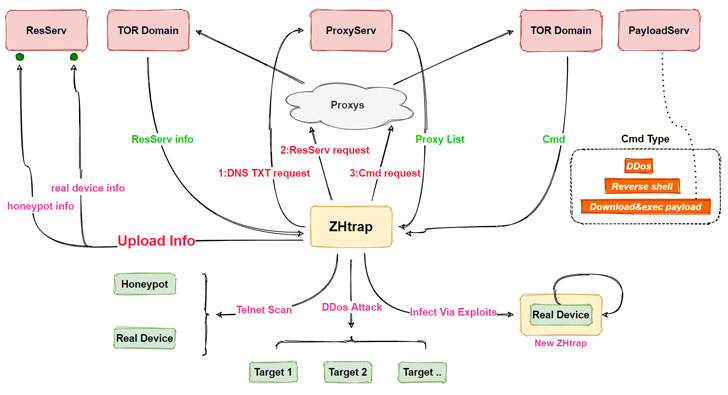
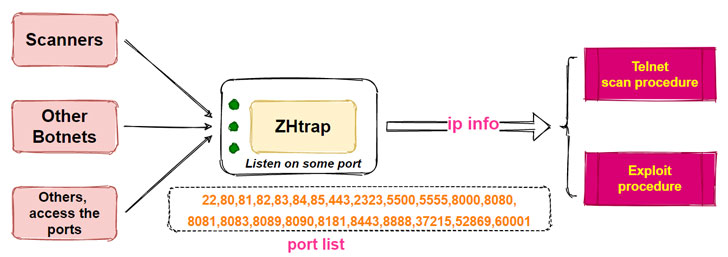
When honeypots commonly mimic a focus on for cyber criminals so as to acquire edge of their intrusion tries to glean more data about their modus operandi, the ZHtrap botnet takes advantage of a very similar strategy by integrating a scanning IP selection module for accumulating IP addresses that are used as targets for even further worm-like propagation.
It achieves this by listening on 23 designated ports and determining IP addresses that link to these ports, then working with the amassed IP addresses to examine them for 4 vulnerabilities to inject the payload –
- MVPower DVR Shell unauthenticated RCE
- Netgear DGN1000 Set up.cgi unauthenticated RCE
- CCTV DVR RCE impacting several vendors, and
- Realtek SDK miniigd Cleaning soap command execution (CVE-2014-8361)
“ZHtrap’s propagation utilizes four N-day vulnerabilities, the main perform is DDoS and scanning, although integrating some backdoor attributes,” the scientists reported. “Zhtrap sets up a honeypot on the contaminated device, [and] can take snapshots for the victim equipment, and disables the operating of new commands primarily based on the snapshot, as a result achieving exclusivity about the device.”
After it has taken in excess of the gadgets, ZHtrap takes a cue from the Matryosh botnet by using Tor for communications with a command-and-command server to down load and execute supplemental payloads.
Noting that the assaults commenced from February 28, 2021, the researchers stated ZHtrap’s capacity to turn infected devices into honeypots marks an “intriguing” evolution of botnets to facilitate finding a lot more targets.
“Several botnets implement worm-like scan propagation, and when ZHtrap’s honeypot port is accessed, its resource is most most likely a system that has been contaminated by a different botnet,” the scientists speculated about the malware’s authors. “This product can be infected, there must be flaws, I can use my scanning mechanism to scan again.This could be a very good probability that I can implant my bot samples, and then with the approach manage perform, I can have full command, is not that wonderful?”
Observed this short article fascinating? Follow THN on Fb, Twitter and LinkedIn to read through additional unique material we article.
Some parts of this article are sourced from:
thehackernews.com


 MoD Contractor Security Incidents Double in a Year
MoD Contractor Security Incidents Double in a Year