Several botnets are targeting thousands of publicly uncovered and still unpatched Oracle WebLogic servers to deploy crypto miners and steal delicate info from contaminated units.
The assaults are getting goal at a not too long ago patched WebLogic Server vulnerability, which was released by Oracle as part of its October 2020 Critical Patch Update and subsequently all over again in November (CVE-2020-14750) in the variety of an out-of-band security patch.
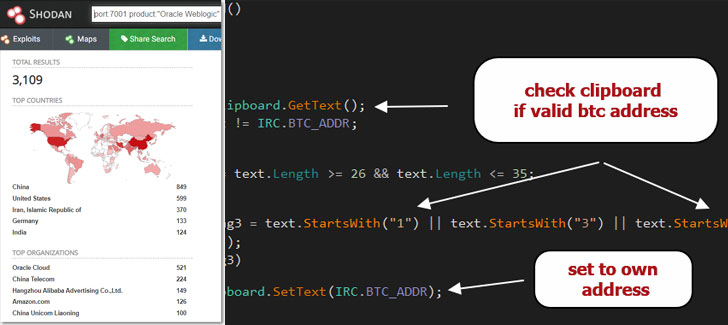
As of creating, about 3,000 Oracle WebLogic servers are accessible on the Internet-primarily based on stats from the Shodan look for motor.
Oracle WebLogic is a platform for producing, deploying, and operating company Java apps in any cloud setting as well as on-premises.
The flaw, which is tracked as CVE-2020-14882, has a CVSS rating of 9.8 out of a maximum score of 10 and influences WebLogic Server variations 10.3.6.., 12.1.3.., 12.2.1.3., 12.2.1.4., and 14.1.1…
Though the issue has been addressed, the release of proof-of-thought exploit code has manufactured susceptible Oracle WebLogic occasions a worthwhile target for risk actors to recruit these servers into a botnet that pilfers critical info and deploy 2nd stage malware payloads.
According to Juniper Menace Labs, operators of the DarkIRC botnet are exploiting this RCE vulnerability to spread laterally throughout the network, download information, record keystrokes, steal credentials, and execute arbitrary instructions on compromised devices.
The malware also acts as a Bitcoin clipper that enables them to alter bitcoin wallet addresses copied to the clipboard to the operator’s bitcoin wallet deal with, allowing for the attackers to reroute Bitcoin transactions.
What is a lot more, a menace actor by the identify of “Freak_OG” has been providing the DarkIRC malware now on hacking forums for $75 considering that August.
But it is really not just DarkIRC that is exploiting the WebLogic Server vulnerability. In a individual campaign—spotted by ‘0xrb’ and in depth by researcher Tolijan Trajanovski—evidence has emerged of a botnet that propagates through the WebLogic flaw to deliver Monero cryptocurrency miner and Tsunami binaries.
Besides applying SSH for lateral movement, the botnet has been uncovered to accomplish persistence by means of cron positions, kill competing mining equipment, and even uninstall Endpoint detection and reaction (EDR) instruments from Alibaba and Tencent.
It really is encouraged that customers apply the October 2020 Critical Patch Update and the updates involved with CVE-2020-14750 as soon as probable to mitigate pitfalls stemming from this flaw.
Oracle has also supplied guidelines to harden the servers by preventing external access to inside apps available on the Administration port.
Discovered this short article intriguing? Adhere to THN on Facebook, Twitter and LinkedIn to examine a lot more exclusive material we submit.
Some parts of this article are sourced from:
thehackernews.com


 Amazon WOW Salary Days sale: Discount on appliances, TVs and more
Amazon WOW Salary Days sale: Discount on appliances, TVs and more