
Although we are recovering from the worst pandemic, cyber threats have shown no signal of downshifting, and cybercriminals are nevertheless not quick of destructive and highly developed strategies to obtain their targets.
The Worldwide Menace Landscape Report suggests a drastic rise in sophisticated cyberattacks concentrating on digital infrastructures, corporations, and men and women in 2021. Threats can just take unique kinds with the intent to commit fraud and harm businesses and individuals. Ransomware, DDoS attacks, phishing, malware, and man-in-the-middle assaults stand for the biggest menace to companies nowadays.
When new threats arise, attackers choose edge of them – having said that, most organizations are only knowledgeable of the existing threats.
Organizations wrestle to address these threats due to their resource sophistication and their lack of comprehending of evolving danger landscapes. For these reasons, businesses require visibility on the sophisticated threats in particular targeting their infrastructure. This post will outline the evolution in the cyber threat landscape 2021.
Evolving Risk Landscape – Locate Out What You Never Know
1 — Ransomware
Ransomware is even now a popular and evolving cyber security danger with quite a few remarkably publicized incidents. Ransomware incidents have an effect on corporations, enterprises, and individuals ensuing in money decline, operational disruptions, and facts exfiltration. Compromise via internet-experiencing vulnerabilities & misconfigurations, third get-togethers & managed assistance vendors, Remote Desktop Protocol (RDP) and phishing e-mails stay the most widespread infection vectors.
The prevalence of extortion schemes has amplified from solitary to many techniques through 2021. Immediately after initially encrypting delicate information and facts from the sufferer and threatening to expose it publicly unless a ransom is paid out, attackers are now targeting the victim’s associates and consumers for ransom to optimize their earnings.
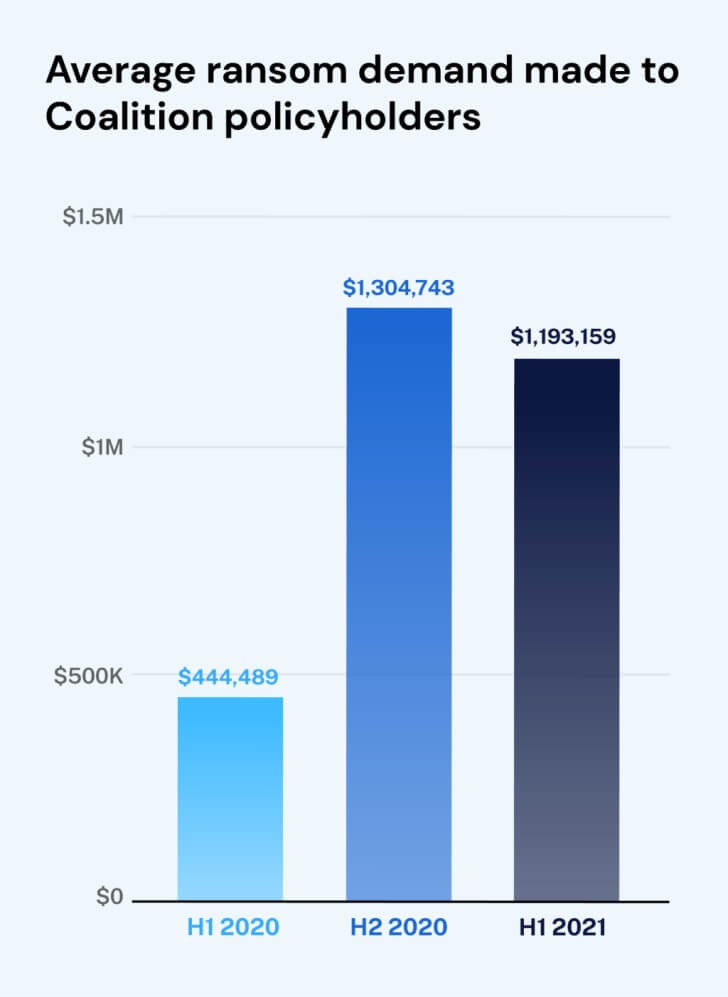
New investigation from Coalition uncovered that there was a 170% boost in the common ransom need in the initial 50 % of 2021 as opposed to last 12 months.
 Impression supply: venturebeat
Impression supply: venturebeat
It is possible to strike $100 million in 2022 – in accordance to the ENISA Threat Landscape 2021.
Furthermore, cryptocurrency will become the selection of pay-out system because it promises a secure, speedy, and anonymous channel for revenue transactions. Also, attackers shifted from Bitcoin to Monero as their decision due to its enhanced anonymity.
Tips to avert becoming a target:
- Security consciousness education
- Use secure sites
- Protection-in-depth cybersecurity approach
- Vulnerability assessment & penetration screening
2 — Cryptojacking
Yet another attack craze in 2021 is cryptojacking, which is connected with the expanding instability in the cryptocurrency industry. Given the anonymity of cryptocurrencies, it has grow to be a easy and attractive means of trade by attackers. In this attack, cybercriminals deploy concealed cryptojacking software on to the target’s equipment, which steals from a cryptocurrency wallet. Siloscape, a new malware, which emerged in June 2021 targets Windows containers and creates destructive containers, loads cryptocurrency miners, which establish and steal cryptocurrency.
