Cybersecurity scientists on Thursday took the wraps off a new cyberespionage team that has been guiding a sequence of specific assaults versus diplomatic entities and telecommunication firms in Africa and the Middle East given that at minimum 2017.
Dubbed “BackdoorDiplomacy,” the marketing campaign entails concentrating on weak details in internet-uncovered devices these types of as web servers to execute a panoply of cyber hacking functions, like laterally moving across the network to deploy a customized implant referred to as Turian which is able of exfiltrating sensitive data stored in removable media.
“BackdoorDiplomacy shares methods, approaches, and processes with other Asia-primarily based groups. Turian very likely represents a up coming phase evolution of Quarian, the backdoor final observed in use in 2013 against diplomatic targets in Syria and the U.S,” explained Jean-Ian Boutin, head of danger investigation at Slovak cybersecurity organization ESET.
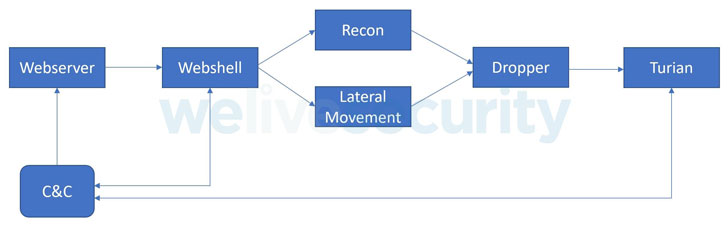
Engineered to focus on both equally Windows and Linux running systems, the cross-platform group singles out management interfaces for networking products and servers with internet-uncovered ports, very likely exploiting unpatched vulnerabilities to deploy the China Chopper web shell for original access, utilizing it to conduct reconnaissance and set up the backdoor.
Specific systems involve F5 Big-IP units (CVE-2020-5902), Microsoft Trade servers, and Plesk web hosting control panels. Victims have been determined in the Ministries of International Affairs of a number of African international locations, as effectively as in Europe, the Middle East, and Asia. On top of that, telecom companies in Africa and at the very least a person Center Japanese charity have also been hit.

“In every single scenario, operators utilized similar practices, techniques, and strategies (TTPs), but modified the applications made use of, even within just close geographic regions, very likely to make monitoring the team more tricky,” the scientists reported. BackdoorDiplomacy is also believed to overlap with earlier documented campaigns operated by a Chinese-talking team Kaspersky tracks as “CloudComputating.”
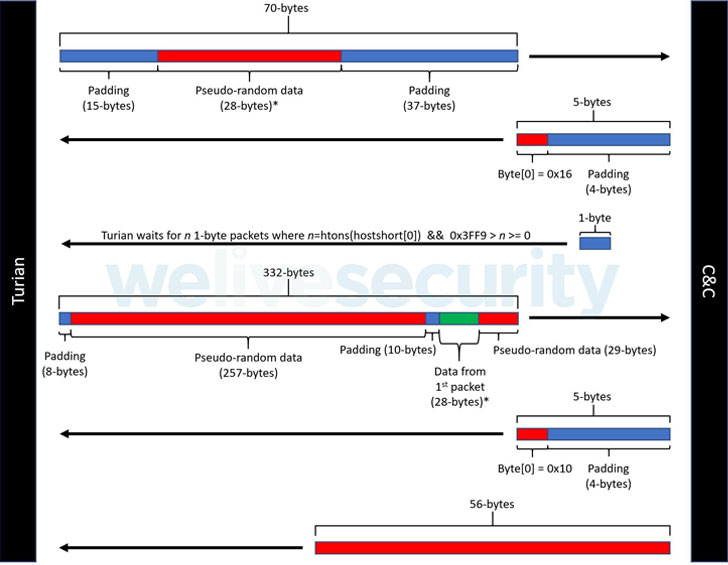
In addition to its options to collect procedure information and facts, just take screenshots, and have out file operations, ESET scientists reported Turian’s network encryption protocol is just about similar to that utilized by WhiteBird, a C++ backdoor operated by an Asia-based menace actor named Calypso, that was put in within diplomatic corporations in Kazakhstan and Kyrgyzstan, and throughout the similar timeframe as BackdoorDiplomacy.
Discovered this post interesting? Stick to THN on Facebook, Twitter and LinkedIn to read through much more special content we post.
Some parts of this article are sourced from:
thehackernews.com


 Apple AirPods Max headphones drop to their lowest price so far at Amazon
Apple AirPods Max headphones drop to their lowest price so far at Amazon