A formerly undocumented Android-centered distant accessibility trojan (RAT) has been located to use display screen recording functions to steal delicate info on the system, like banking qualifications, and open up the door for on-system fraud.
Dubbed “Vultur” owing to its use of Digital Network Computing (VNC)’s remote screen-sharing technology to get full visibility on focused consumers, the mobile malware was dispersed by using the official Google Engage in Retailer and masqueraded as an app named “Protection Guard,” attracting around 5000 installations. Banking and crypto-wallet applications from entities positioned in Italy, Australia, and Spain have been the most important targets.
“For the to start with time we are viewing an Android banking trojan that has display recording and keylogging as the principal technique to harvest login qualifications in an automated and scalable way,” researchers from ThreatFabric claimed in a write-up shared with The Hacker News.

“The actors chose to steer away from the typical HTML overlay development we typically see in other Android banking Trojans: this approach ordinarily involves a much larger time and effort expenditure from the actors to produce numerous overlays able of tricking the consumer. In its place, they selected to just history what is shown on the display, proficiently obtaining the identical conclude final result.”
Whilst banking malware such as MysteryBot, Grandoreiro, Banker.BR, and Vizom have customarily relied on overlay attacks — i.e., developing a wrong version of the bank’s login webpage and overlaying it on best of the authentic app — to trick victims into revealing their passwords and other essential private facts, evidence is mounting that menace actors are pivoting absent from this strategy.
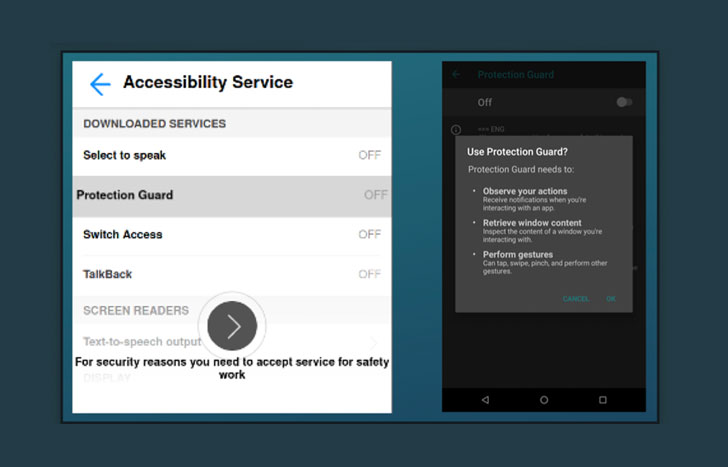
In a report published previously this week, Italian cybersecurity firm Cleafy uncovered UBEL, an updated variant of Oscorp, that was observed making use of WebRTC to interact with the compromised Android phone in genuine-time. Vultur adopts a very similar tactic in that it will take advantage of accessibility permissions to seize keystrokes and leverages VNC’s display recording attribute to stealthily log all functions on the phone, hence obviating the need to sign-up a new system and generating it complicated for financial institutions to detect fraud.
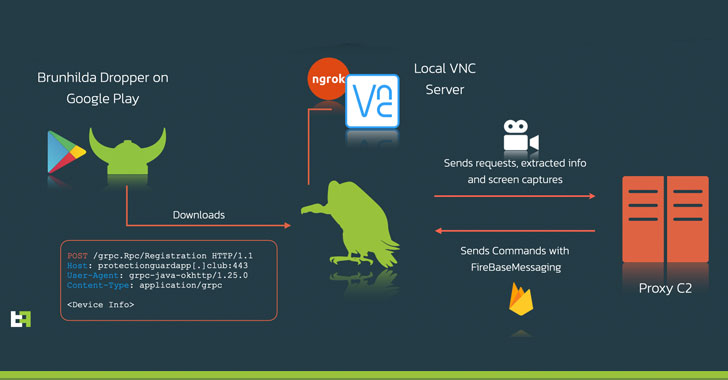
What’s far more, the malware employs ngrok, a cross-platform utility utilised to expose regional servers driving NATs and firewalls to the general public internet in excess of protected tunnels, to supply remote access to the VNC server managing locally on the phone. Also, it also establishes connections with a command-and-regulate (C2) server to obtain commands over Firebase Cloud Messaging (FCM), the benefits of which, including extracted facts and screen captures, are then transmitted back again to the server.

ThreatFabric’s investigation also related Vultur with one more perfectly-acknowledged piece of destructive software program named Brunhilda, a dropper that utilizes the Enjoy Retailer to distribute unique kinds of malware in what is actually called a “dropper-as-a-support” (DaaS) operation, citing overlaps in the source code and C2 infrastructure made use of to aid attacks.
These ties, the Amsterdam-primarily based cybersecurity solutions company said, show Brunhilda to be a privately working risk actor that has its possess dropper and proprietary RAT Vultur.
“The story of Vultur exhibits 1 extra time how actors shift from making use of rented Trojans (MaaS) that are offered on underground markets in direction of proprietary/private malware tailored to the requirements of this group,” the researchers concluded. “These assaults are scalable and automatic due to the fact the steps to carry out fraud can be scripted on the malware backend and sent in the form of commands sequence, creating it uncomplicated for the actor(s) to hit-and-run.”
Found this article interesting? Stick to THN on Fb, Twitter and LinkedIn to examine much more unique content material we post.
Some parts of this article are sourced from:
thehackernews.com

 Top 30 Critical Security Vulnerabilities Most Exploited by Hackers
Top 30 Critical Security Vulnerabilities Most Exploited by Hackers