Recommendations to counteract cryptojacking:
- Put into action web filters and blacklist IP addresses from cryptomining IP pools
- Produce patches towards well-regarded exploits
- Carry out a robust vulnerability administration application
3 — Information Breaches
Delicate data being stolen from businesses or consumers is almost nothing new, but how menace actors strategy it has advanced. Just as companies embrace new systems to survive in the digital landscape, threat actors also harness innovative solutions to exploit assaults – Deepfake technology, for instance.
Though it is really not a new principle, it has evolved considerably. With MI and AI, Deepfake technology allows the electronic creation of an individual’s likeness, which can then be utilised to impersonate the target. AI and ML instruments make it possible to make synthetic versions of any voice or any video.
Cybercube’s security scientists alerted that deep fake audio and online video written content could become a significant cyber danger to businesses globally. Also, the widespread destruction affiliated with this pretended content is predicted to enhance in the coming yrs. It is also envisioned that the enhanced dependence on movie-dependent communication is the significant factor that motivates attackers to concentrate far more on Deepfake technology.
Tips for Deepfake Checking and Removing:
- Improved electronic archiving to identify the fake movie and fake voice clips
- Employ Content Authenticity Initiative to validate the creator as effectively as origin of information
4 — Botnets
Newer botnets carry on to emerge as aged types preserve reworking to sidestep the current security remedies. This is due to the fact cyber-criminals see a new paradigm with botnets-as-a-services where bonnets can be leased/marketed to corporations or men and women for nefarious makes use of and economical added benefits.
Moreover, the existence of botnets in the cloud and mobile natural environment proposes a new chance that they could shortly be in a position to study and exploit the weakness on their have in the designs of person interactions. The elevated adoption of IoT and the deficiency of security when they are developed as effectively as deployed provides an additional possible frontier for botnet proliferation.
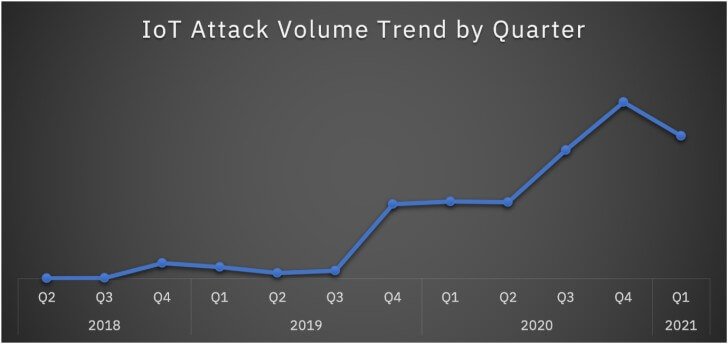
A recent report unveiled there is a 500% increase in over-all IoT attacks by well known IoT botnets like Mirai and Mozi.
 Graphic source: Security Intelligence
Graphic source: Security Intelligence
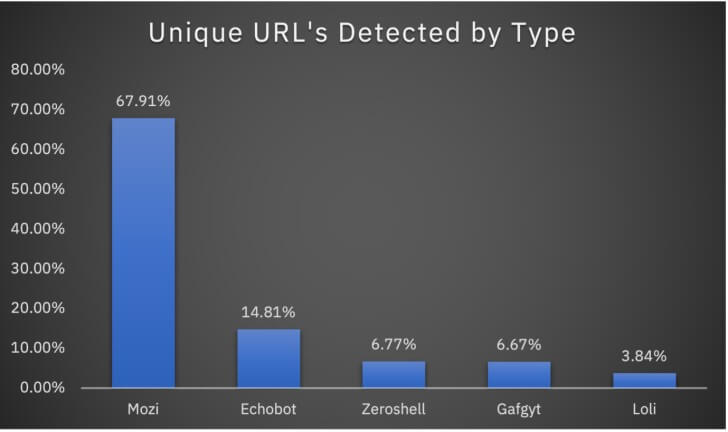
In 2020, the Mozi botnet attackaccounted for 89% of the IoT attacks – in accordance to X-Drive study. In addition to Mozi, various other botnets proceed to concentrate on the IoT landscape. Ecobot, Zeroshell, Gafgyt, and Loli are four notable botnets impacting businesses all over the globe.
 Picture resource: Security Intelligence
Picture resource: Security Intelligence
Suggestions to combat again:
- Use penetration screening
- Adjust your default IoT location when installing any new product
- Employ a strong patch management application
- Apply helpful bot security and mitigation strategy
The Massive Photograph
New cyber threats are being detected all the time, and they have the prospective to affect any functioning procedure, together with Linux, Windows, iOS, Mac OS, and Android. Additionally, new threats vectors are evolving thanks to probable vulnerabilities in the continual adoption of distant performing and a growing quantity of IoT devices remaining connected.
This cyber threat landscape evolution has pressured enterprises to improve their vulnerability administration method, security tools, processes, and competencies to stay ahead. Indusface AppTrana, a absolutely managed Web Application and API security (WAAP)addresses these problems and speeds up risk detection and reaction.
If you want to be proactive and actionable in preserving your info, continue to be knowledgeable of the new cyber security threat landscape!
Uncovered this article intriguing? Comply with THN on Fb, Twitter and LinkedIn to examine far more distinctive content material we write-up.
Some parts of this article are sourced from:
thehackernews.com


 Apple's second-generation AirPods drop to $89 ahead of Black Friday
Apple's second-generation AirPods drop to $89 ahead of Black Friday