A week just after the US authorities issued an advisory about a “world-wide intelligence gathering mission” operated by North Korean condition-sponsored hackers, new results have emerged about the menace group’s spyware abilities.
The APT — dubbed “Kimsuky” (aka Black Banshee or Thallium) and considered to be lively as early as 2012 — has been now linked to as several as three hitherto undocumented malware, which include an details stealer, a tool outfitted with malware anti-analysis attributes, and a new server infrastructure with major overlaps to its more mature espionage framework.
“The group has a loaded and notorious history of offensive cyber functions all-around the environment, together with operations focusing on South Korean consider tanks, but more than the earlier handful of many years they have expanded their targeting to nations around the world such as the United States, Russia and several nations in Europe,” Cybereason researchers reported in an analysis yesterday.
Final week, the FBI and departments of Protection and Homeland Security jointly released a memo detailing Kimsuky’s techniques, procedures, and strategies (TTPs).
Leveraging spear-phishing and social engineering methods to attain the preliminary entry into sufferer networks, the APT has been regarded to particularly goal folks determined as specialists in many fields, believe tanks, the cryptocurrency market, and South Korean federal government entities, in addition to posing as journalists from South Korea to send out e-mails embedded with BabyShark malware.
In latest months, Kimsuky has been attributed to a number of strategies using coronavirus-themed email lures that contains weaponized Word files as their an infection vector to attain a foothold on sufferer devices and launch malware attacks.
“Kimsuky focuses its intelligence assortment functions on international coverage and national security issues relevant to the Korean peninsula, nuclear coverage, and sanctions,” the Cybersecurity and Infrastructure Security Company (CISA) mentioned.
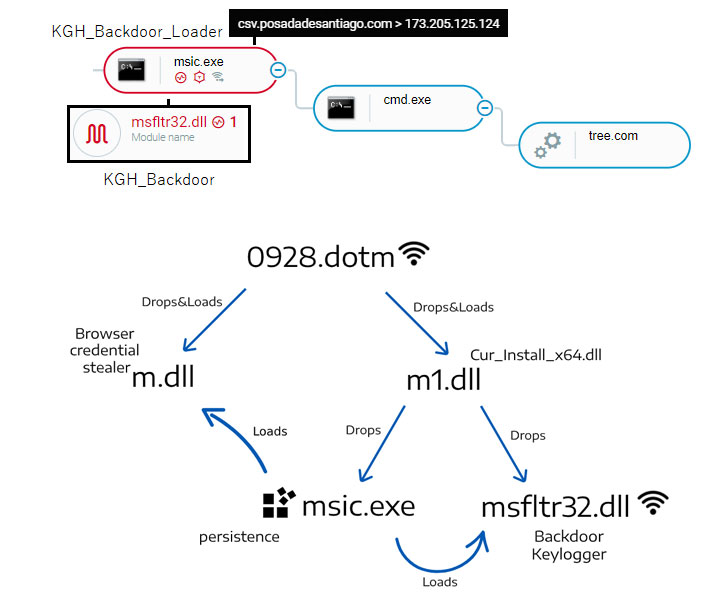
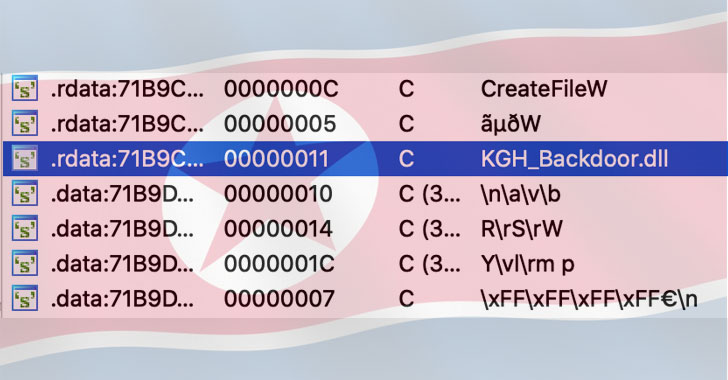
Now according to Cybereason, the menace actor has acquired new abilities by using a modular spy ware suite known as “KGH_SPY,” letting it to carry out reconnaissance of focus on networks, seize keystrokes, and steal delicate info.
Aside from this, the KGH_SPY backdoor can obtain secondary payloads from a command-and-handle (C2) server, execute arbitrary commands by means of cmd.exe or PowerShell, and even harvest credentials from web browsers, Windows Credential Manager, WINSCP and mail shoppers.
Also of note is the discovery of a new malware named “CSPY Downloader” that is created to thwart investigation and download added payloads.
And lastly, Cybereason researchers unearthed a new toolset infrastructure registered concerning 2019-2020 that overlaps with the group’s BabyShark malware employed to earlier focus on US-centered consider tanks.
“The menace actors invested endeavours in get to remain underneath the radar, by employing a variety of anti-forensics and anti-evaluation approaches which included backdating the generation/compilation time of the malware samples to 2016, code obfuscation, anti-VM and anti-debugging techniques,” the researchers stated.
“Though the id of the victims of this campaign stays unclear, there are clues that can recommend that the infrastructure specific organizations working with human rights violations.”
Observed this report interesting? Comply with THN on Fb, Twitter and LinkedIn to read through additional exceptional articles we post.
Some parts of this article are sourced from:
thehackernews.com

 iPhone Upgrade Program members can now lock in their iPhone 12 Pro Max and mini units
iPhone Upgrade Program members can now lock in their iPhone 12 Pro Max and mini units